In the first chapter of this series, we provided an overview of the hidden sub-economy of scammers who scam scammers, and in the second we examined the wide variety of scams and tricks within it.
The third chapter is a little different. It covers a specific scam we uncovered during our research, which we highlight because of its scale, levels of coordination, and apparent success.
The curious case of twenty fake marketplaces
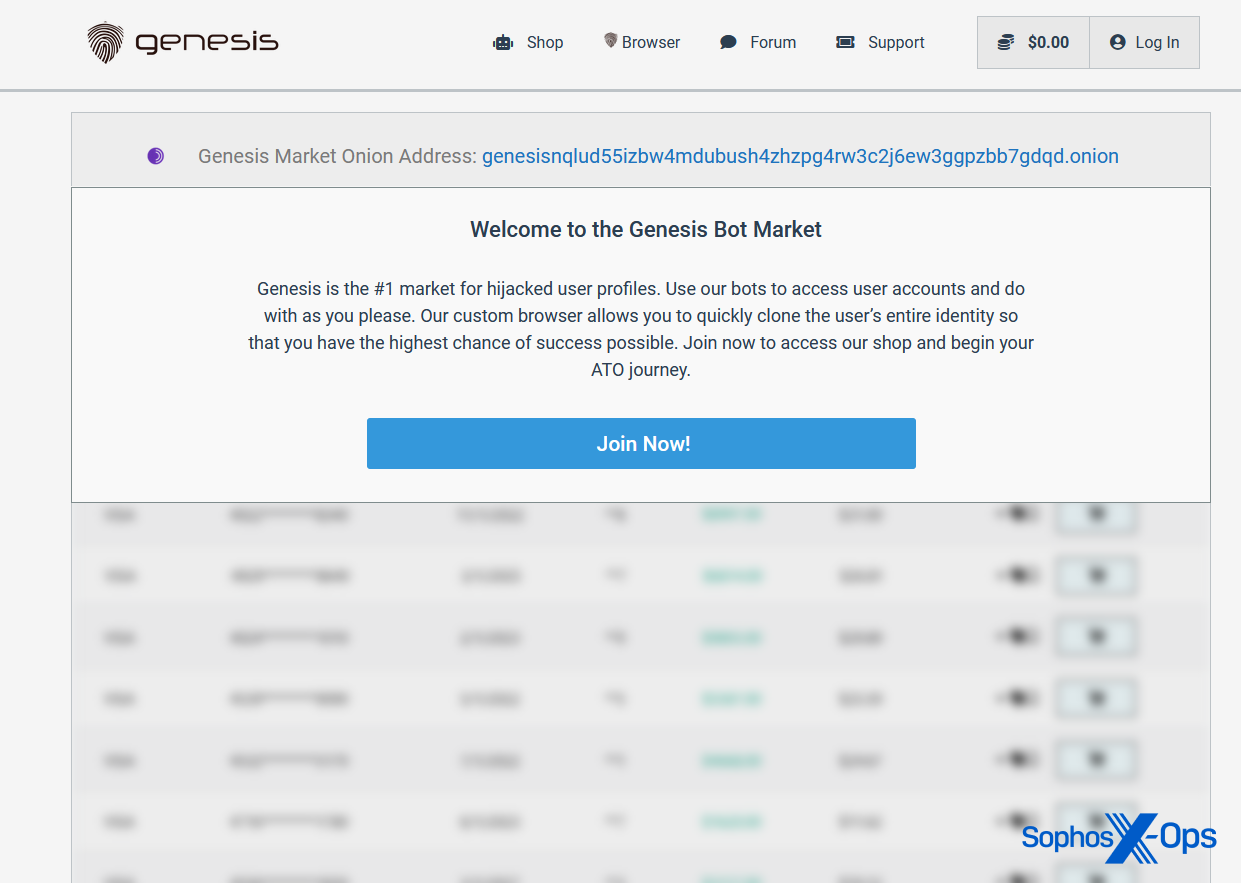
During our research into Genesis Market, we found a clearnet site (genesismarket[.]org) that looked nothing like the genuine Genesis Market site but appeared prominently in search engine results.
Figure 1: The fake Genesis Market site
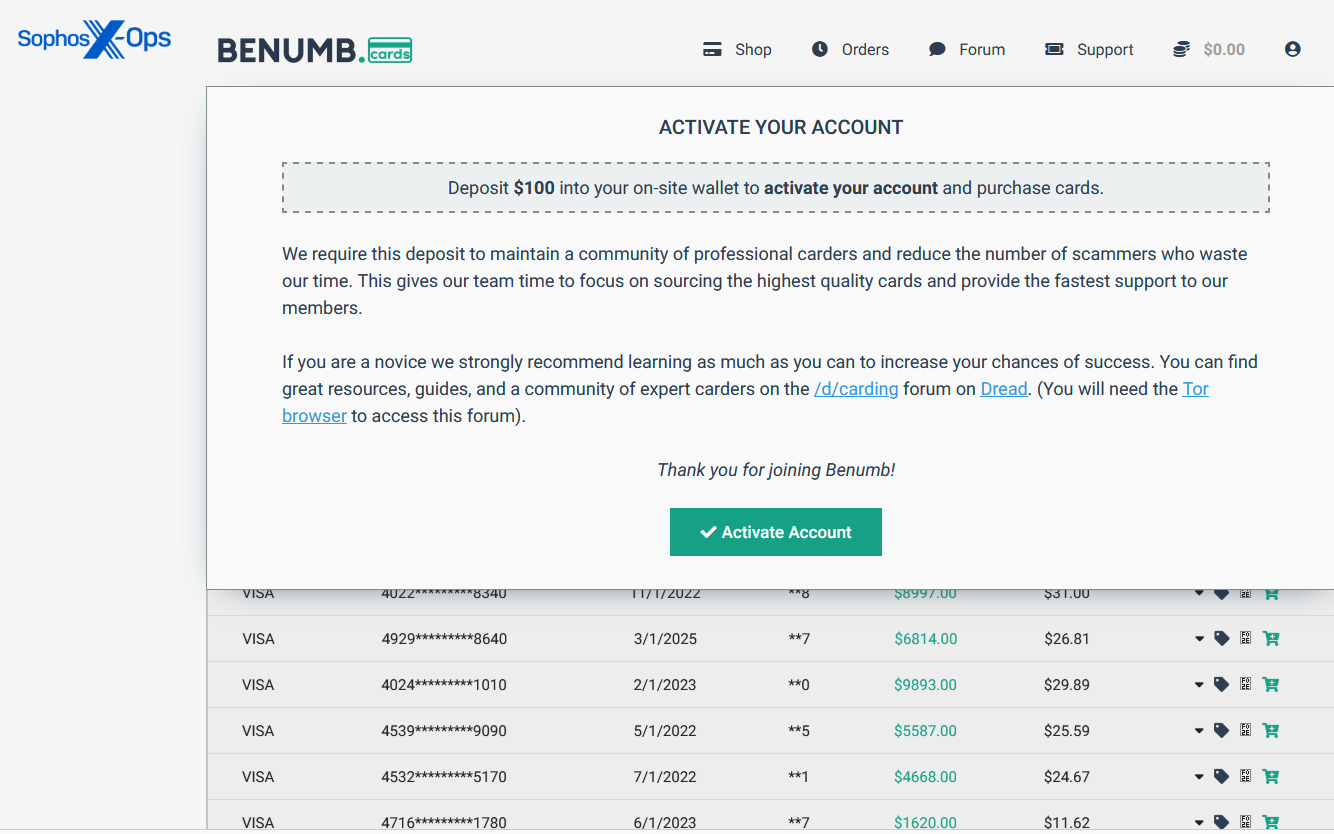
We quickly determined that the site didn’t seem to be connected to the genuine Genesis Market. For one thing, the site demands a $100 USD deposit, whereas the real Genesis is invitation-only.
