Microsoft on Tuesday released 79 patches touching eleven product families. Seven of those issues, affecting Azure, SharePoint, and Windows, are considered by Microsoft to be of critical severity. At press time, three of the issues addressed are known to be under exploit in the wild, with a fourth issue not itself under exploit, but intertwined with issues that are. (For details on this unusual situation, please see the “Notable September updates” section below.) Microsoft assesses that 11 CVEs, all in Windows, are by the company’s estimation more likely to be exploited in the next 30 days. Eight of this month’s issues are amenable to detection by Sophos protections, and we include information on those in a table below.
In addition to these patches, the release includes advisory information on three CVEs addressed by patches from Adobe, affecting Reader and ColdFusion; one of the Reader vulnerabilities CVE-2024-41869) is a critical-severity use-after-free with a workable exploit already available in the wild. We are as always including at the end of this post additional appendices listing all Microsoft’s patches, sorted by severity, by predicted exploitability, and by product family.
By the numbers
- Total CVEs: 79
- Total Adobe advisories covered in update: 3
- Publicly disclosed: 1
- Exploited detected: 4*
- Severity
- Critical: 7
- Important: 71
- Moderate: 1
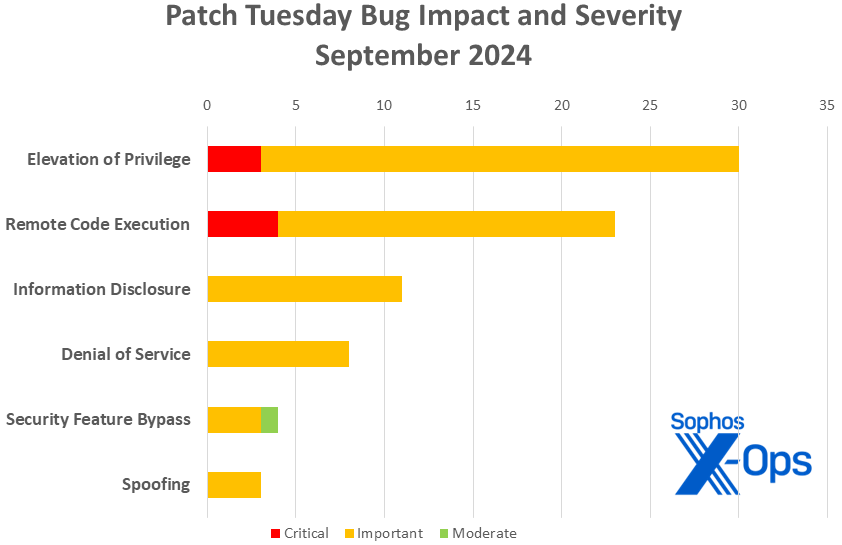
- Impact
- Elevation of privilege: 30
- Remote code execution: 23
- Information disclosure: 11
- Denial of service: 8
- Security feature bypass: 4
- Spoofing: 3
- CVSS base score 9.0 or greater: 2
- CVSS base score 8.0 or greater: 24
* For information on why we count CVE-2024-43491 as this month’s fourth exploited-detected CVE despite the CVE itself not being detected as under exploit, please see the “Notable September updates” section below.
