It’s taken nearly ten years, but the US Department of Justice (DOJ) has just announced the court-approved seizure of a web domain called LolekHosted.net that was allegedly connected to a wide range of crimeware-as-a-service activities.
The DOJ also charged a 36-year-old Polish man named Artur Karol Grabowski in connection with running the service, but his current whereabouts are unknown.
In the DOJ’s blunt words, “Grabowski remains a fugitive.”
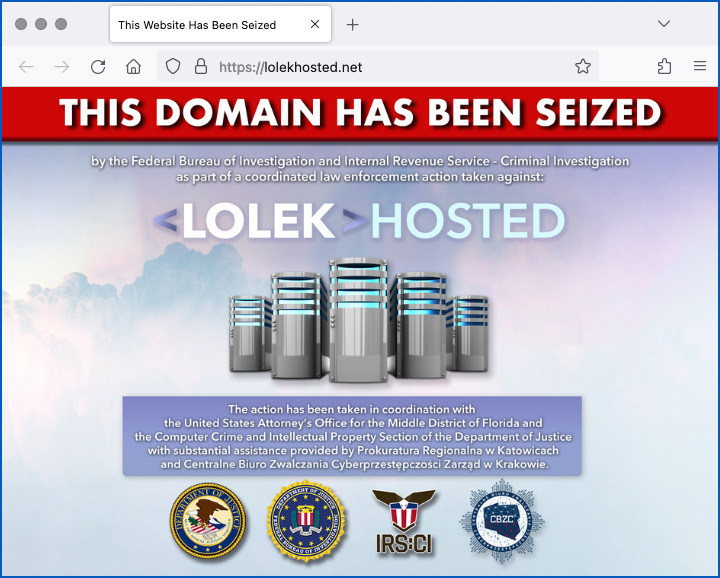
The downed site is still technically online, but now presents a warning notice to visitors:
Bulletproof hosting
Sites of this sort are known in the jargon as bulletproof hosts, whose operators like to claim that they will not only shift around online to resist takedown efforts, but also shield their “customers” from identification even if their assets do get seized.
Indeed, the DOJ alleges that:
Grabowski allegedly facilitated the criminal activities of LolekHosted clients by allowing clients to register accounts using false information, not maintaining Internet Protocol (IP) address logs of client servers, frequently changing the IP addresses of client servers, ignoring abuse complaints made by third parties against clients, and notifying clients of legal inquiries received from law enforcement.
Cybercrime activities allegedly enabled by LolekHosted include: ransomware attacks; system penetration attempts via what’s known as brute force attacks (for example, where attackers try logging into thousands of different servers with millions of different passwords each); and phishing.
As you probably know, ransomware criminals typically use anonymous darkweb hosts for contact purposes when they’re “negotiating” their blackmail payoffs.
Those darkweb servers are usually hosted in the largely anonymous Tor network, with server names ending in .onion.
So-called onion addresses aren’t part of the regular internet domain name system (DNS), so they can’t be looked up or traced using conventional tools, and they require ransomware victims to to setup and use a special Tor-enabled browser to access them pseudoanonymously.
In the build-up to an attack, however, and even while the attack is under way, ransomware crooks often need innocently-styled URLs on the regular “brightweb”.
For example, attackers often set up legitimate-looking sites as download repositories for their malware and hacking tools, as jumping-off points for mounting attacks, and as upload servers to which they can exfiltrate stolen files without arousing immediate suspicion.
According to the DOJ, Grabowski’s customers included numerous affiliates of the notorious NetWalker ransomware gang, with LoledHosted servers implicated in:
approximately 50 NetWalker ransomware attacks on victims located all over the world, including in the Middle District of Florida [where Grabowski is being charged]. Specifically, clients used the servers of LolekHosted as intermediaries when gaining unauthorized access to victim networks, and to store hacking tools and data stolen from victims.
What next?
If caught and convicted, the DOJ says that it is seeking a to recover a whopping $21,500,000 in forfeited funds from Grabowski, a sum that the DOJ claims matches the proceeds of the criminal activities with which he has been charged.
We don’t know what happens if Grabowski gets caught and won’t or can’t come up with the money, but the DOJ also points out that the maximum jail-time penalty he faces if convicted on all charges (for all that maxiumum sentences are rarely imposed) comes to 45 years.

Anon
That guy is probably living like a king somewhere that he can’t be extradited. Russia, China etc. Lots of luck. 10 years is a long time for a take down.
Paul Ducklin
Never say never. Russia and China don’t extradite ther own citizens (suprisingly many countries don’t), but I don’t think the same constitutional protection applies to foreigners who happen to go or be there.
The suspect in this case is a Polish national, apparently from Poland, so although it’s conceivable he might also have a Russian passport, it seems unlikey he’d have dual nationality with PRC or any of the other likely “etc.” countries, such as DPNK.
Although there are EU countries with extradition protection for citizens (I think France and Germany are two examples), even if he’s in one of those right now and has the right nationality to avoid being sent to the US, he’d probably end up getting prosecuted in that country anyway, if the crime were considered serious enough. That’s how these “can’t be extradited” rules often work out. The US sends the evidence to the other country and they take on the case there.
Bill boy Abbot
That CBZC logo looks straight out of a movie (in a good way).
H Davis
I think that if it takes 10 years and who knows how many man-hours to catch just one of these guys then the crooks have a better business model than any of the high tech companies.h