The world of malicious software is a mirror universe to the world of legitimate software.
Some of the software is very good (at being bad) and some of the software is very bad (which is good), and underneath it all is an army of people: software developers, sales and marketing people, distributors, support…
And, as new research from SophosLabs reminds us, where people go, human interest and human failings go too.
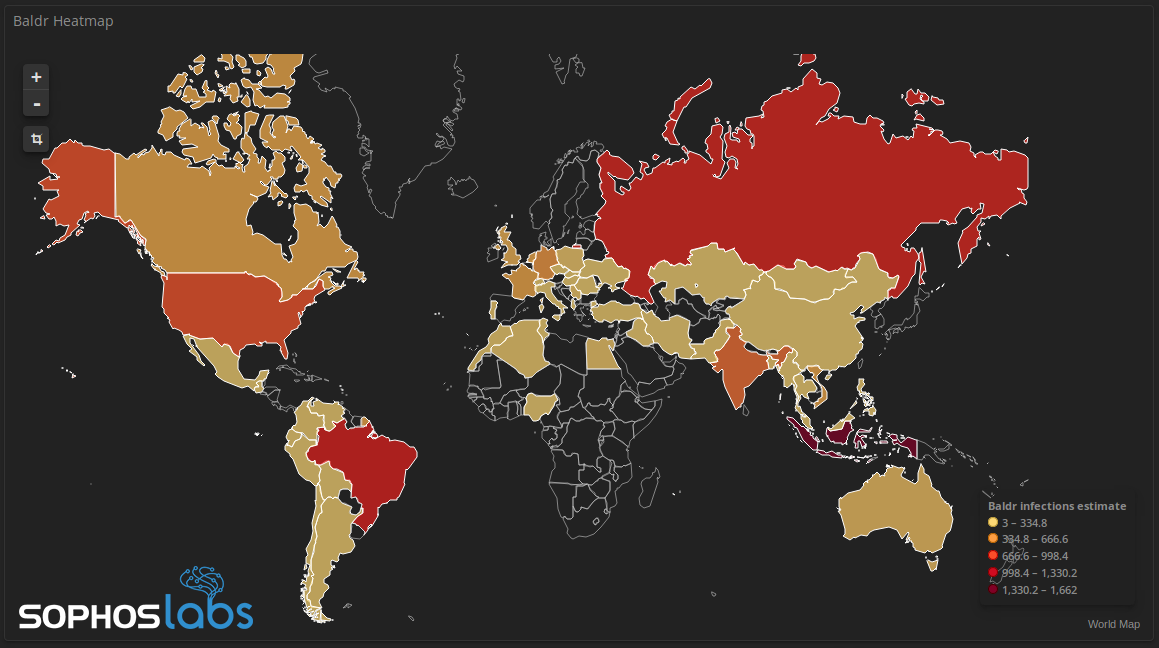
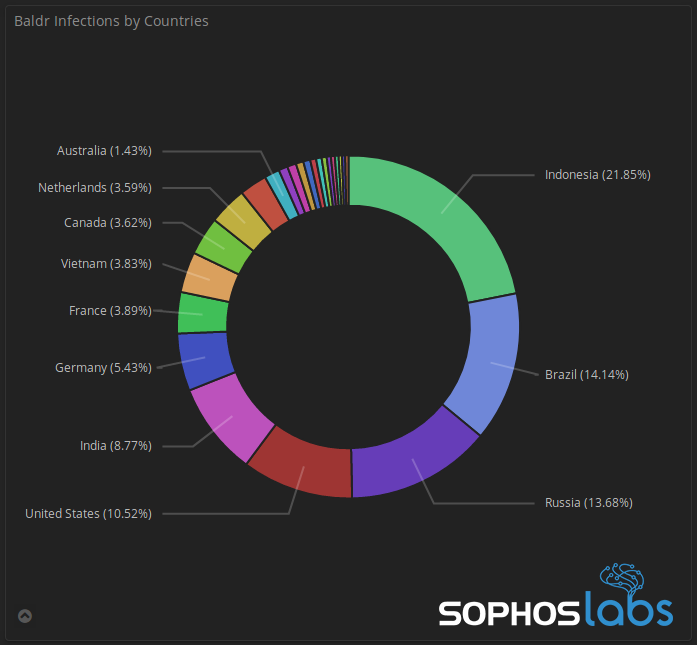
The research in question concerns Baldr, an up-and-comer in the world of illegal software that SophosLabs’ has been tracking closely since January.
