Today, we released new Sophos research into a series of Microsoft SQL Server attacks. We also released a new piece outlining our vision of how security operations can and will be enhanced and improved by machine learning and artificial intelligence: “Building the AI-Driven SOC: Sophos’ 5-Year Perspective.” Finally, today we announced the launch of Sophos X-Ops, a new cross-operational unit that links together three established teams of cybersecurity experts at Sophos: SophosLabs, SecOps (Managed Threat Response, Rapid Response and Sophos Security) and Sophos AI to provide stronger, more innovative protection, detection and response capabilities for our customers.
Fragmentation of security research and response is a well-known problem across the industry, and one that gives attackers an advantage. At Sophos, we believe that the right answer is to bring our multiple areas of capability and expertise together in a joint task force model to match and counter each unique threat. In this posting, I want to show what that means in practical, nuts-and-bolts terms using specific research, so you can see how Sophos X-Ops functions in action. 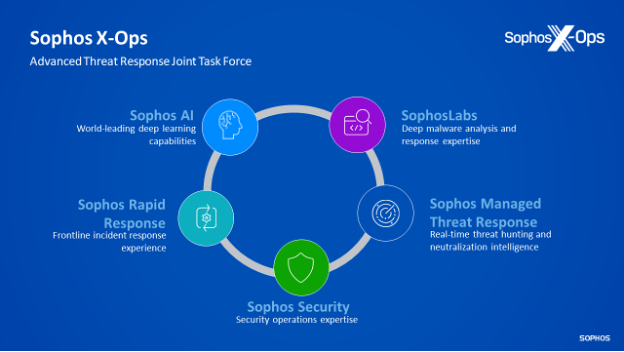
The research we’re releasing discusses a series of attempted attacks against Microsoft SQL Servers unpatched for known vulnerabilities. We believe the threat group behind these attacks is likely responsible for multiple incidents in the first half of 2022, mainly affecting organizations in the Americas and Asia. The ultimate goal of these attacks was to gain a foothold on vulnerable systems, compromise more systems, and deploy ransomware.
Sophos X-Ops teams work together in an ongoing, virtuous cycle of constant collaboration. For instance, in this case, SophosLabs, aided by intelligence and tools from Sophos AI, builds detections into our Intercept X product: Intercept X was able to detect and prevent the ransomware these attackers were seeking to deploy. Specifically, our CryptoGuard technology detected and blocked the deployment of this ransomware. It’s also worth noting that Intercept X prevented the ransomware’s attempts to disable the endpoint security. Altogether Intercept X was able to deny the attackers a safe space from which to launch further attacks against the network and systems on it.
Our Managed Threat Response (MTR) team, a part of SecOps, which provides ongoing 24x7x365 live monitoring and response to protect customer systems, noticed a series of detections for this ransomware family. The team began to investigate to better understand the context and indicators of compromise behind these attempts.
In this investigation, the MTR and SophosLabs teams collaborated to understand how the malware functions and how it was being deployed in the live environment.
Meanwhile, our Rapid Response team, also a part of SecOps, had been engaged separately to help combat an attempted deployment of the same ransomware at a different organization. The Rapid Response team used Intercept X to help prevent the deployment of ransomware and was able to gather more specific, real-world details about how these attacks were unfolding. As part of their work, Rapid Response conferred with SophosLabs and MTR, and they shared information from their areas of specialty and expertise to build out a fuller picture of the malware and the actual real-world attack chain. After the attack was quashed, Rapid Response wrapped up with the client and MTR stepped in, as is Sophos practice, for a period of after-event monitoring.
This fuller, fleshed-out picture was then used by SophosLabs to build even better protections into our products as well as provide even more data that can be used by Sophos AI to train the machine learning that helps power protections.
Finally, all of these teams worked together to assemble and publish the research we released today so that defenders can learn from what we’ve learned and better protect their organization.
We believe that information sharing is a crucial component in the cybersecurity industry, so another key part of Sophos X-Ops is our newly updated Sophos X-Ops blog and Twitter handle as well as participating in programs such as the Cyber Threat Alliance (CTA) and Microsoft Active Protections Program. Through the CTA for instance, the detection information that is in our Intercept X product gets shared with all other CTA members, enabling their customers to also be protected.
Today’s Sophos X-Ops announcement is just the start: all of our information gathered, analyzed, and shared leads to stopping more attacks, which leads to more information about how those attacks work. The cycle continues, with the Sophos X-Ops constantly working together — because attackers themselves are also working together to constantly update their attack methods in an attempt to outwit defenders.
Sophos customers and everyone are better protected and informed because we assemble these different teams with complementary knowledge, expertise, and intelligence to provide the fullest, broadest picture of threats possible. As Sophos grows and brings more capabilities and expertise together for even fuller research and response, Sophos X-Ops capabilities will naturally grow too. Watch this space!
For more information on Sophos X-Ops, please see our FAQ.

Leave a Reply