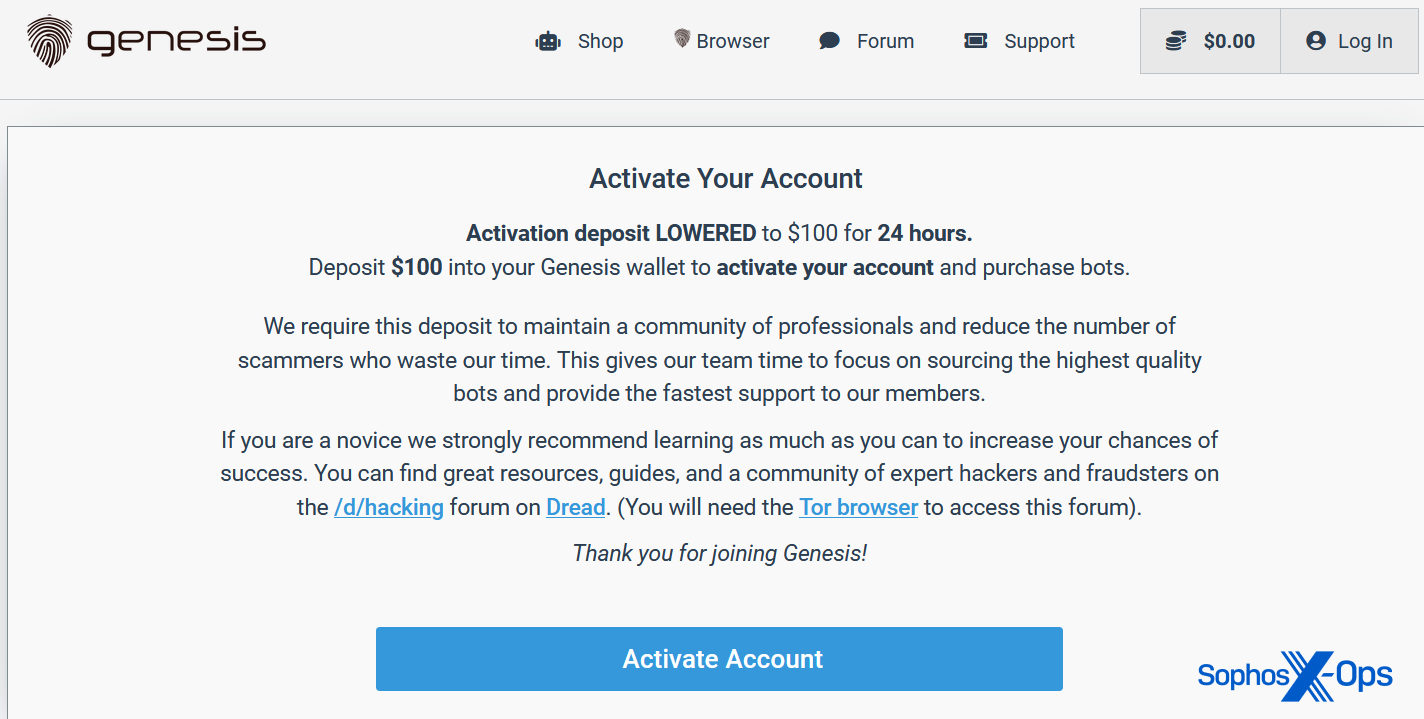
Figure 2: The deposit demand on the fake Genesis site
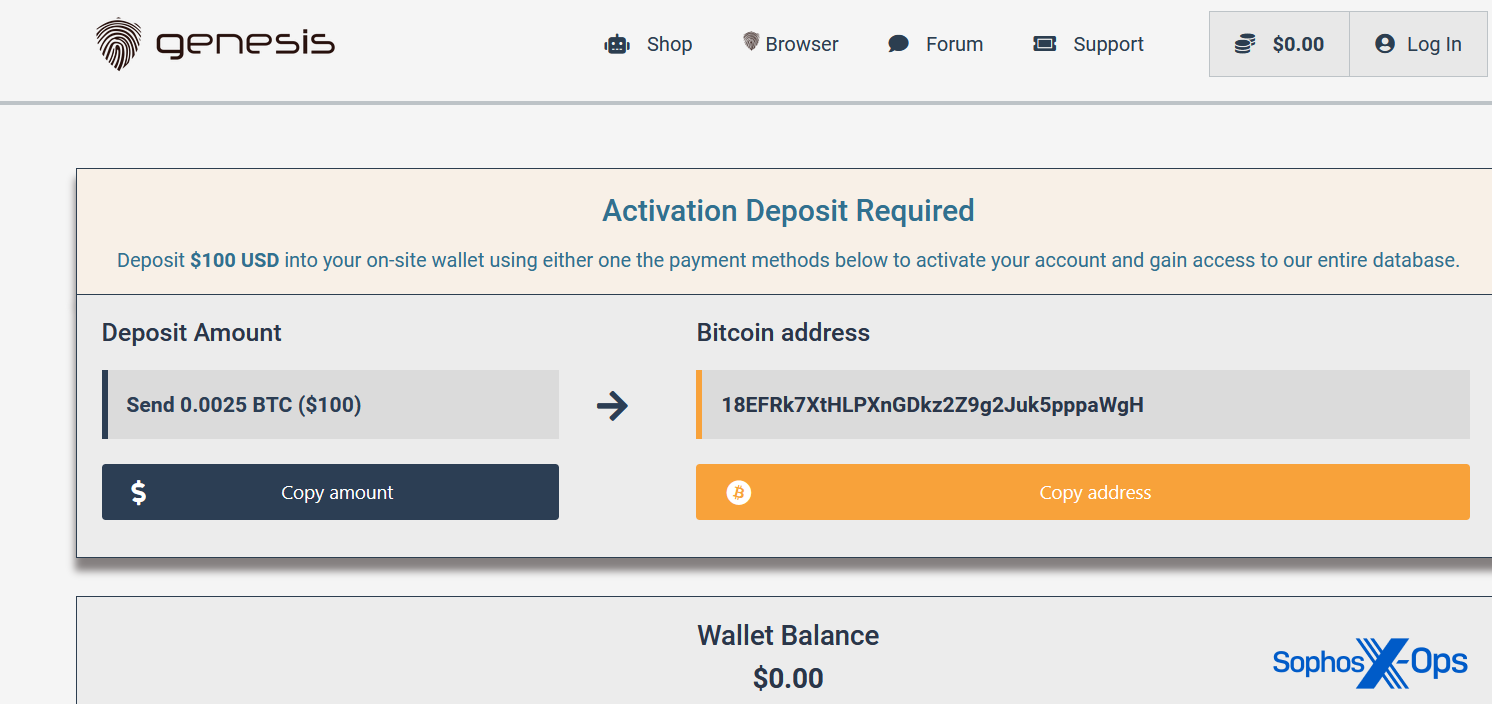
The site asks users to pay in Bitcoin or Monero:
Figure 3: The fake site’s deposit page
This, and a few other elements (such as the ‘lost password’ button not redirecting anywhere, and some falsified ‘forum posts’) led us to assume it was a crude, low-effort, one-off scam, designed to take advantage of inexperienced researchers, would-be threat actors, and the generally curious.
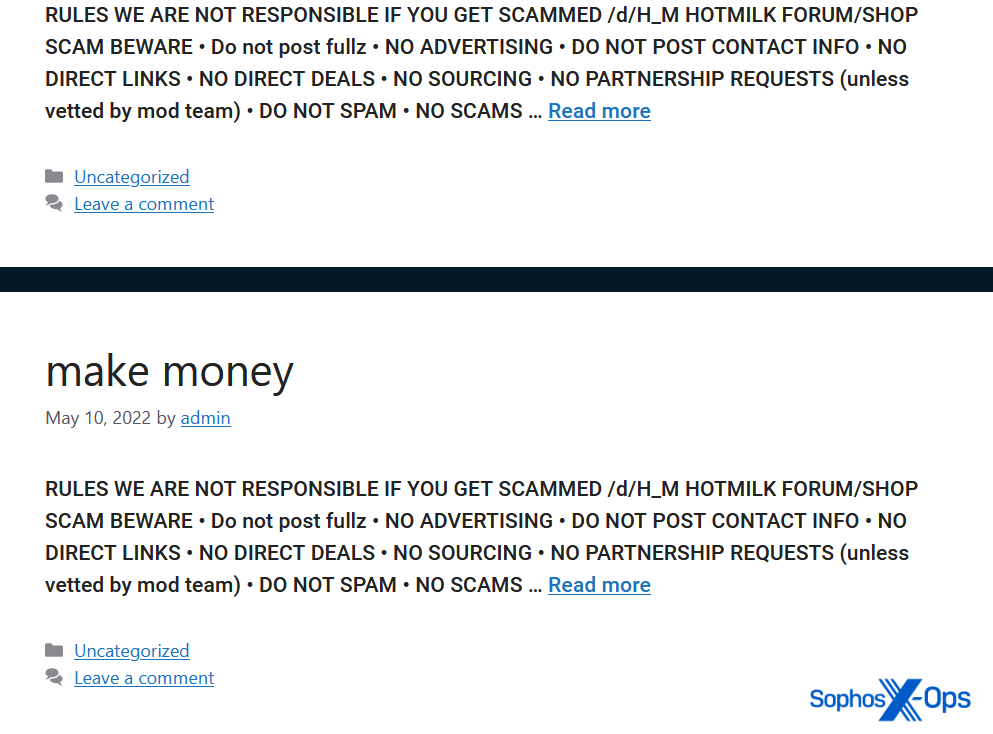
Figure 4: Some of the low-effort fake forum posts
But three things piqued our curiosity.
The first was that the onion link on the homepage doesn’t link to an onion site at all, but to genesismarket[.]org/benumbiernqlud55izbw4mdubush4zhzpg4rw3c2j6ew3ggpzbb7gdqd[.]onion. Benumb is a carding site, and we wondered if someone from that marketplace was running the scam and had made a mistake with the link.
