 This round of independent ATT&CK Evaluations for enterprise cybersecurity solutions emulated two sophisticated threat groups, Wizard Spider and Sandworm.
This round of independent ATT&CK Evaluations for enterprise cybersecurity solutions emulated two sophisticated threat groups, Wizard Spider and Sandworm.
Wizard Spider is a financially motivated criminal group that has been conducting ransomware campaigns since August 2018 against a variety of organizations, ranging from major corporations to hospitals. Sandworm is a destructive Russian threat group that is known for launching the NotPetya ransomware attacks that wreaked havoc in 2017.
These two threat actors were chosen based on their complexity, relevancy to customer organizations, and how well MITRE Engenuity’s staff can fittingly emulate the adversary for a real-world test that organizations can trust.
Delivering the highest visibility of threats
Sophos is proud to share that Intercept X demonstrated a world-class ability to prevent and detect advanced attacks, including Wizard Spider and Sandworm. Specifically, Intercept X blocked both simulated attacks and detected each of the major steps of the two attack scenarios.
“The challenge of protecting your organization against real-world cyberthreats is a demanding effort in precision and scale. Providing the highest level of context to a defender is key to improving the speed at which you can identify and respond to attacker tactics, techniques, and procedures (TTPs). Adversaries continuously adapt and evolve their toolsets and activity to seize new opportunities, evade detection and try to stay one step ahead of security teams. For that reason, we’re pleased to be recognized in the MITRE Engenuity evaluations, which focus on the actual TTPs of two assertive and modern-day attackers,” said Joe Levy, Sophos Chief Technology and Product Officer.
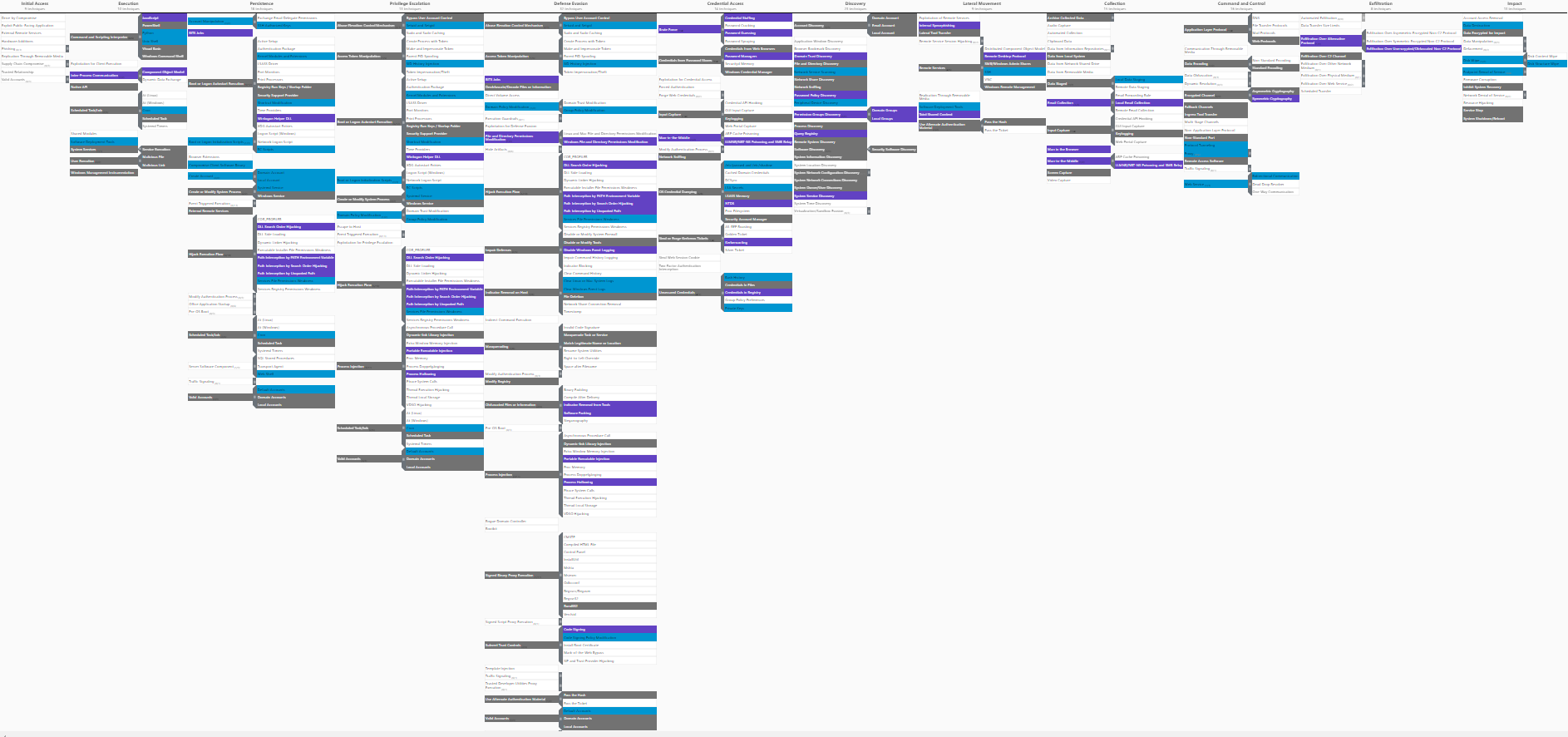
You can view the in-scope techniques used in the evaluation in the ATT&CK Navigator by checking out the layer file we made available here, and Sophos’ results in detecting them here.