Figure 1: This month’s critical-severity patches include one for which exploitation has already been detected, and two more for which exploitation is more likely within the next 30 days
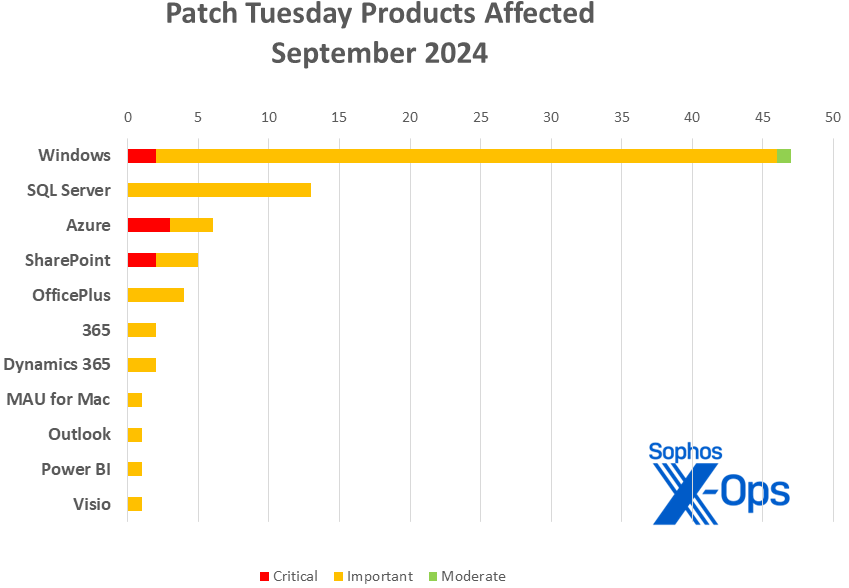
Product families
- Windows: 47
- SQL Server: 13
- Azure: 6
- SharePoint: 5
- Office: 4
- 365: 2
- Dynamics 365: 2
- Microsoft AutoUpdate (MAU) for Mac: 1
- Outlook for iOS: 1
- Power BI: 1
- Visio: 1
As is our custom for this list, CVEs that apply to more than one product family are counted once for each family they affect.
Figure 2: Though Windows as usual leads the list of affected product families, a collection of Native Scoring issues in SQL Server contributed to that product taking 13 patches of its own
Notable September updates
In addition to the issues discussed above, a number of specific items merit attention.
CVE-2024-38217 — Windows Mark of the Web Security Feature Bypass Vulnerability
CVE-2024-43492 — Windows Mark of the Web Security Feature Bypass Vulnerability
There are patches for two Mark of the Web vulnerabilities this month, and both are either currently under active exploit in the wild (CVE-2024-38217) or judged by Microsoft as more likely to be exploited within the next 30 days (CVE-2024-43492). The latter bug was found in-house at Microsoft and is considered to be of moderate severity. The former, however, was disclosed responsibly by Elastic Security’s Joe Desimone, who has posted about the discovery and the reporting process, and which may be of interest to those who follow issues around code-signing certificates. The bug affects all versions of Windows including Win 11H24 and is of important severity.
CVE-2024-38014 — Windows Installer Elevation of Privilege Vulnerability
This issue is under active exploit in the wild. It affects all versions of Windows including Win 11H24.
CVE-2024-43491 – Microsoft Windows Update Remote Code Execution Vulnerability
The good news is that this issue affects only certain operational components of Windows 10, version 1507 (first released in July 2015); only two versions of that build, Windows 10 Enterprise 2015 LTSB and Windows 10 IoT Enterprise 2015 LTSB, are still under support. The bad news, for those still running either of those versions, is that critical-severity remote code execution issue, which carries a 9.8 CVE base score, occurs in… the Windows Servicing Stack. It’s a fascinating issue for those who care about such things — rather than a coding error per se, Microsoft explains that the build version numbers themselves “crossed into a range that triggered a code defect in the Windows 10 (version 1507) servicing stack that handles the applicability of Optional Components. As a result, any Optional Component that was serviced with updates released since March 12, 2024 (KB5035858) was detected as “not applicable” by the servicing stack and was reverted to its RTM version.” If this issue is applicable to your estate, it is recommended that you closely read and follow the information Microsoft provides in KB5043083, as the patch sequence one must follow is precise. That page also includes a list of the specific optional components affected, which may help clarify your exposure.
[29 CVEs] — Windows 11 24H2 patches
Even though Windows 11 24H2 is not yet in general release, just over a third of this month’s patches affect that platform, including two (CVE-2024-38014, CVE-2024-38217) for which exploitation has already been detected in the wild. Users of the new Copilot+ PCs who do not ingest their patches automatically should be sure to update their devices.