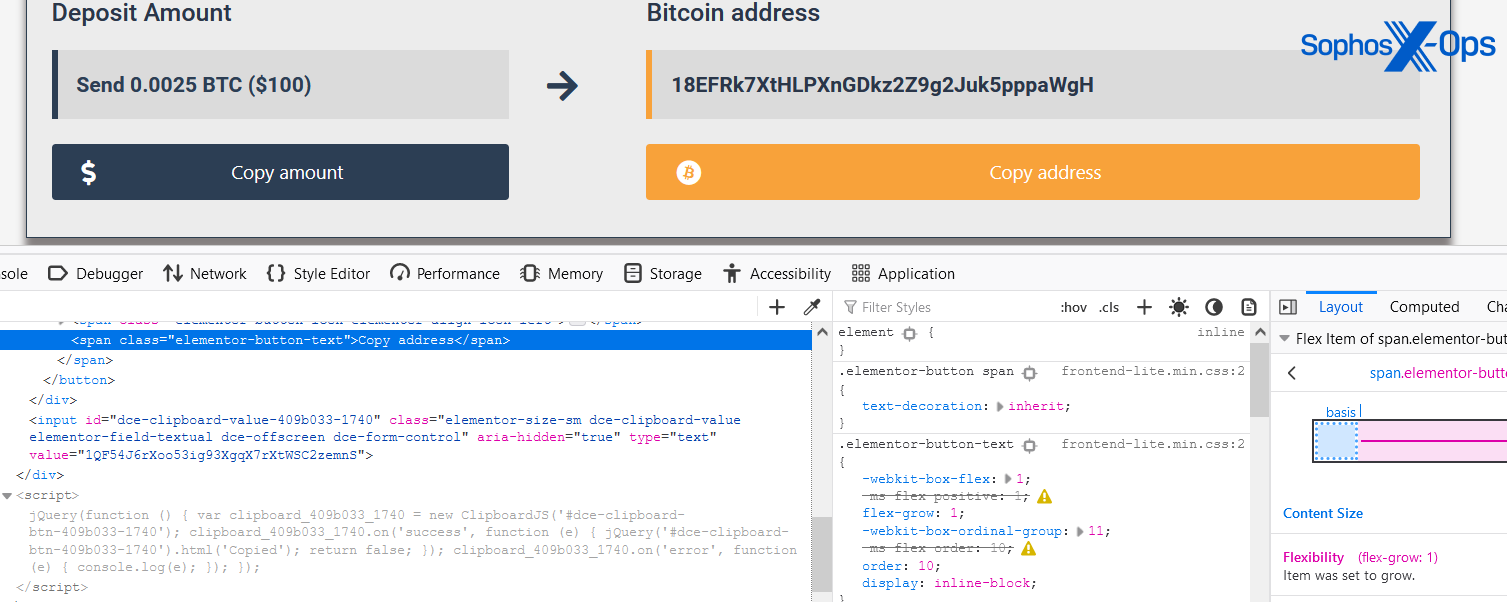
The second thing was that the Copy address button on the deposit page triggers some JavaScript, which copies a different Bitcoin address to the clipboard:
Figure 5: Clicking the ‘Copy address’ button results in a different address being copied to the clipboard
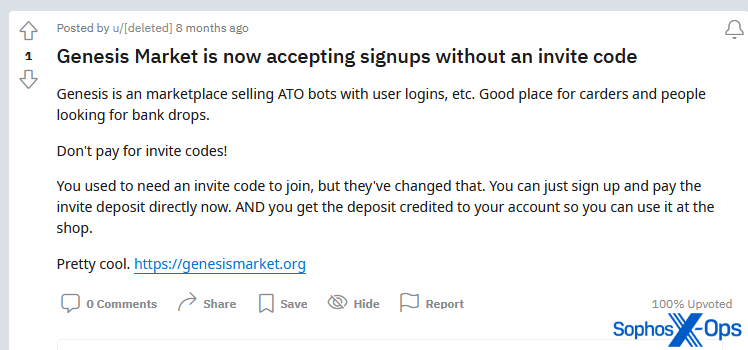
And the third was that someone had actively advertised this site on Reddit, which suggested the scam might be more coordinated than we first thought:
Figure 6: A now-deleted Reddit post advertising the fake site
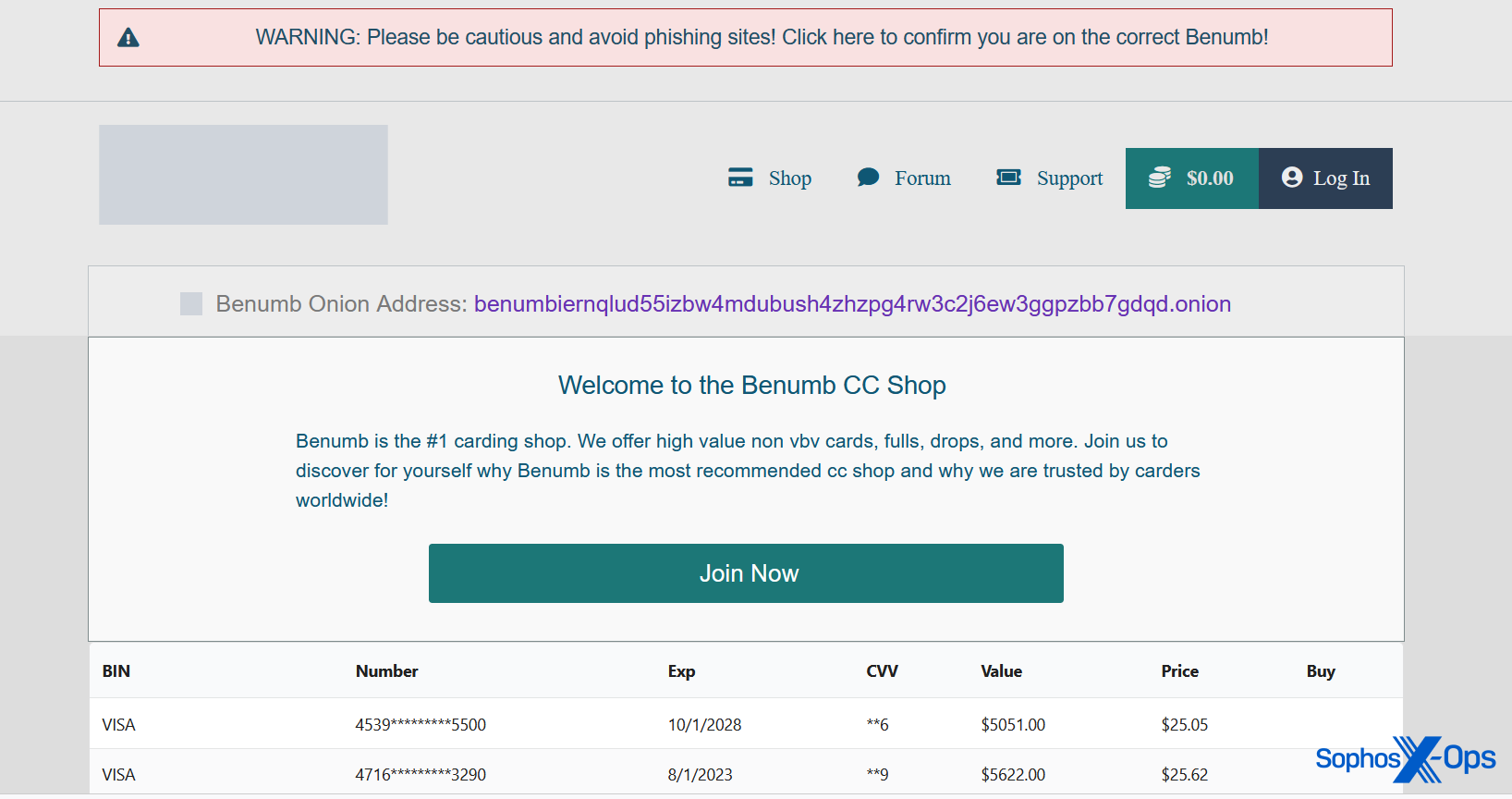
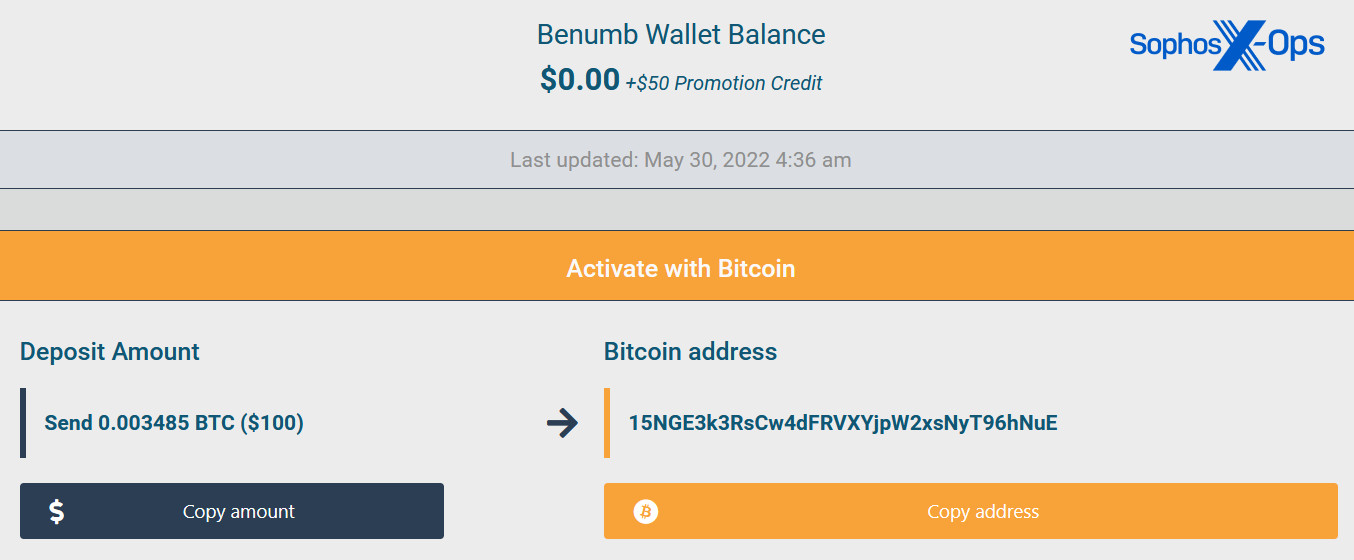
We visited the ‘Benumb’ link and found a site set up in exactly the same way, with the same demand for $100 (albeit with different Bitcoin and Monero addresses):
Figure 7: The fake Benumb page, with an ironic phishing warning
Figure 8: The fake Benumb’s wallet page
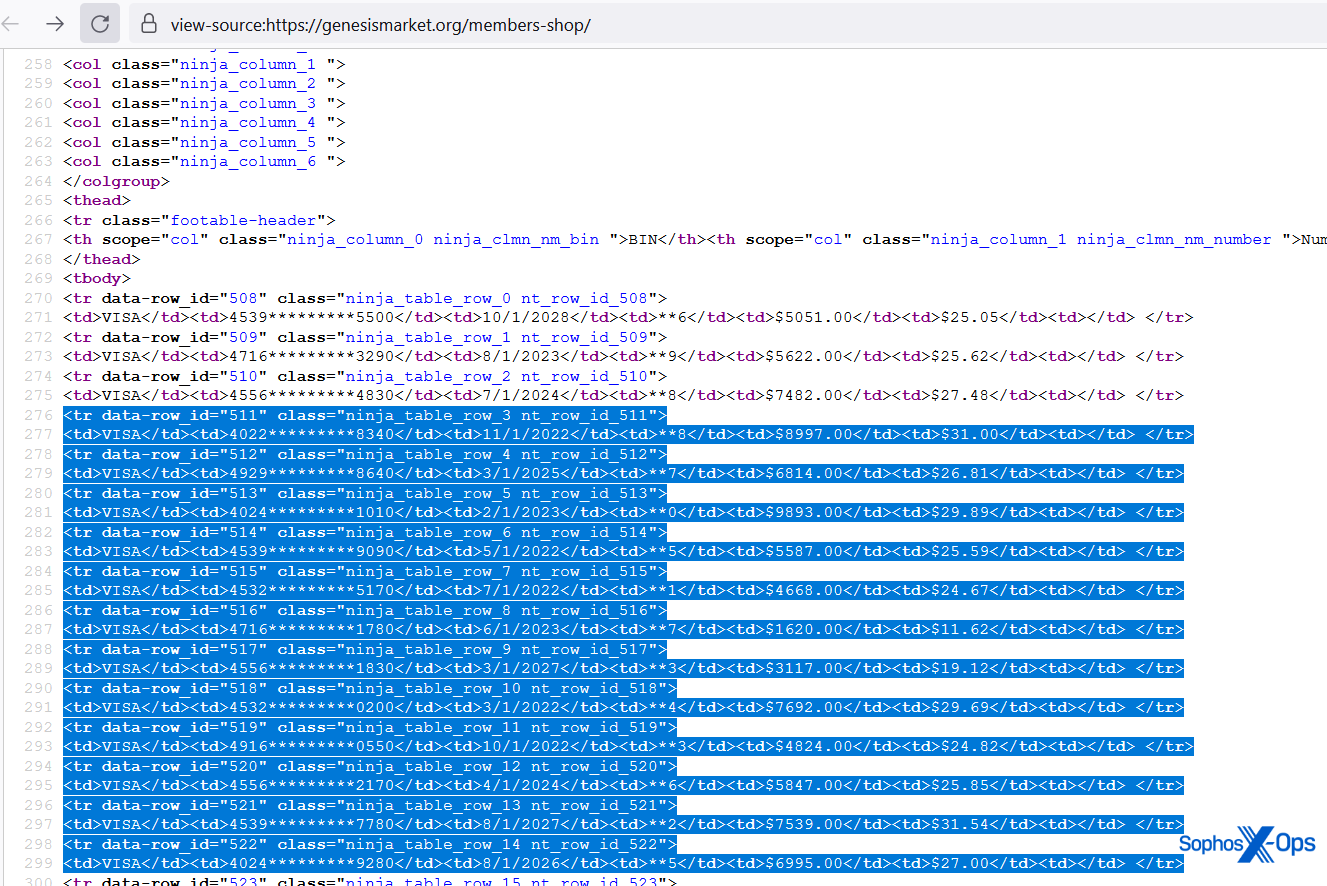
And when we looked at the credit card numbers on the homepage, we discovered that they were identical to the ones listed on the fake Genesis site.