Stopping threats faster
“We’re very pleased with the way MITRE’s evaluation showcases the threat detection strength of Sophos Intercept X. Every day, this enables our customers to deter more active attacks earlier in the attack lifecycle, and to reduce the impact of costly threats like ransomware,” adds Levy. Preventing a single ransomware incident, as simulated in the ATT&CK Evaluations, could result in saving millions of dollars, not to mention the potential collateral damage, simply by stopping attacks before they culminate into something more devious.
As President Biden releases a statement that Russian threat groups, like those responsible for Sandworm, may be shifting towards cyber-offensive action against Western organizations and infrastructure, it’s important for organizations to optimize prevention. An important step is to reduce the attack surface, removing opportunities for attackers to breach your organization. Some examples of how Sophos achieves this is by:
- Blocking potentially unwanted applications
- Blocking malicious or suspicious websites based on content or URL rating
- Controlling which applications are allowed to run in the organization
- Controlling which devices are allowed on the organization’s network or able to access cloud assets
- Locking down server configurations in a single click
The next step is to prevent attacks from running, using layered protection technologies to stop both the threats and the tactics attackers use, including:
- Behavioral detection and prevention based on known-adversarial and anomalous activities
- Artificial intelligence (AI) models to assign risk scores to file artifacts, including those never-before-seen
- Behavior-based anti-ransomware protection for both local and remote systems
- Exploit prevention that stops the techniques attackers use, protecting against a broad set of attacks, including those that leverage previously unknown malware
Last year’s Kaseya attack highlights how important the combination of prevention and detection is — by the time the attack was detected, it was too late, and the files were encrypted. Not a single Sophos customer with our next-gen endpoint protection correctly deployed had their files encrypted in that attack.
Minimizing the time to detect and respond
Optimizing prevention like this minimizes time to detect and respond in the face of real-world threats and enables defenders to focus on fewer, more accurate detections.