[0 CVEs] — .NET, Visual Studio, Edge / Chromium, non-iOS Outlook
A rare month of respite for .NET and Visual Studio, with no patches released for those families. Nor are there any this time around related to Edge, or to Outlook for platforms other than Apple’s.
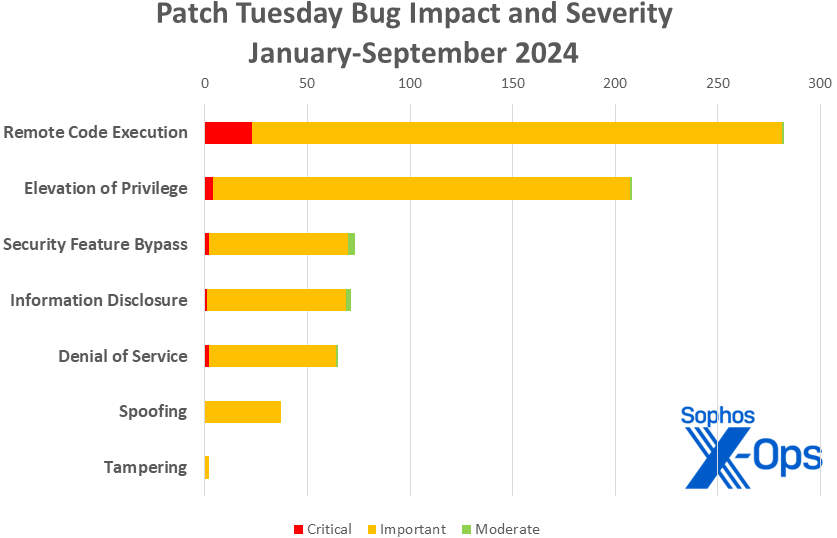
Figure 3: Despite the predominance of EoP issues in recent months, RCE continues to lead the pack as we reach the three-quarter mark for 2024.
Sophos protections
| CVE | Sophos Intercept X/Endpoint IPS | Sophos XGS Firewall |
| CVE-2024-38237 | Exp/2438237-A | Exp/2438237-A |
| CVE-2024-38238 | Exp/2438238-A | Exp/2438238-A |
| CVE-2024-38241 | Exp/2438241-A | Exp/2438241-A |
| CVE-2024-38242 | Exp/2438242-A | Exp/2438242-A |
| CVE-2024-38243 | Exp/2438243-A | Exp/2438243-A |
| CVE-2024-38244 | Exp/2438244-A | Exp/2438244-A |
| CVE-2024-38245 | Exp/2438245-A | Exp/2438245-A |
| CVE-2024-43461 | SID:2310127 | SID:2310126 |
As you can every month, if you don’t want to wait for your system to pull down Microsoft’s updates itself, you can download them manually from the Windows Update Catalog website. Run the winver.exe tool to determine which build of Windows 10 or 11 you’re running, then download the Cumulative Update package for your specific system’s architecture and build number.
Appendix A: Vulnerability Impact and Severity
This is a list of September patches sorted by impact, then sub-sorted by severity. Each list is further arranged by CVE.