Figure 9: The credit card numbers and details on the fake Benumb homepage…
Figure 10: …which are exactly the same as those on the fake Genesis site
We started querying search engines for portions of the text, the credit card details, and the cryptocurrency addresses, to find other sites created by the same scammer.
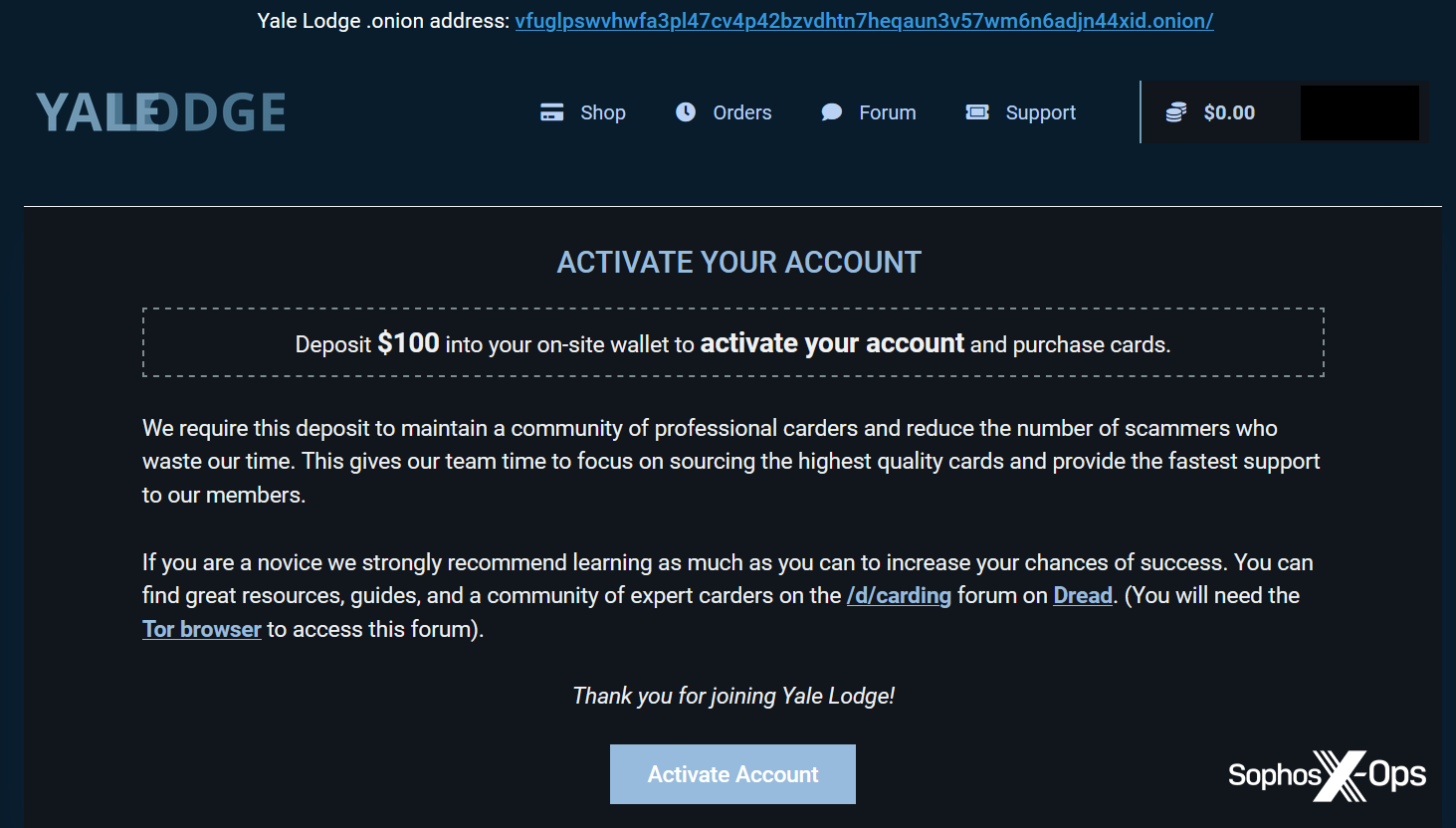
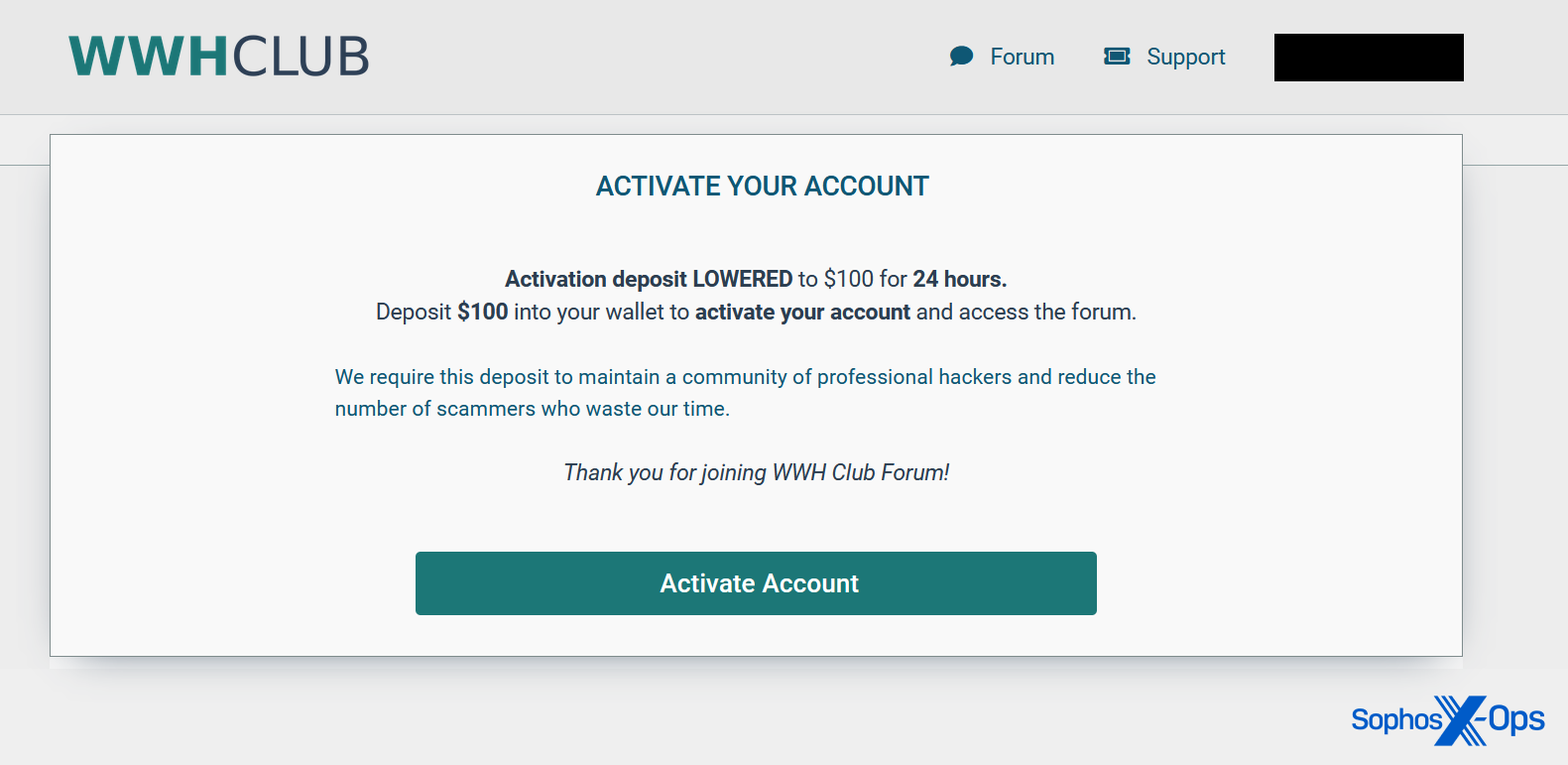
All in all we found twenty sites, registered between August 2021 and June 2022, which we assess with high confidence are operated by the same individual or group. Virtually all of them imitate existing or defunct criminal marketplaces (including multiple scam versions of Genesis, Benumb, UniCC, and Pois0n), ask for an activation deposit of $100, and have a similar look and feel. Some employ the same clipboard substitution quirk, and some don’t. We also observed a few other minor differences, like background color or slight modifications to the spiel.