Sophos Intercept X with XDR, by achieving the highest context rating for the majority of detections in the evaluation, demonstrated how it enables you to streamline the whole investigation and response process. Our intuitive console makes it easy with a rich set of pre-defined, categorized Threat Hunting and Investigation queries in several categories including MITRE ATT&CK oriented.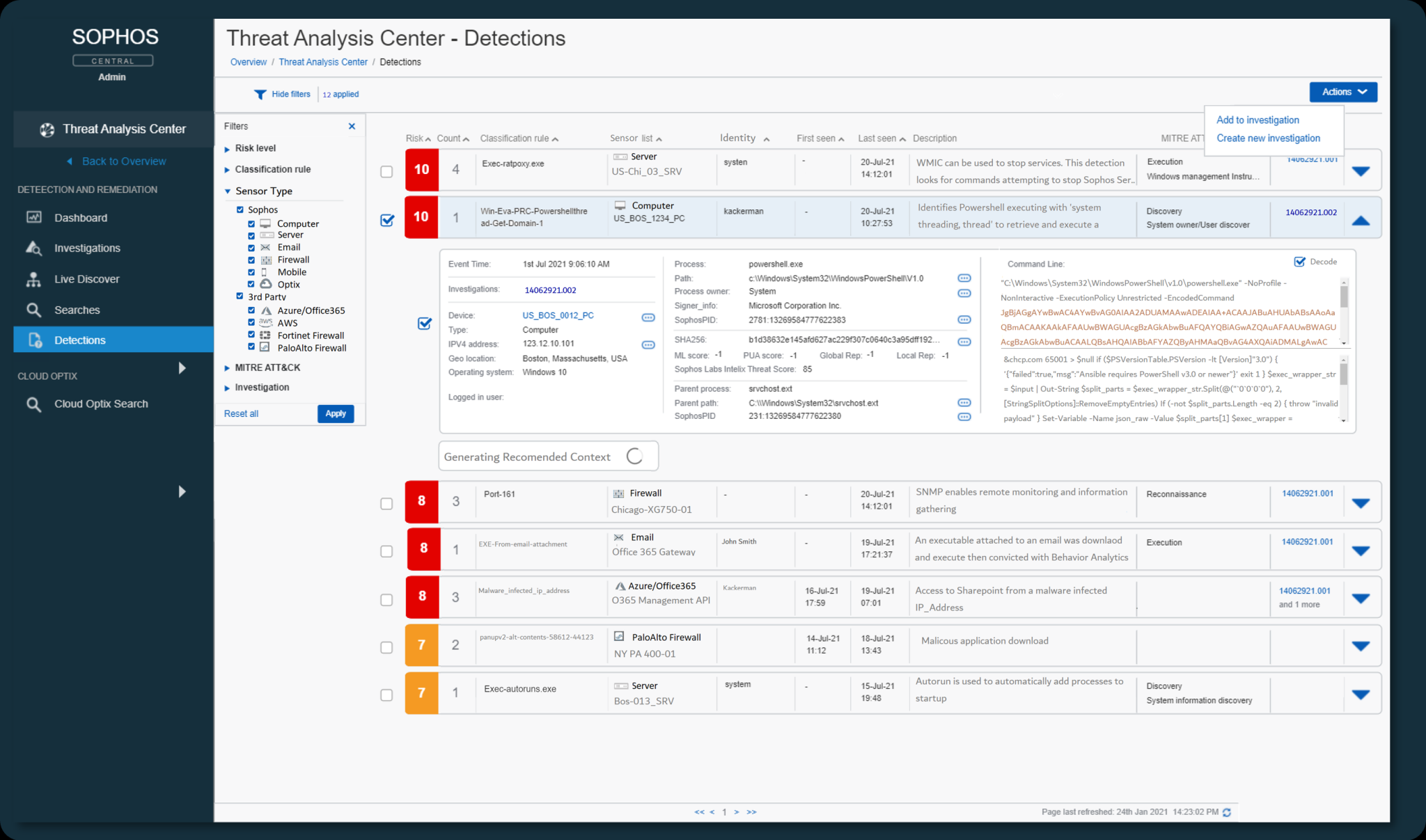 To bring this to life, I’d like to share data from Sophos Managed Threat Response (MTR), our 24/7/365 managed detection and response (MDR) service which today serves well over 8,500 Sophos Intercept X customers.
To bring this to life, I’d like to share data from Sophos Managed Threat Response (MTR), our 24/7/365 managed detection and response (MDR) service which today serves well over 8,500 Sophos Intercept X customers.
Customers enrolled in our service are seeing mean time to detect (MTTD) attacks under one minute. Enriched investigation techniques result in a mean time to investigate (MTTI) of 25 minutes.
Our human-led investigations leverage the superior detection context identified by MITRE, enabling us to achieve quicker and more accurate response. The result is a mean time to resolution (MTTR) of just 12 minutes, or a total time from detecting the threat to resolving it of just under 38 minutes.
Delivering real-world results
Our goal at Sophos is to help our customers prevent, detect, and respond to security incidents faster, enabling you to achieve better security outcomes.
We are committed to testing Sophos Intercept X with a wide range of leading testing providers like MITRE Engenuity, as well as soliciting reviews from the organizations we protect every day. The results speak for themselves: Sophos consistently delivers industry-leading protection, was named the highest rated and most reviewed vendor in Gartner Peer Insights™ Customer’s Choice for Endpoint Protection Platforms, and was named best Enterprise Endpoint Protection by SE Labs.
To learn more and discuss how we can help with your security challenges, visit our website and speak with a member of the team.
If you need immediate assistance to contain, neutralize, and investigate an active threat, you can contact Sophos Rapid Response for support 24/7.

Leave a Reply