Elevation of Privilege (30 CVEs)
| Critical severity | |
| CVE-2024-38194 | Azure Web Apps Elevation of Privilege Vulnerability |
| CVE-2024-38216 | Azure Stack Hub Elevation of Privilege Vulnerability |
| CVE-2024-38220 | Azure Stack Hub Elevation of Privilege Vulnerability |
| Important severity | |
| CVE-2024-37341 | Microsoft SQL Server Elevation of Privilege Vulnerability |
| CVE-2024-37965 | Microsoft SQL Server Elevation of Privilege Vulnerability |
| CVE-2024-37980 | Microsoft SQL Server Elevation of Privilege Vulnerability |
| CVE-2024-38014 | Windows Installer Elevation of Privilege Vulnerability |
| CVE-2024-38046 | PowerShell Elevation of Privilege Vulnerability |
| CVE-2024-38188 | Azure Network Watcher VM Agent Elevation of Privilege Vulnerability |
| CVE-2024-38225 | Microsoft Dynamics 365 Business Central Elevation of Privilege Vulnerability |
| CVE-2024-38237 | Kernel Streaming WOW Thunk Service Driver Elevation of Privilege Vulnerability |
| CVE-2024-38238 | Kernel Streaming Service Driver Elevation of Privilege Vulnerability |
| CVE-2024-38239 | Windows Kerberos Elevation of Privilege Vulnerability |
| CVE-2024-38240 | Windows Remote Access Connection Manager Elevation of Privilege Vulnerability |
| CVE-2024-38241 | Kernel Streaming Service Driver Elevation of Privilege Vulnerability |
| CVE-2024-38242 | Kernel Streaming Service Driver Elevation of Privilege Vulnerability |
| CVE-2024-38243 | Kernel Streaming Service Driver Elevation of Privilege Vulnerability |
| CVE-2024-38244 | Kernel Streaming Service Driver Elevation of Privilege Vulnerability |
| CVE-2024-38245 | Kernel Streaming Service Driver Elevation of Privilege Vulnerability |
| CVE-2024-38246 | Win32k Elevation of Privilege Vulnerability |
| CVE-2024-38247 | Windows Graphics Component Elevation of Privilege Vulnerability |
| CVE-2024-38248 | Windows Storage Elevation of Privilege Vulnerability |
| CVE-2024-38249 | Windows Graphics Component Elevation of Privilege Vulnerability |
| CVE-2024-38250 | Windows Graphics Component Elevation of Privilege Vulnerability |
| CVE-2024-38252 | Windows Win32 Kernel Subsystem Elevation of Privilege Vulnerability |
| CVE-2024-38253 | Windows Win32 Kernel Subsystem Elevation of Privilege Vulnerability |
| CVE-2024-43457 | Windows Setup and Deployment Elevation of Privilege Vulnerability |
| CVE-2024-43465 | Microsoft Excel Elevation of Privilege Vulnerability |
| CVE-2024-43470 | Azure Network Watcher VM Agent Elevation of Privilege Vulnerability |
| CVE-2024-43492 | Microsoft AutoUpdate (MAU) Elevation of Privilege Vulnerability |
Remote Code Execution (23 CVEs)
| Critical severity | |
| CVE-2024-38018 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
| CVE-2024-38119 | Windows Network Address Translation (NAT) Remote Code Execution Vulnerability |
| CVE-2024-43464 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
| CVE-2024-43491 | Microsoft Windows Update Remote Code Execution Vulnerability |
| Important severity | |
| CVE-2024-21416 | Windows TCP/IP Remote Code Execution Vulnerability |
| CVE-2024-26186 | Microsoft SQL Server Native Scoring Remote Code Execution Vulnerability |
| CVE-2024-26191 | Microsoft SQL Server Native Scoring Remote Code Execution Vulnerability |
| CVE-2024-37335 | Microsoft SQL Server Native Scoring Remote Code Execution Vulnerability |
| CVE-2024-37338 | Microsoft SQL Server Native Scoring Remote Code Execution Vulnerability |
| CVE-2024-37339 | Microsoft SQL Server Native Scoring Remote Code Execution Vulnerability |
| CVE-2024-37340 | Microsoft SQL Server Native Scoring Remote Code Execution Vulnerability |
| CVE-2024-38045 | Windows TCP/IP Remote Code Execution Vulnerability |
| CVE-2024-38227 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