Figure 11: A scam version of YaleLodge, a criminal marketplace
Figure 12: A scam version of another marketplace, WWH Club
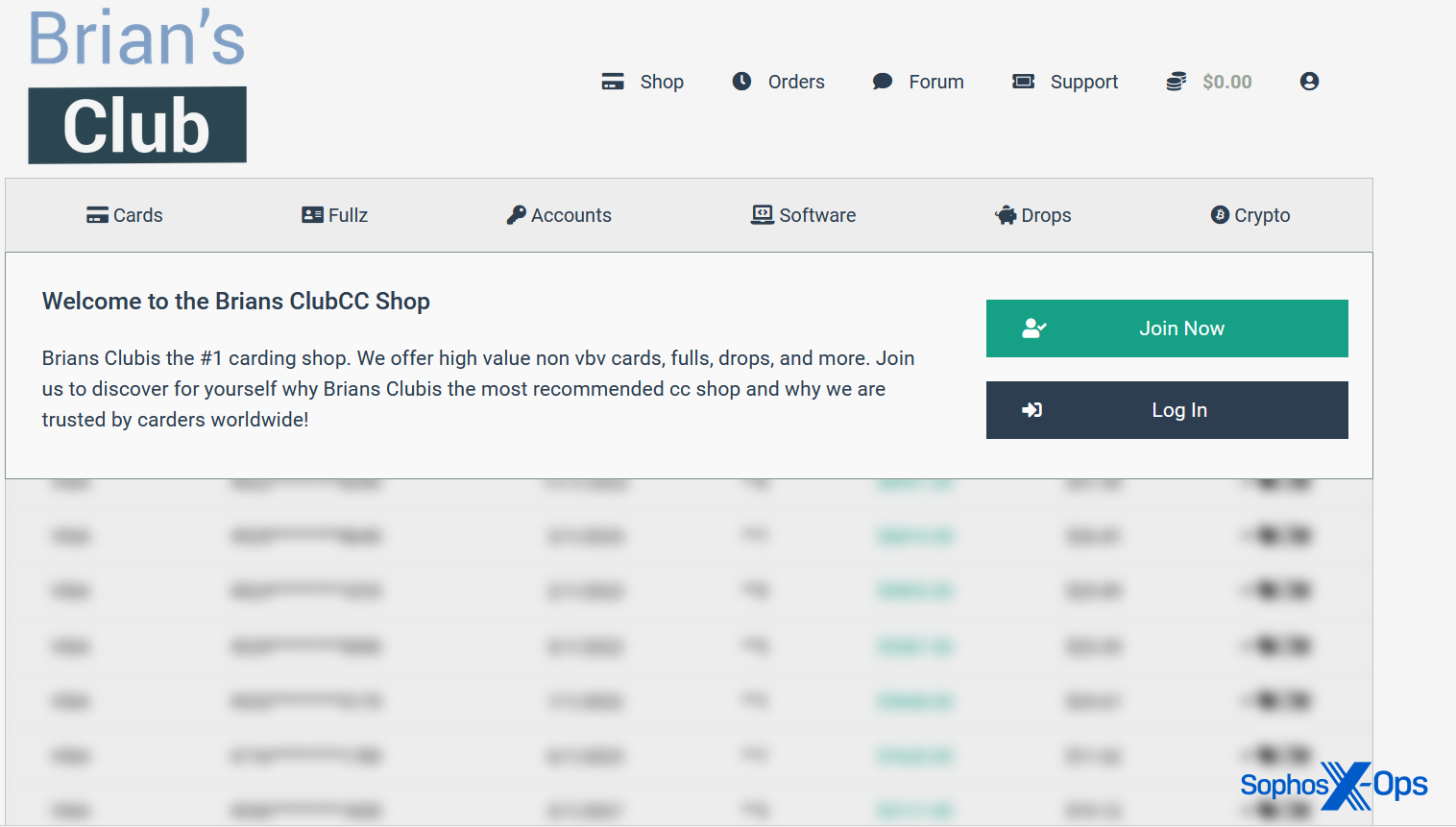
Figure 13: A scam version of Brian’s Club, yet another criminal marketplace
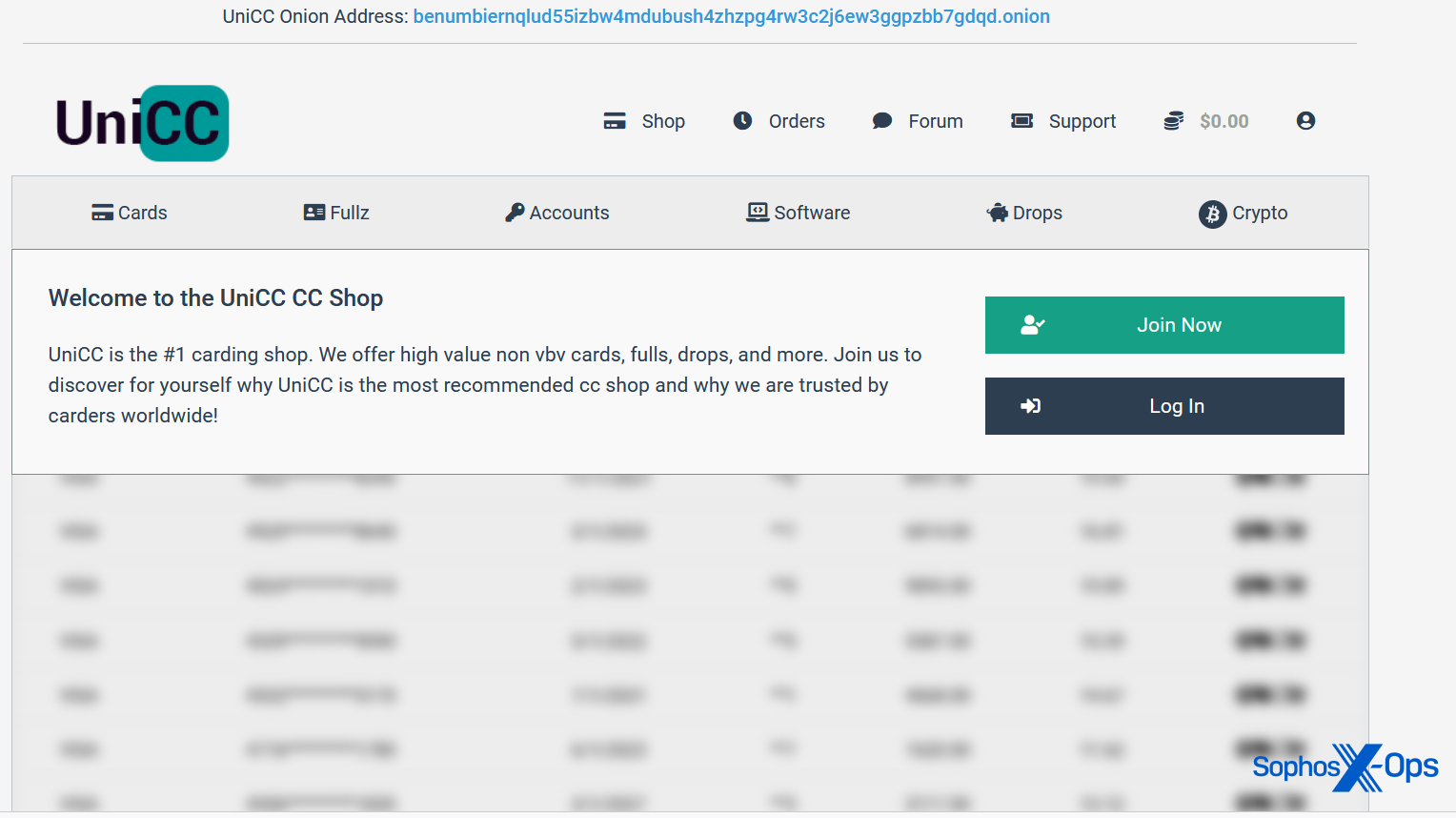
Figure 14: A scam version of the UniCC carding site (the genuine site closed in January 2022). Note that this site also contains a link to the fake Benumb site
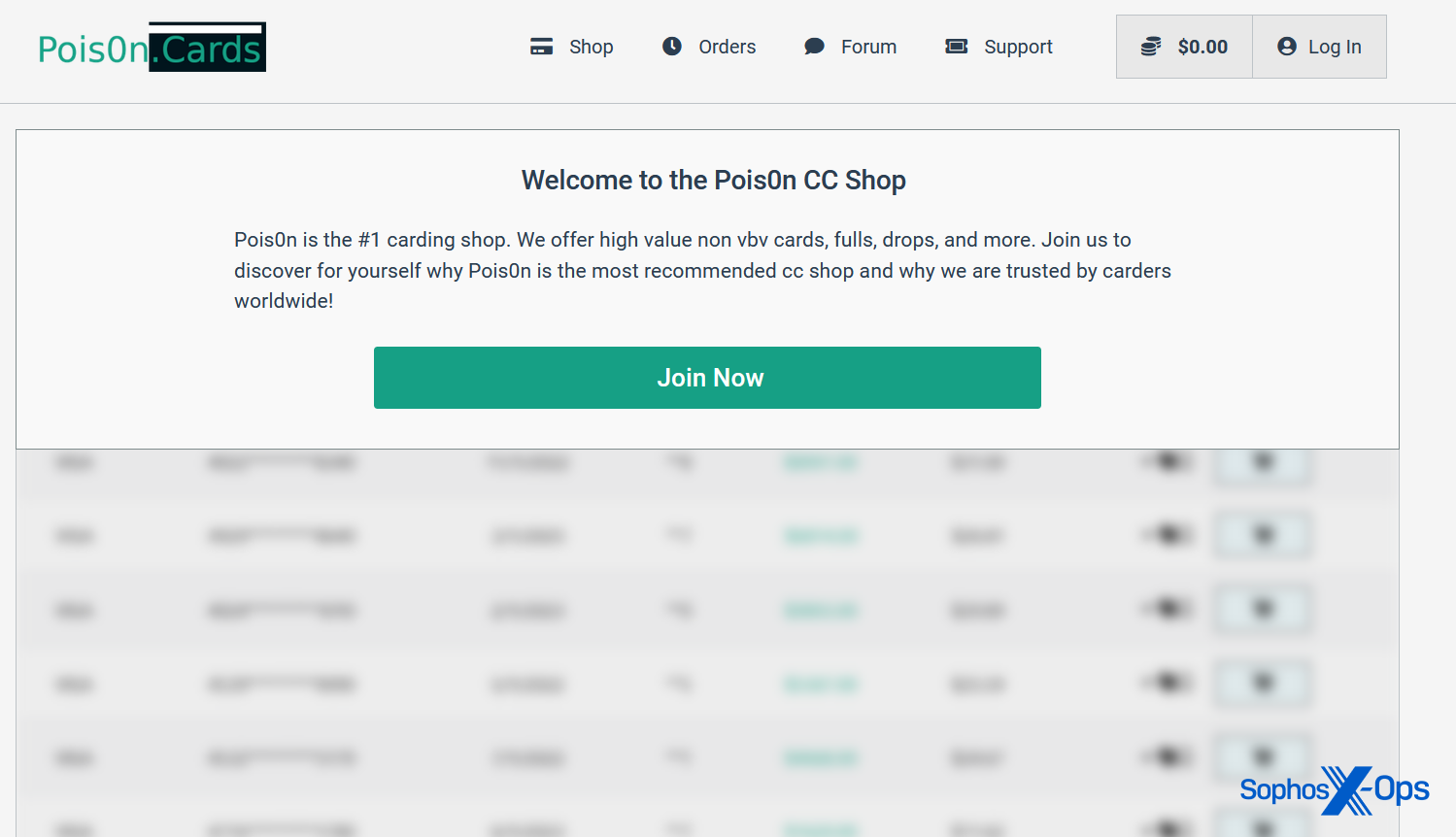
Figure 15: A scam version of Pois0n, another criminal marketplace
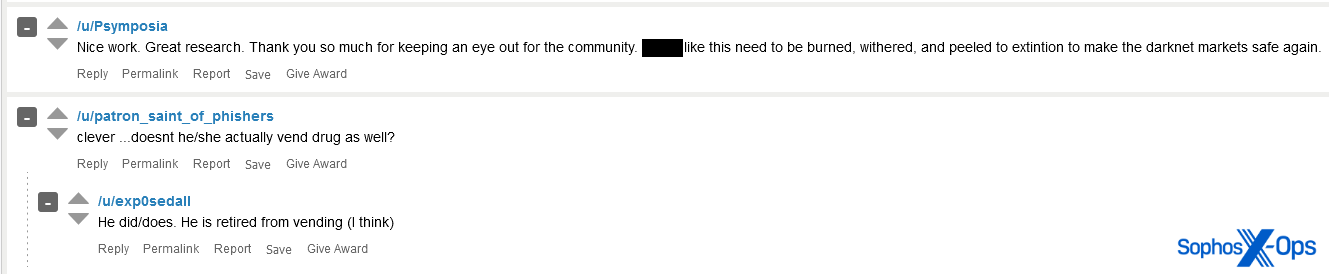
Along the way, we found evidence that the scammer was advertising other sites on Reddit:
Figure 16: A Reddit post promoting one of the fake Benumb sites
We did find one anomaly – a site called ‘Cashout Guide’, which claims to teach users carding and fraud (for a fee, naturally) – which nonetheless has a similar appearance to the scam marketplaces:
Figure 17: Available tiers on the Cashout Guide site
Of the twenty sites we found, thirteen are no longer active. Most are clearnet sites, although we discovered three onion sites (and one clearnet site masquerading as an onion site).
Here’s a full list, along with the associated Bitcoin addresses and registration information (where available):
| Site | WHOIS registration | Registrar | BTC |
| genesismarket.org | 06/09/2021 | Tucows | 1QF54J6rXoo53ig93XgqX7rXtWSC2zemnS 18EFRk7XtHLPXnGDkz2Z9g2Juk5pppaWgH |
| wwh.club | 09/05/2022 | Porkbun | 15NGE3k3RsCw4dFRVXYjpW2xsNyT96hNuE |
| brians.cards | 22/02/2022 | Tucows | 1Q5AKMFfhV2jTu1Jjpm1pMP7qabApe9Xr |
| uniccards.com | 09/02/2022 | Namecheap | 1Q5AKMFfhV2jTu1Jjpm1pMP7qabApe9Xr |
| benumb.cards | 28/08/2021 | Tucows | 1QF54J6rXoo53ig93XgqX7rXtWSC2zemnS |
| yalelodge.cards | 09/02/2022 | Tucows | 1QF54J6rXoo53ig93XgqX7rXtWSC2zemnS |
| unic.cards | 09/02/2022 | Tucows | 1KjZcgsTh9SZJiLDHBYQem96Z4CwbgQPL2 |
| pois0n.cards | 22/04/2022 | Tucows | 14KRaiCZp2zYPyRqVd3AHbyjT6qPcSnMKn |
| pois0n.shop | 22/04/2022 | Namecheap | N/K |
