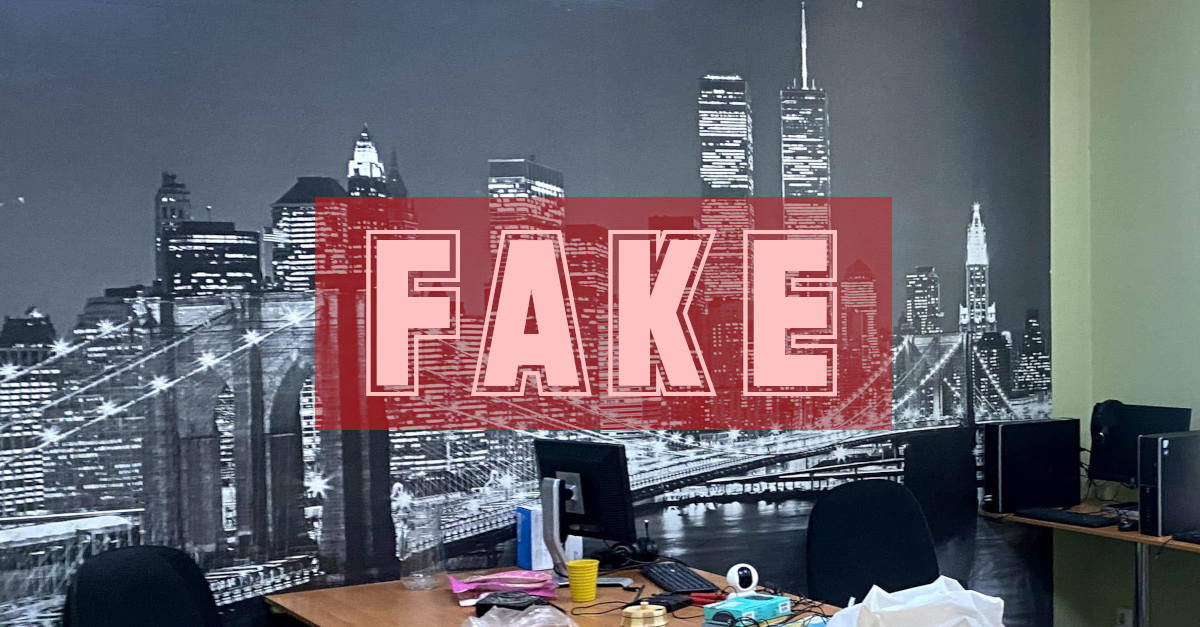
It looks like the sort of meeting room you might find in startups all over the world: diffuse lighting from windows down one wall, alongside a giant poster cityscape of New York’s Brooklyn Bridge, with the Manhattan skyline towering behind it.
The difference in this case is that that the computer workstations around the room are there for a different sort of “entrepreneurial” venture, and the room is empty not because no one showed up for work, but because the “employees” were in the process of being arrested.
This picture comes from the Ukraine Cyber Police, who raided a fraudulent call centre just before New Year, where they say the three founders of the scam, plus 37 “staff”, were busted for allegedly operating a large-scale banking fraud.
Playbook + gift of gab = scam
You’re probably familiar with the scamming script they’re said to have used, and you probably know friends or family who have been pestered by scammers of this sort.
Some of you may even have acquaintances who were ripped off this way, because these scammers are well versed in gaining the trust of their victims.
Typically, the scammers try to convince you that your bank account is under attack from fraudsters (technically, that part is true – the caller is the attacker), and patiently offer to help you “secure” your account and “recover” lost or at-risk funds.
The scammers aim to turn people’s general awareness of banking scams into an excuse, a reason, a playbook, if you like, for carrying out a scam of their own.
Simply put, they call up pretending to be an official from your own bank, using a variety of tricks to make you accept their fictitious credentials as bank staff, and then “advise” you to take a series of disastrous steps.
IMPORTANT. Remember that the number that pops up on your phone when someone calls you cannot be relied on. Scammers can inject fake numbers into the calling process to make it look as though they’re calling from almost anywhere: from your bank’s HQ; from an official helpline number;from the tax office; even from your local police station. Also remember also that if you call someone back based on a number they gave you, even if the number is a tollfree number inside your country, you could end up invisibly redirected almost anywhere in the world. Scammers can even buy ready-to-go “spoofed” telephone services from other cybercriminals, so they don’t need any internet telephony knowhow themselves.
The scammers’ first job is to convince you that a hacker has already gained access to your account.
The crooks typically use a mix of threatening, scary and urgent language, combined with the sort of attentiveness that you probably wish more call centre staff would show.
Even if you decide to call them back (don’t do it – you’re only reconnecting to the person who just called you, which proves nothing!), you’ll almost certainly find the scammers more prompt and more helpful than you’ve experienced in a long time when calling a real support line…
…so we’re not surprised that this sort of caller makes some people feel comfortable enough to keep on listening, even if they didn’t believe a word at first.
If in doubt, don’t give it out
As you can imagine, once the crooks know you’re starting to believe their cover story, they’ll start to milk you for personal information, often by pretending that they can see it for themselves on the “banking screen” in front of them, yet somehow always coaxing you to say it out loud first.
At that point, of course, they do know the information you just let slip, and they’ll pretend to “confirm” it or to “double-check” it to keep up the pretence.
There are then many ways that the crooks can defraud you or drain your account.
Sometimes, they may simply convince you to login on a fake “security” site as they coach you through the process, including getting you to go through any 2FA (two-factor authentication) process.