| CVE-2024-38228 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
| CVE-2024-38259 | Microsoft Management Console Remote Code Execution Vulnerability |
| CVE-2024-38260 | Windows Remote Desktop Licensing Service Remote Code Execution Vulnerability |
| CVE-2024-38263 | Windows Remote Desktop Licensing Service Remote Code Execution Vulnerability |
| CVE-2024-43454 | Windows Remote Desktop Licensing Service Remote Code Execution Vulnerability |
| CVE-2024-43463 | Microsoft Office Visio Remote Code Execution Vulnerability |
| CVE-2024-43467 | Windows Remote Desktop Licensing Service Remote Code Execution Vulnerability |
| CVE-2024-43469 | Azure CycleCloud Remote Code Execution Vulnerability |
| CVE-2024-43479 | Microsoft Power Automate Desktop Remote Code Execution Vulnerability |
| CVE-2024-43495 | Windows libarchive Remote Code Execution Vulnerability |
Information Disclosure (11 CVEs)
| Important severity | |
| CVE-2024-37337 | Microsoft SQL Server Native Scoring Information Disclosure Vulnerability |
| CVE-2024-37342 | Microsoft SQL Server Native Scoring Information Disclosure Vulnerability |
| CVE-2024-37966 | Microsoft SQL Server Native Scoring Information Disclosure Vulnerability |
| CVE-2024-38254 | Windows Authentication Information Disclosure Vulnerability |
| CVE-2024-38256 | Windows Kernel-Mode Driver Information Disclosure Vulnerability |
| CVE-2024-38257 | Microsoft AllJoyn API Information Disclosure Vulnerability |
| CVE-2024-38258 | Windows Remote Desktop Licensing Service Information Disclosure Vulnerability |
| CVE-2024-43458 | Windows Networking Information Disclosure Vulnerability |
| CVE-2024-43474 | Microsoft SQL Server Information Disclosure Vulnerability |
| CVE-2024-43475 | Microsoft Windows Admin Center Information Disclosure Vulnerability |
| CVE-2024-43482 | Microsoft Outlook for iOS Information Disclosure Vulnerability |
Denial of Service (8 CVEs)
| Important severity | |
| CVE-2024-38230 | Windows Standards-Based Storage Management Service Denial of Service Vulnerability |
| CVE-2024-38231 | Windows Remote Desktop Licensing Service Denial of Service Vulnerability |
| CVE-2024-38232 | Windows Networking Denial of Service Vulnerability |
| CVE-2024-38233 | Windows Networking Denial of Service Vulnerability |
| CVE-2024-38234 | Windows Networking Denial of Service Vulnerability |
| CVE-2024-38235 | Windows Hyper-V Denial of Service Vulnerability |
| CVE-2024-38236 | DHCP Server Service Denial of Service Vulnerability |
| CVE-2024-43466 | Microsoft SharePoint Server Denial of Service Vulnerability |
Security Feature Bypass (4 CVEs)
| Important severity | |
| CVE-2024-30073 | Windows Security Zone Mapping Security Feature Bypass Vulnerability |
| CVE-2024-38217 | Windows Mark of the Web Security Feature Bypass Vulnerability |
| CVE-2024-38226 | Microsoft Publisher Security Features Bypass Vulnerability |
| Moderate severity | |
| CVE-2024-43487 | Windows Mark of the Web Security Feature Bypass Vulnerability |
Spoofing (3 CVEs)
| Important severity | |
| CVE-2024-43455 | Windows Remote Desktop Licensing Service Spoofing Vulnerability |
| CVE-2024-43461 | Windows MSHTML Platform Spoofing Vulnerability |
| CVE-2024-43476 | Microsoft Dynamics 365 (on-premises) Cross-site Scripting Vulnerability |
Appendix B: Exploitability
This is a list of the September CVEs judged by Microsoft to be either under exploitation in the wild or more likely to be exploited in the wild within the first 30 days post-release. The list is arranged by CVE. In the case of CVE-2024-43491, the issue itself is not known to be under active exploit, but certain of the issues fixed by the rejected servicing-stack updates are, so we are choosing to include it on this list. (Please see the “Notable September updates” section above for context.)
