Organizations continue cleaning up from last week’s WannaCry ransomware worm outbreak, and are still trying to make sense of how this thing became such a monster. In the following video, we break down the process, including how it spread and how Sophos Intercept X protects against it.
Outbreak updates
Four days since WannaCry hijacked 200,000 computers in 150 countries, SophosLabs have determined that this probably didn’t start the way a typical ransomware attack does – as a phishing email carrying a malicious attachment or link that the user is tricked into opening. It also appears the first infections were in south-east Asia.
Researchers assumed early on that the outbreak began with an email link or attachment, but SophosLabs VP Simon Reed identified it as a worm from start to finish.
In other words, this outbreak was a throwback to the early 2000s. Only this time, instead of mere noise and network downtime, a much more damaging payload of ransomware ground many organizations to a halt.
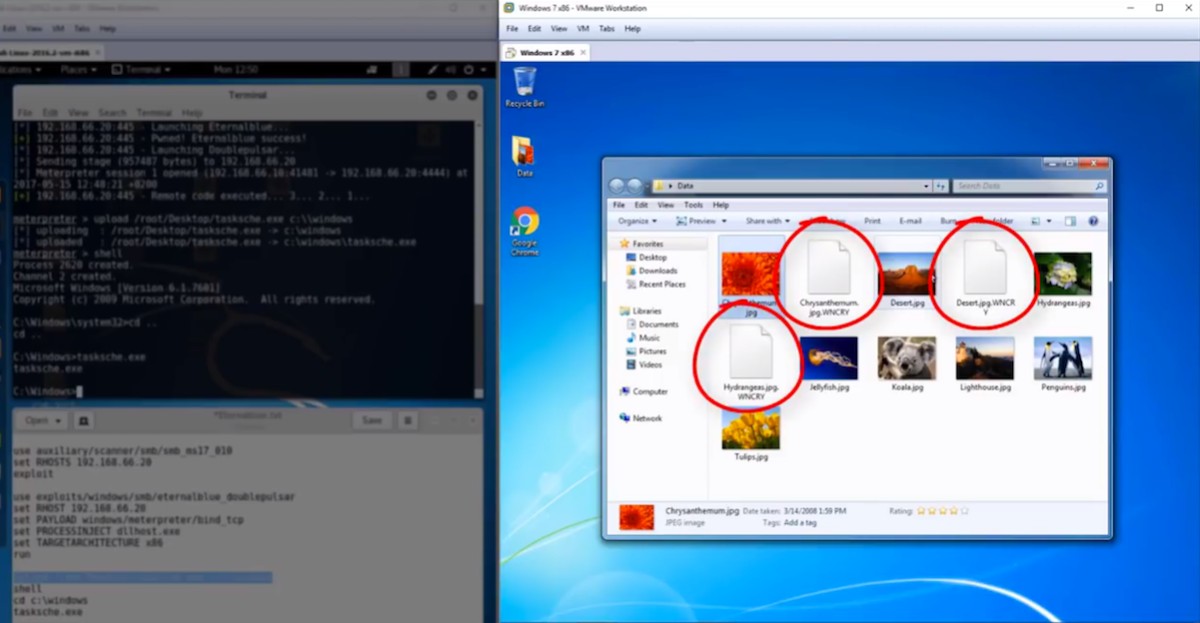
Analysis seems to confirm that Friday’s attack was launched using suspected NSA code leaked by a group of hackers known as the Shadow Brokers. It used a variant of the Shadow Brokers’ APT EternalBlue Exploit (CC-1353), and used strong encryption on files such as documents, images, and videos.
More malware using leaked NSA tools
Weeks before the WannaCry ransomware worm tore up the internet, another strain of malware was doing it. That malware, Adylkuzz, is a cryptocurrency miner that, like WannaCry, has likely infected hundreds of thousands of computers across the globe. It wasn’t previously discovered because, unlike WannaCry, it allows computers to operate while creating the digital cash in the background. SophosLabs has been detecting and protecting customers from the malware.
Defensive measures
Whether it’s WannaCry or Adylkuzz, the best advice, especially given the wormy nature of these malware families, is to:
- Stay on top of all patch releases and apply them quickly, especially those released by Microsoft.
- If at all possible, replace older Windows systems with the latest versions.
And since these malware families are all about collecting cryptocurrency, it’s worth repeating our ransomware advice:
- Back up regularly and keep a recent backup copy off-site. There are dozens of ways other than ransomware that files can suddenly vanish, such as fire, flood, theft, a dropped laptop or even an accidental delete. Encrypt your backup and you won’t have to worry about the backup device falling into the wrong hands.
- Be cautious about unsolicited attachments. The crooks are relying on the dilemma that you shouldn’t open a document until you are sure it’s one you want, but you can’t tell if it’s one you want until you open it. If in doubt, leave it out.
- Use Sophos Intercept X and, for home (non-business) users, register for Sophos Home Premium Beta, which stops ransomware in its tracks by blocking the unauthorized encryption of files.
Michael Probst
Thank you for this Informations. I’ve read Online, that WannaCry and (NEW!) the Adylkuzz used Port 445 to get inside. Sophos also uses this port. Is there anything to do on the Sophos Firewall to block this port?
I don’t have Intercept X yet.
Thank you
Mark Stockley
Hi Michael, please take a look at our WannaCry knowledgebase article for information about how to protect yourself using Sophos products https://community.sophos.com/kb/en-us/126733. That article is updated as new information comes to light and new protection is released. If that doesn’t answer your question then please contact Support https://www.sophos.com/en-us/support.aspx