The Ukrainian call centre that just got busted seems to have worked that way, with victims being “helpfully” guided through the process of “cancelling” transactions that, in fact, never happened in the first place [automated translation]:
[These scammers] called people in Kazakhstan, pretending to be employees of the security service of banks. These people were notified of suspicious transactions and told that alleged outsiders had gained access to their accounts. Under the guise of “cancelling” transactions, victims were persuaded to provide financial data.
After receiving such information, the perpetrators transferred the victims’ money to account under their own control. They also issued quick loans and appropriated the loan amount.
For the conspiracy, the participants used bank accounts located in offshore zones, and cryptocurrency wallets.
In this way, the criminals defrauded [about 18,000 people].
High and dry
In other scams – this approach, unfortunately, is widely reported in the UK – the crooks present you with a brand-new account number, based at the same bank, which they announce is your “replacement account”.
The idea is that you’re being provided with new account details in the same way that if you were to ask for a new credit card due to fraud, it too would have a brand new number, expiry date and so on.
The crooks then convince you to transfer the funds from your “old, hacked” account to this new one, leading you to believe that the account was created by the bank minutes ago, especially for the purpose of “protecting” you from an active attack.
Of course, this “new account” is just a regular account that was opened recently by accomplices of the crooks, perhaps using fraudulent documentation to pass the bank’s know-your-customer (KYC) process.
So, the account it is already directly under the control of the scammers, and the money will typically be whisked out of that “new” account even before you finish the call.
In cases like this, victims sometimes tragically find themselves left high and dry by their bank, which may claim that because they apparently willingly transferred the funds of their own accord, and properly identified themselves to the online banking system (for example by using 2FA), the funds have technically not been “stolen”, and the bank therefore has no liability.
What to do?
- Never believe anyone who contacts you out of the blue and claims to be “helping” you with a fraud investigation. That person isn’t stopping a fraud, they are starting one.
- Never use contact details given to you by the other person when cybersecurity is at stake. This cannot possibly prove anything, given that the details probably came from a scammer in the first place. All you get is a false sense of “security”.
- Never rely on the Caller ID number that shows up on your phone. The number that appears can easily be faked. If the caller tells you to “check the number if you don’t believe them”, you can be sure they’re a scammer.
- Never let yourself be talked into handing over personal information, especially not to “prove” your identity. After all, it’s the other person who should be proving themselves to you. Visit your bank in person if you possibly can; if you need to call or interact online, look for contact details printed on something you know you received directly from the bank, such as the back of your payment card or a recent statement.
- Never transfer funds to another account on someone else’s say so. You bank will never call you to ask you to do this, so any call of this sort must be a scam. Worse still, you could find yourself liable for the transfer if you approve it yourself, even if you were tricked into doing so.
- Look out for friends and family who may be vulnerable. These scammers don’t give up easily, and they can be consummate actors when playing the role of a helpful official. Make sure your friends and family know to hang up right away, and to contact you personally for advice, so they never give the scammers a chance to “vouch” for themselves.
NO NEED TO GET UP – WE’LL LET OURSELVES IN
4caster
I agree. If someone calls you purporting to be your bank, it is probably a scam, but might just be genuine.
End the call, and if you think it might be genuine, call the number printed on your bank card. But wait a few minutes first, for the line to clear, or preferably call the bank from a different line. For example if the call came to your mobile, call the bank from a landline or another mobile.
Paul Ducklin
I’m not sure how long the caller gets to “hold the line open” in these post-pulse-dialling days… but that used to be a huge problem in the electromechanical era. If the caller didn’t hang up at the end of the call then your line would probably still end up “circuit switched” to their phone when you next went to call out. Therefore if they were sneaky they could wait until they heard you come back on the line, play you a dialling tone, listen in to the number you thought you were dialling (count the pulses) and then pretend to answer, *even though you were electrically part of the same call as before*.
This was a massive risk for so-called dial-back modems, which would automatically hang up on connection and call your number back, both for “added security” and so the company bore the cost of the call. Often easily spoofed…
Charles Palmer
Well researched and written. More of these articles needed!
This type of USE case narratives needs to be propagated far and wide.
I know too many folks who have been duped by these calls and the banks leverage as much wriggle room here as they can. Since I turned 70, I have been swamped with these types of calls.
I have been a Business/Solutions/Information architect for 20+ years and prior to that an ICT auditor for 10 and prior to that, an assembly developer. I also teach Cyber Sec part time at Post Graduate level.
Paul Ducklin
It’s easy to say “what WERE the victims thinking?”, but today’s know-your-customer rules mean that people expect to get pestered for identifying data by the bank… and, as I said in the article, it’s not a big leap from “I get a new credit card number every time it’s reissued, and I have to choose a new PIN, and the CVV code changes”, so why not a new bank account number, if it really has been hacked?
Raffles
Just tell them that you will go to your bank at the earliest opportunity and fix any problems in person. Ask them for reference numbers. Refuse all telephonic assistance.
Paul Ducklin
That’s what I do… but my local branch closed recently, presumably to boost shareholder value, and so did every other competing bank’s branch in the immediate area. Fortunately I still have a branch within a reasonable distance, but lots of others haven’t been so lucky.
John Lord
Scammers lair has a background poster showing the WTC twin towers that I would like to get for myself.
Derek Smith
High street banks continue to close branches because they are under utilised. I noticed some closures around Scotland recently which were leaving branches only in large cities, some a convenient 90 miles distant, others a flight or ferry journey away. Not so bad in areas of dense population, but banks now require customers to use the internet – so they should be improve guidance and assistance with this, and be ready to adapt methods, particularly for long standing customers.. Most banks seem too focussed on their own security to the detriment of customer service.