| Exploitation detected | |
| CVE-2024-38014 | Windows Installer Elevation of Privilege Vulnerability |
| CVE-2024-38217 | Windows Mark of the Web Security Feature Bypass Vulnerability |
| CVE-2024-38226 | Microsoft Publisher Security Features Bypass Vulnerability |
| CVE-2024-43491 | Microsoft Windows Update Remote Code Execution Vulnerability |
| Exploitation more likely within the next 30 days | |
| CVE-2024-38018 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
| CVE-2024-38227 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
| CVE-2024-38228 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
| CVE-2024-38237 | Kernel Streaming WOW Thunk Service Driver Elevation of Privilege Vulnerability |
| CVE-2024-38238 | Kernel Streaming Service Driver Elevation of Privilege Vulnerability |
| CVE-2024-38241 | Kernel Streaming Service Driver Elevation of Privilege Vulnerability |
| CVE-2024-38242 | Kernel Streaming Service Driver Elevation of Privilege Vulnerability |
| CVE-2024-38243 | Kernel Streaming Service Driver Elevation of Privilege Vulnerability |
| CVE-2024-38244 | Kernel Streaming Service Driver Elevation of Privilege Vulnerability |
| CVE-2024-38245 | Kernel Streaming Service Driver Elevation of Privilege Vulnerability |
| CVE-2024-38246 | Win32k Elevation of Privilege Vulnerability |
| CVE-2024-38247 | Windows Graphics Component Elevation of Privilege Vulnerability |
| CVE-2024-38249 | Windows Graphics Component Elevation of Privilege Vulnerability |
| CVE-2024-38252 | Windows Win32 Kernel Subsystem Elevation of Privilege Vulnerability |
| CVE-2024-38253 | Windows Win32 Kernel Subsystem Elevation of Privilege Vulnerability |
| CVE-2024-43457 | Windows Setup and Deployment Elevation of Privilege Vulnerability |
| CVE-2024-43461 | Windows MSHTML Platform Spoofing Vulnerability |
| CVE-2024-43464 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
| CVE-2024-43487 | Windows Mark of the Web Security Feature Bypass Vulnerability |
Appendix C: Products Affected
This is a list of September’s patches sorted by product family, then sub-sorted by severity. Each list is further arranged by CVE. Patches that are shared among multiple product families are listed multiple times, once for each product family.
Windows (47 CVEs)
| Critical severity | |
| CVE-2024-38119 | Windows Network Address Translation (NAT) Remote Code Execution Vulnerability |
| CVE-2024-43491 | Microsoft Windows Update Remote Code Execution Vulnerability |
| Important severity | |
| CVE-2024-21416 | Windows TCP/IP Remote Code Execution Vulnerability |
| CVE-2024-30073 | Windows Security Zone Mapping Security Feature Bypass Vulnerability |
| CVE-2024-38014 | Windows Installer Elevation of Privilege Vulnerability |
| CVE-2024-38045 | Windows TCP/IP Remote Code Execution Vulnerability |
| CVE-2024-38046 | PowerShell Elevation of Privilege Vulnerability |
| CVE-2024-38217 | Windows Mark of the Web Security Feature Bypass Vulnerability |
| CVE-2024-38230 | Windows Standards-Based Storage Management Service Denial of Service Vulnerability |
| CVE-2024-38231 | Windows Remote Desktop Licensing Service Denial of Service Vulnerability |
| CVE-2024-38232 | Windows Networking Denial of Service Vulnerability |
| CVE-2024-38233 | Windows Networking Denial of Service Vulnerability |
| CVE-2024-38234 | Windows Networking Denial of Service Vulnerability |