| genesismarket.app | 27/04/2022 | Tucows | 18EFRk7XtHLPXnGDkz2Z9g2Juk5pppaWgH |
| benumb.shop | N/K | Namecheap | N/K |
| benumb-cc.shop | 27/04/2022 | Namecheap | N/K |
| bydto.com | 08/04/2022 | Tucows | N/K |
| cashouts.guide | 10/03/2022 | Hosting Concepts B.V. | 14ZFe4BH5FdfvdyndxfK4rwJtf3oPHjTgS |
| bennumb.cards | 17/02/2022 | N/A | bc1qn2gfx8x9t234s8ncs80k3mrf5359g34xkxj0j8 |
| benumbiernqlud55izbw4mdubush4zhzpg4rw3c2j6ew3ggpzbb7gdqd.onion | N/A | N/A | 15NGE3k3RsCw4dFRVXYjpW2xsNyT96hNuE |
| shops4knpoaodqdvs3tgzctkwk2cot6nggtyfpfxjuno23brpzpaquyd.onion | N/A | N/A | 1FWrm3Z1g2W4kEQXgsUyHXEk2S9dTVK54P |
| j4j245araf5zxzd6z342a7cmakooyx3g7rt4oluffu6zimjshtbkpsid.onion | N/A | N/A | N/K |
| benumbie55bw4mdubszhzpg4rw3c2j6ew3gpzbb7gdqd.online | 23/06/2022 | Gransy s.r.o. | bc1q2jw57fy5cf5rrdcdjcdwz34nln5xmycpunzay8 |
| rainblack.com | 07/06/2022 | Porkbun | N/K |
Table 1: The sites we discovered
When we collated information from all the Bitcoin addresses (by design, the balances of Monero addresses are hidden), we found that this scam network has been lucrative. Together, those addresses have received over $132,000 – and most of it has been withdrawn, leaving a total balance of only $1,633.34.
We can’t say for certain whether all the inputs to those addresses are related to the scam (i.e., we don’t know if the scammer has used them for other business), and in a few cases, the timelines didn’t add up (a few addresses made their first transaction before the associated site(s) were registered, so some inputs may have been unrelated to the scam). But even taking those examples out, there was still $87,676 going into those wallets.
One big question remained: who was behind the scam?
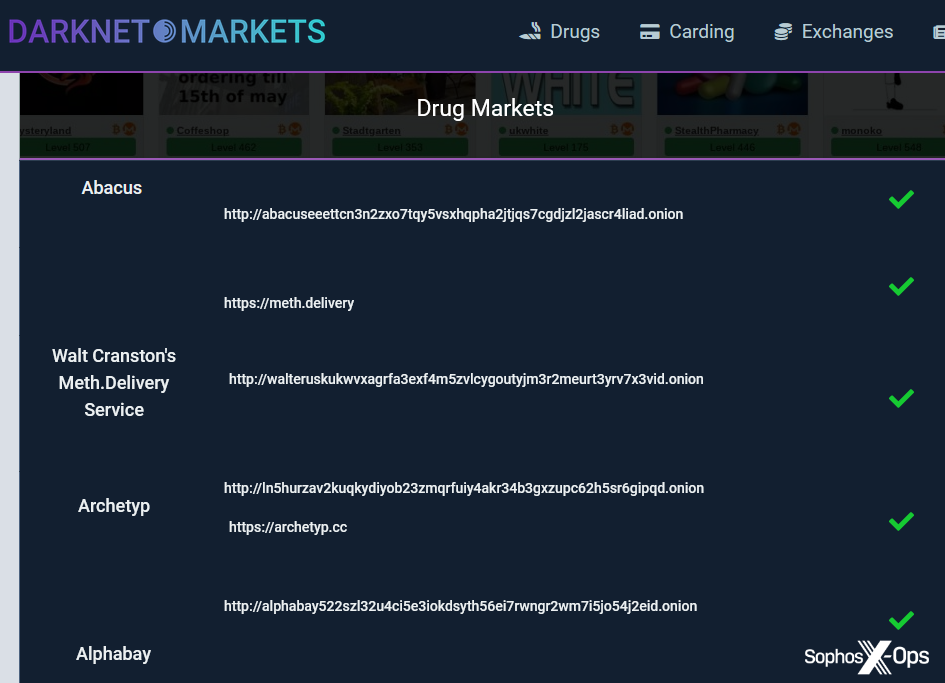
We found something we thought might be a clue: on some sites, the footer contains a link to a website called darknet[.]markets (there appear to be a few versions of this site with very similar content, including darknetmarket[.]org and dark[.]markets).