In simple terms, Baldr is a password stealer, although in reality it’s more of an indiscriminate malware thief with an interest in anything it can carry away. It would steal your watch if it could.
We know this, thanks to our story’s first bunch of humans. The venerable researchers of SophosLabswhose job it is to roll up their sleeves and figure out what malware does and how to stop it, after their algorithms have taken things as far as they can.
In the case of Baldr, the sleeve rolling started early. In an attempt to frustrate malware analysts, it hides its secrets under layers of obfuscation, so the SophosLabs boffins had to flay it by hand.
Baldr employs an excessive number obfuscation layers (at last count, 9) that thwarts static code analysis. Can we hack it? (Yes we can!)
What their analysis reveals is a rapacious voyeur.
If you’re unlucky enough to get it on your system, the malware will grab anything that looks like it might contain useful or valuable data.
How it works
It begins by creating a profile of your system: grabbing a boat load of information about the computer it’s on such as the CPU model, operating system, system language, screen resolution, installed programs, hat size and favourite colour (OK, it doesn’t capture the last two but it would if it could).
Then it ransacks your web browsers, relieving them of saved credentials, autocomplete information, credit card information, cookies, the domains you’ve visited and your browsing history.
After that it hoovers up any FTP logins it finds, and then it steals credentials from your computer’s instant messaging clients and VPNs.
If you’ve got any cryptocurrency lying around, it knows how to plunder it from a range of different wallets. And then it takes a screenshot of your desktop, because – why not?
It stuffs all the data into an encrypted file and POSTs it via HTTP to a C2 (Command and Control) server before deleting itself in an effort to cover its tracks.
It can even get worse..
As if that wasn’t all bad enough, Baldr can also be used to download other malware from its C2 server.
Baldr’s malware relationship status is: Complicated. For example, we recently observed ransomware loading Baldr onto a victim’s machine … We’ve also logged instances of Arkei or Megumin dropping Baldr during an infection, and Baldr dropping Megumin.
Our knowledge of Baldr and its C2 infrastructure was assisted, unintentionally, by our story’s second bunch of humans: Baldr’s customers.
Demonstrating that cloud data leaks are a game that anyone can play, their sloppy server admin skills gave SophosLabs a grandstand view of the malware’s back end.
Some of Baldr’s customers were careless with their operational security, and left the C2 package accessible in an open directory on the C2 server, so we downloaded a few to take a closer look.
With a copy of the C2 code, the folks in the labs were able to learn more about the malware authors’ strategy and motivations. They also learned something about some of the Baldr developers’ coding skills, finding sufficient security failings to conclude that the admin console is “vulnerable to a number of attacks.”
And just in case anyone is labouring under the illusion that there’s honour among thieves, it seems they aren’t the only people to have noticed.
We observed Baldr C2 servers that had been repeatedly taken over with web shells by other threat actors, who have been investigating and taking advantage of these panels.
Further insight was provided by crooks who cut out the middle man and just pwned themselves.
In rare circumstances, the malware buyers also become victim to their own stealer, either by mistake or for testing purposes they execute the malware sample on their own machine.
Sadly though, Baldr itself is no joke and there are enough Baldr operators who know what they’re doing to represent a significant threat. This, in spite of the efforts of the people around Baldr:
The makers of Baldr appear to have had a falling out with one of their larger distributors, and as this story went to press, the primary distributor appears to have stopped working with the Baldr developers. Based on the nature of this type of criminal enterprise, we suspect that Baldr will once again be offered for sale, and the distribution issues are only temporary.
Leave a Reply