| CVE-2024-38235 | Windows Hyper-V Denial of Service Vulnerability |
| CVE-2024-38236 | DHCP Server Service Denial of Service Vulnerability |
| CVE-2024-38237 | Kernel Streaming WOW Thunk Service Driver Elevation of Privilege Vulnerability |
| CVE-2024-38238 | Kernel Streaming Service Driver Elevation of Privilege Vulnerability |
| CVE-2024-38239 | Windows Kerberos Elevation of Privilege Vulnerability |
| CVE-2024-38240 | Windows Remote Access Connection Manager Elevation of Privilege Vulnerability |
| CVE-2024-38241 | Kernel Streaming Service Driver Elevation of Privilege Vulnerability |
| CVE-2024-38242 | Kernel Streaming Service Driver Elevation of Privilege Vulnerability |
| CVE-2024-38243 | Kernel Streaming Service Driver Elevation of Privilege Vulnerability |
| CVE-2024-38244 | Kernel Streaming Service Driver Elevation of Privilege Vulnerability |
| CVE-2024-38245 | Kernel Streaming Service Driver Elevation of Privilege Vulnerability |
| CVE-2024-38246 | Win32k Elevation of Privilege Vulnerability |
| CVE-2024-38247 | Windows Graphics Component Elevation of Privilege Vulnerability |
| CVE-2024-38248 | Windows Storage Elevation of Privilege Vulnerability |
| CVE-2024-38249 | Windows Graphics Component Elevation of Privilege Vulnerability |
| CVE-2024-38252 | Windows Win32 Kernel Subsystem Elevation of Privilege Vulnerability |
| CVE-2024-38253 | Windows Win32 Kernel Subsystem Elevation of Privilege Vulnerability |
| CVE-2024-38254 | Windows Authentication Information Disclosure Vulnerability |
| CVE-2024-38256 | Windows Kernel-Mode Driver Information Disclosure Vulnerability |
| CVE-2024-38257 | Microsoft AllJoyn API Information Disclosure Vulnerability |
| CVE-2024-38258 | Windows Remote Desktop Licensing Service Information Disclosure Vulnerability |
| CVE-2024-38259 | Microsoft Management Console Remote Code Execution Vulnerability |
| CVE-2024-38260 | Windows Remote Desktop Licensing Service Remote Code Execution Vulnerability |
| CVE-2024-38263 | Windows Remote Desktop Licensing Service Remote Code Execution Vulnerability |
| CVE-2024-43454 | Windows Remote Desktop Licensing Service Remote Code Execution Vulnerability |
| CVE-2024-43455 | Windows Remote Desktop Licensing Service Spoofing Vulnerability |
| CVE-2024-43457 | Windows Setup and Deployment Elevation of Privilege Vulnerability |
| CVE-2024-43458 | Windows Networking Information Disclosure Vulnerability |
| CVE-2024-43461 | Windows MSHTML Platform Spoofing Vulnerability |
| CVE-2024-43467 | Windows Remote Desktop Licensing Service Remote Code Execution Vulnerability |
| CVE-2024-43475 | Microsoft Windows Admin Center Information Disclosure Vulnerability |
| CVE-2024-43495 | Windows libarchive Remote Code Execution Vulnerability |
| Moderate severity | |
| CVE-2024-43487 | Windows Mark of the Web Security Feature Bypass Vulnerability |
SQL Server (13 CVEs)
| Important severity | |
| CVE-2024-26186 | Microsoft SQL Server Native Scoring Remote Code Execution Vulnerability |
| CVE-2024-26191 | Microsoft SQL Server Native Scoring Remote Code Execution Vulnerability |
| CVE-2024-37335 | Microsoft SQL Server Native Scoring Remote Code Execution Vulnerability |
| CVE-2024-37337 | Microsoft SQL Server Native Scoring Information Disclosure Vulnerability |
| CVE-2024-37338 | Microsoft SQL Server Native Scoring Remote Code Execution Vulnerability |