Figure 18: A link to darknet[.]markets on the scam site unic[.]cards
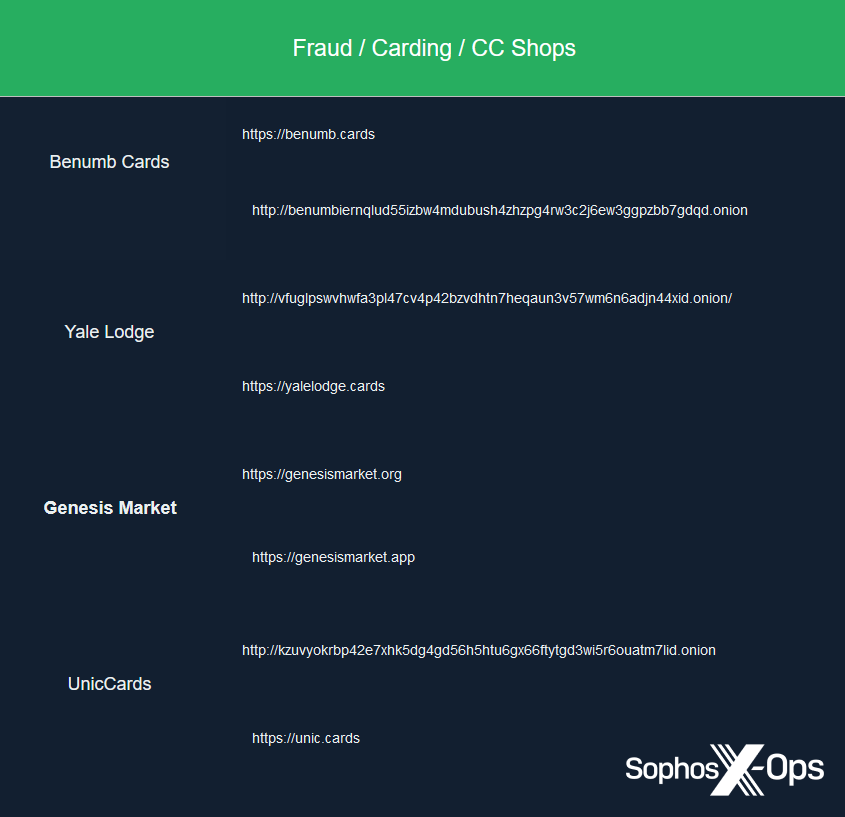
These sites are indexes of dark web criminal marketplaces, for visitors interested in drugs sales, carding, and cryptocurrency exchanges. Not only do they look similar to the scam marketplaces (and with similar hosting/registration details), they also list several of the fake marketplaces we discovered.
Figure 19: The ‘carding’ section on dark[.]markets
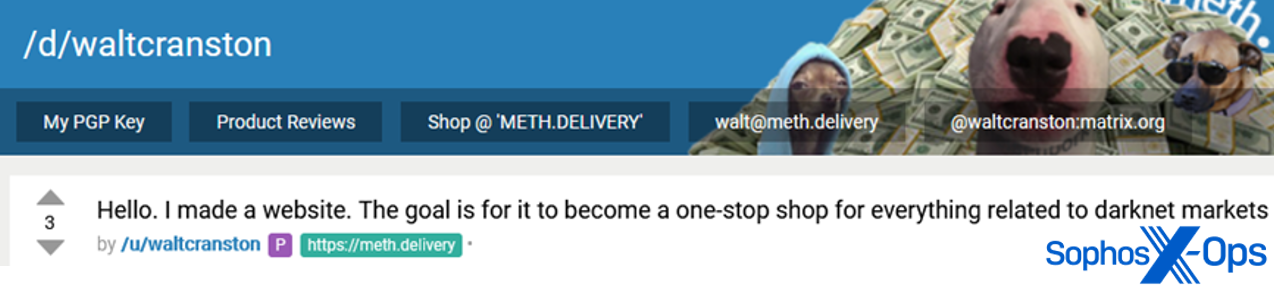
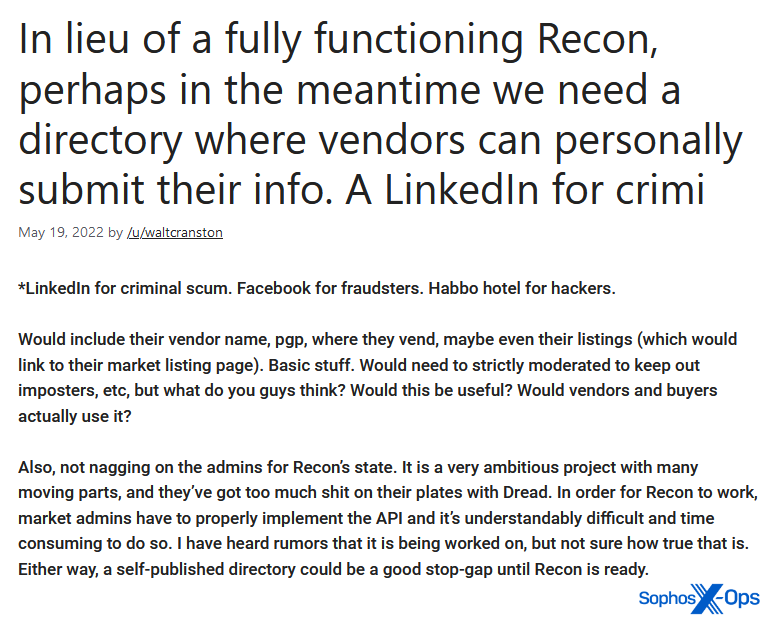
Most of the activation notices on the scam marketplaces mention a carding forum on the criminal marketplace Dread (also known as Café Dread). We searched the names of the index sites on Dread, and found a post by a user called waltcranston (the username is likely inspired by the television series Breaking Bad), who claimed to have created them:
Figure 20: waltcranston’s post (now deleted)
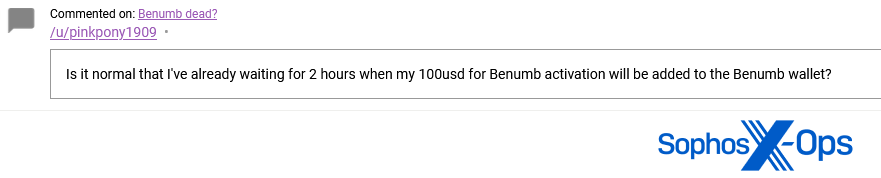
We also found at least one Dread user who seemed to fall for one of the scams:
Figure 21: A Dread user’s post
We dug further into the index sites, and found waltcranston listed prominently in the ‘Drug Markets’ section:
Figure 22: waltcranston’s onion link on one of the index sites
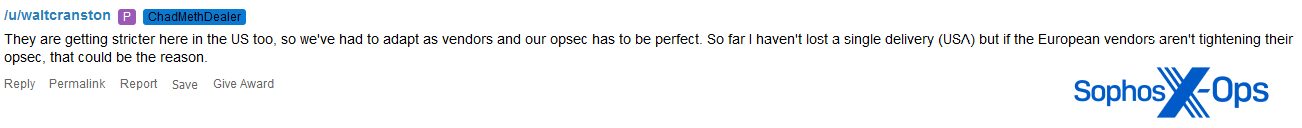
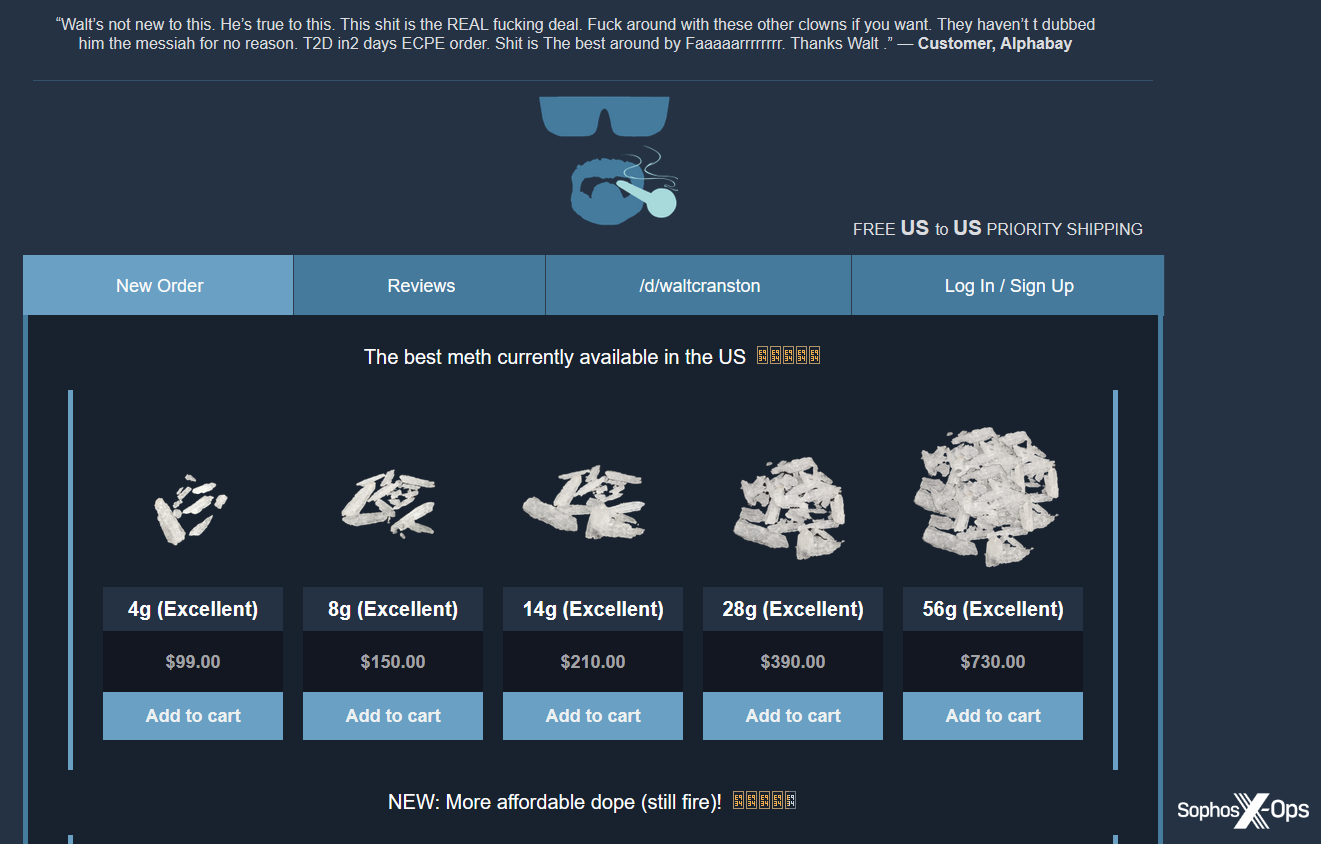
waltcranston is a self-proclaimed methamphetamine dealer on both Dread and other marketplaces such as Alphabay. By their own admission they’re based in the US:
Figure 23: waltcranston claims to be based in the US
Their website appears to use a similar template to the scam marketplaces, and the clearnet version has similar hosting and registration details:
Figure 24: waltcranston’s vendor site
We also found that one of the fake forum posts on at least one of the scam marketplaces was written by a waltcranston:
Figure 25: A forum post on one of the fake Benumb marketplaces
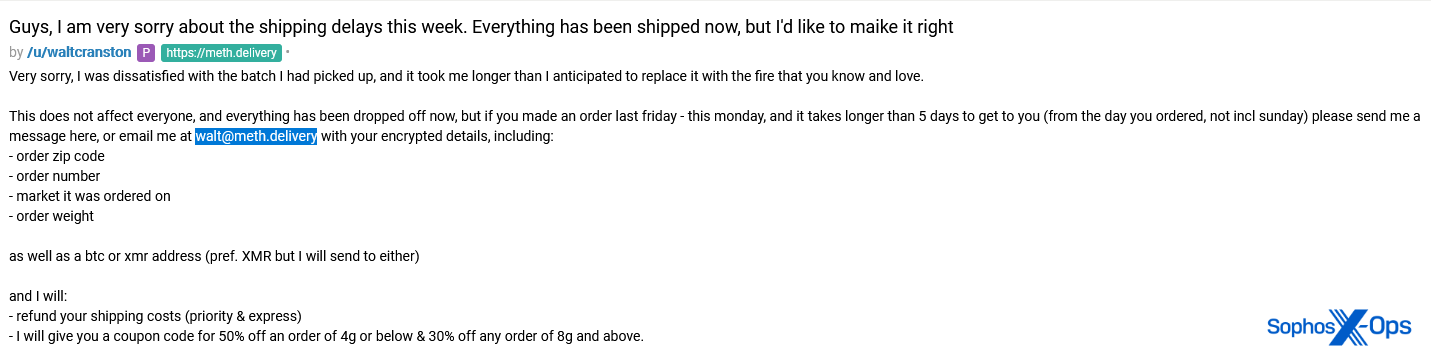
waltcranston uses both Bitcoin and Monero, as shown in this post:
Figure 26: In a post relating to their methamphetamine business, waltcranston confirms they use both Bitcoin and Monero
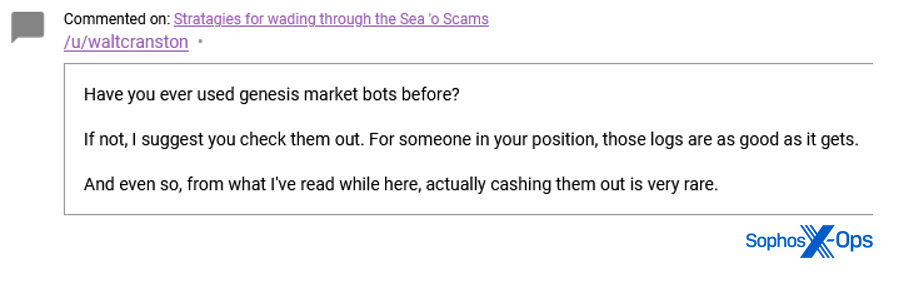
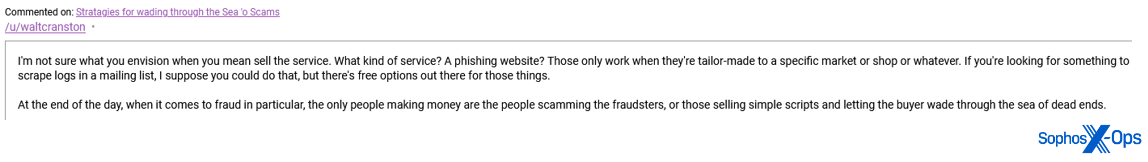
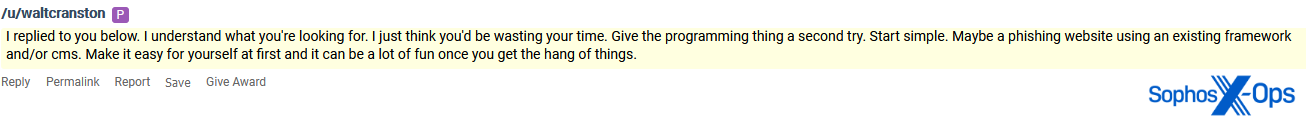
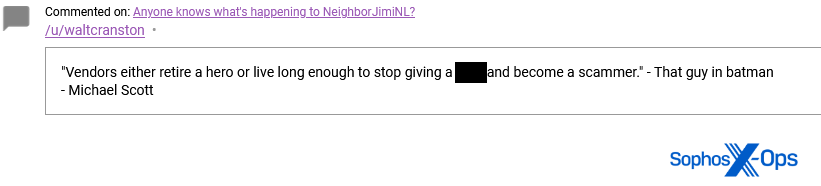
And several of waltcranston’s posts indicate a familiarity with criminal marketplaces and an open-minded attitude towards phishing and scamming, particularly when it comes to imitating specific marketplaces:
Figure 27: waltcranston recommends Genesis Market to another user
Figure 28: waltcranston passes on some advice regarding phishing sites “tailor-made to a specific market or shop”
Figure 29: waltcranston suggests running a phishing site to another user
Figure 30: waltcranston with a tongue-in-cheek quote about vendors turning to scamming
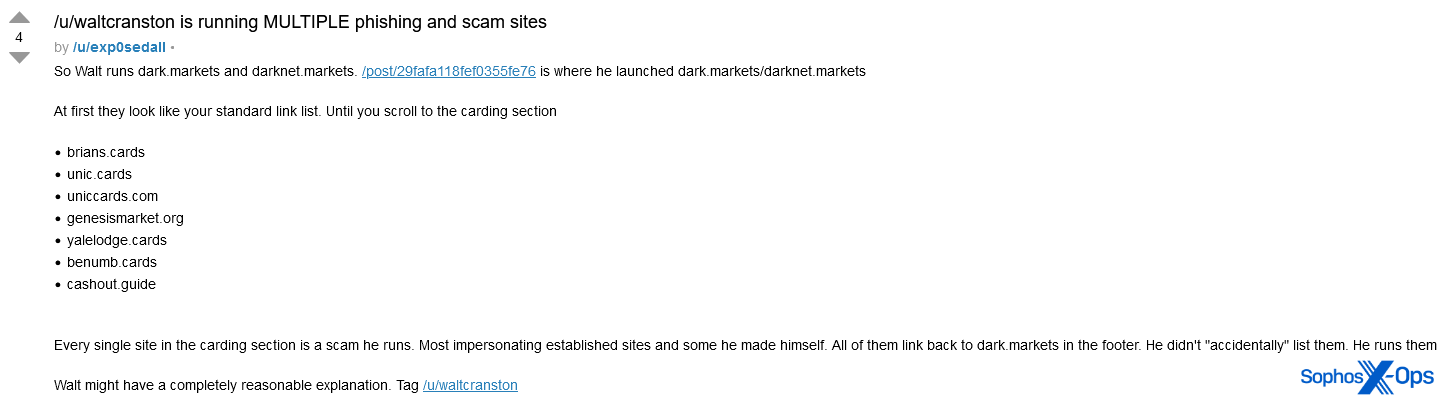
A Dread user had come to the same conclusion as us, publicly posting this accusation:
Figure 31: A Dread user calls out waltcranston for running some of the scam marketplaces we discovered
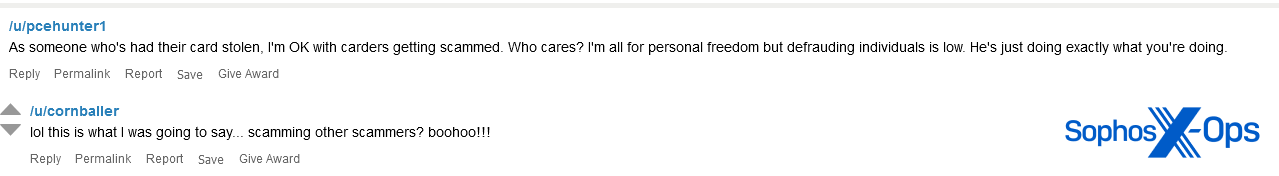
waltcranston did not confirm or deny the allegation in his responses, although other Dread users chipped in:
Figure 32: Some Dread users condemned scammers
In the above conversation, the accuser suggests a possible motivation for waltcranston running these scamming sites – retirement from dealing methamphetamine.
Other Dread users were more apathetic about the situation:
Figure 33: Two Dread users less concerned about scammers
We should point out here that most of this evidence is circumstantial, and we didn’t find any discrete identifiers which link waltcranston to the fake marketplaces.
In the final part of our series, due out Wednesday 28 December, we’ll show why this subject matters. Scam reports are a rich, and underexplored, source of intelligence; threat actors are aware that criminal forums are monitored, and so often employ good operational security – but when they’re victims of crime themselves, not so much. Because forum rules demand proof to support scam allegations, wronged threat actors will often post screenshots of private conversations and source code, identifiers, transactions, chat logs, and blow-by-blow accounts of negotiations, sales, and troubleshooting. We’ll share some case studies and wrap up our series with some recommendations and ideas for future research.

![A Reddit post advertising the fake Benumb[.]cards site](https://news.sophos.com/wp-content/uploads/2022/12/image16-1.png)
![The cashout[.]guide site](https://news.sophos.com/wp-content/uploads/2022/12/image17-2.png)
![A screenshot of one of the scam marketplaces, with a prominent footer linking to darknet[.]markets](https://news.sophos.com/wp-content/uploads/2022/12/image19-2.png)
Leave a Reply