| CVE-2024-37339 | Microsoft SQL Server Native Scoring Remote Code Execution Vulnerability |
| CVE-2024-37340 | Microsoft SQL Server Native Scoring Remote Code Execution Vulnerability |
| CVE-2024-37341 | Microsoft SQL Server Elevation of Privilege Vulnerability |
| CVE-2024-37342 | Microsoft SQL Server Native Scoring Information Disclosure Vulnerability |
| CVE-2024-37965 | Microsoft SQL Server Elevation of Privilege Vulnerability |
| CVE-2024-37966 | Microsoft SQL Server Native Scoring Information Disclosure Vulnerability |
| CVE-2024-37980 | Microsoft SQL Server Elevation of Privilege Vulnerability |
| CVE-2024-43474 | Microsoft SQL Server Information Disclosure Vulnerability |
Azure (6 CVEs)
| Critical severity | |
| CVE-2024-38194 | Azure Web Apps Elevation of Privilege Vulnerability |
| CVE-2024-38216 | Azure Stack Hub Elevation of Privilege Vulnerability |
| CVE-2024-38220 | Azure Stack Hub Elevation of Privilege Vulnerability |
| Important severity | |
| CVE-2024-38188 | Azure Network Watcher VM Agent Elevation of Privilege Vulnerability |
| CVE-2024-43469 | Azure CycleCloud Remote Code Execution Vulnerability |
| CVE-2024-43470 | Azure Network Watcher VM Agent Elevation of Privilege Vulnerability |
SharePoint (5 CVEs)
| Critical severity | |
| CVE-2024-38018 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
| CVE-2024-43464 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
| Important severity | |
| CVE-2024-38227 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
| CVE-2024-38228 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
| CVE-2024-43466 | Microsoft SharePoint Server Denial of Service Vulnerability |
Office (4 CVE)
| Important severity | |
| CVE-2024-38226 | Microsoft Publisher Security Features Bypass Vulnerability |
| CVE-2024-38250 | Windows Graphics Component Elevation of Privilege Vulnerability |
| CVE-2024-43463 | Microsoft Office Visio Remote Code Execution Vulnerability |
| CVE-2024-43465 | Microsoft Excel Elevation of Privilege Vulnerability |
365 (2 CVE)
| Important severity | |
| CVE-2024-43463 | Microsoft Office Visio Remote Code Execution Vulnerability |
| CVE-2024-43465 | Microsoft Excel Elevation of Privilege Vulnerability |
Dynamics 365 (2 CVE)
| Important severity | |
| CVE-2024-38225 | Microsoft Dynamics 365 Business Central Elevation of Privilege Vulnerability |
| CVE-2024-43476 | Microsoft Dynamics 365 (on-premises) Cross-site Scripting Vulnerability |
Microsoft AutoUpdate (MAU) for Mac (1 CVE)
| Important severity | |
| CVE-2024-43492 | Microsoft AutoUpdate (MAU) Elevation of Privilege Vulnerability |
Outlook for iOS (1 CVE)
| Important severity | |
| CVE-2024-43482 | Microsoft Outlook for iOS Information Disclosure Vulnerability |
PowerBI (1 CVE)
| Important severity | |
| CVE-2024-43479 | Microsoft Power Automate Desktop Remote Code Execution Vulnerability |
Visio (1 CVE)
| Important severity | |
| CVE-2024-43463 | Microsoft Office Visio Remote Code Execution Vulnerability |
Appendix D: Advisories and Other Products
This is a list of advisories and information on other relevant CVEs in the September release, sorted by product.
Relevant to Adobe (non-Microsoft release) (3 CVEs)
| CVE-2024-41869 | APSB24-70 | Use After Free (CWE-416) |
| CVE-2024-41874 | APSB24-71 | Deserialization of Untrusted Data (CWE-502) |
| CVE-2024-39420 | APSB24-70 | Time-of-check Time-of-use (TOCTOU) Race Condition (CWE-367) |