Even if you’re not a native speaker of English, you’ve probably heard the curious saying, “It’s a bit of a Curate’s Egg”, referring to something about which you’re determined to keep a positive public attitude, even if your immediate private reaction was to be disappointed.
The saying has certainly stood the test of time, coming as it does from a British satiricial cartoon from the late 1800s, in which a young curate has been invited to breakfast with the bishop.
(A curate is an Anglican church minister in their first job, right at the bottom of the clerical hierarchy, while a bishop is in the uppermost levels of church staff.)
Loosely speaking, the cartoon depicts the modern business equivalent of an intern who finds themelves in the midst of a lunch meeting of senior VPs: a promising but vaguely intimidating situation, with the very real danger of not getting a second chance to make a good first impression.
The British, of course, are well-known for eating boiled eggs at breakfast time, and in the Victorian era, there were no food labelling regulations to tell you how long your eggs had been in the supply chain, so stale eggs were a much more common problem than they are today.
And a boiled egg, still being in its shell when it’s served, doesn’t reveal that it’s gone off until you open it up to eat it…
…whereupon it rapidly reports its rancidity to the rest of the room by releasing a rancorous reek. (It’s a sulfurous smell, but we’d already decided to alliterate with R, so there was no space for a stench soubriquet starting with S in that sentence.)
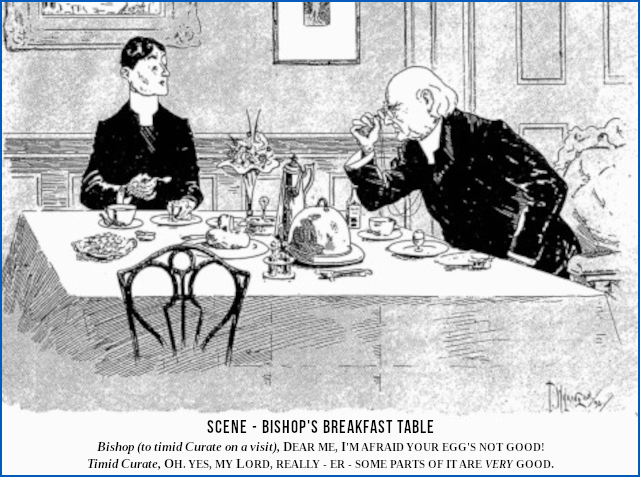
Anyway, in the now-famous cartoon, the bishop is seen apologising to the junior cleric for serving him a bad egg, saying, “Dear me, I’m afraid your egg’s not good!”
The timid curate, for whom both the Ninth Commandment and the aforementioned rancourous reek preclude an outright lie, but for whom politeness and social discretion is the better sort of valour, gamely but absurdly replies, “Some parts of it are very good.”
Which is a long way of warning you how you might react to the news delivered by the Sophos Ransomware Survey 2022, which we published today:
No leading questions
As usual, we didn’t conduct the survey ourselves, to avoid the problem that a cybersecurity company asking respondents cybersecurity questions might be considered “leading the witnesses”.
Surveys overtly connected with vendors often result in answers, like the curate’s remark about the egg, that the respondents thought the experts might like to hear, rather than the bald facts of what really happened.
We also made an effort to keep our sample size high, and to talk to a broad and representative cross-section of the global business community.
We therefore used a survey company to conduct the process, and they asked numerous cybersecurity questions to more than 5500 randomly-chosen respondents from a wide range of businesses of varying sizes in more than 30 countries across the globe.
As with the Curate’s Egg, you’ll find that some parts of the report are indeed very good, but it’s hard to sugar-coat the headline statistic of this year’s survey, which is disappointing.
In our Ransomware 2020 survey, 1/2 of our respondents said that they’d actually had a ransomware infection in the past year (2019).
In our Survey 2021, we were pleased to report that figure was down to about 1/3, with a creditable 63% of respondents saying they’d avoided ransomware altogether during 2020.
But in the Ransomware 2022 survey, the figure has gone up again, with 2/3 of our respondents admitting to a ransomware infection during 2021.
In other words, the underlying prevalence of ransomware attacks has doubled since our previous report, which implies that the size, scale and skills (if we may use that word in this context) of the cybercriminal underworld have increased correspondingly, too.
Not everyone needed to pay up
The upside to that figure is that 1/3 of those who did get hit nevertheless managed to prevent the usual disastrous denoument by heading off the cybercriminals before they were able to unleash the final data-scrambling part of the attack.
In other words, even though all of those who suffered a ransomware intrusion faced an extensive malware cleanup exercise and a possible data breach disclosure to their local regulator, defence-in-depth meant that 33% of them were spared the total derailment of their business that typically happens after a file-encrypting ransomware attack.
Also, just over 1/2 (54%) of those who did get hit, and were faced with the choice of paying up, didn’t hand money to the crooks, but found other ways to recover instead.
Sadly, however, the proportion of victims who refused to pay up is one statistic that has deteriorated over the past three years.
In 2020, just 1/4 of victims said they paid up; in 2021, that was up to 1/3; but in 2022, as we just said, the figure was close to 1/2.
What to do?
Our Top Tips are:
- Ensure high-quality defences at all points in your environment. Review your security controls and make sure they continue to meet your needs. As the ever-increasing success of ransomware criminals reminds us, cybersecurity is a journey, not a destination. The security precautions you picked back in 2019 aren’t necessarily the right ones for today, because “set-and-forget” just doesn’t work in the cybersecurity game.
- Proactively hunt for threats so you can stop adversaries before they can execute their attack. If you don’t have the time or skills in-house, look for a Managed Detection and Response (MDR) specialist to help you out. The file-scrambling part of a ransomware incident may unfold within a few hours, or even in a matter of minutes, with the criminals deliberately scheduling the coup de grace for a specific, and usually inconvenient, time of day (or night). But when our own Managed Threat Reponse (MTR) experts are called in to investigate attacks after they’ve occurred, they frequently find tell-tale signs going back days, or even weeks, that could have been used as a tip-off to close down the attack and eject the criminals in time.
- Harden your environment by searching for and closing down security gaps such as unpatched devices, unprotected computers, insecure remote access servers, and more. Cybersecurity products with Extended Detection and Response (XDR) features are ideal for this purpose, because they allow you to close the gap between your cybersecurity policy (see Tip 1) and your cybersecurity practice (see Tip 2). If you don’t search for exploitable holes in your network, you can be sure that the crooks will!
- Prepare for the worst. Know what to do if a cyberattack occurs, and whom you need to contact, especially if your local laws require formal and speedy data breach disclosures. Preparing for a cyberattack is not an admission that you expect to fail. Indeed, regular and purposeful practice can help you improve your resilience by exposing places where you haven’t followed Tip 1, Tip 2 and Tip 3 as robustly as you thought.
- Make backups, and practise restoring from them. A backup that you can’t reliably and rapidly restore doesn’t count, so you might as well not bother making backups in the first place if they aren’t going to be any use. Your goal is to get back up and running quickly, with minimum disruption, and without being forced to pay blackmail money to the crimnals.
Remember that although the Ransomware Survey 2022 reports that 2/3 of respondents were ransomware victims, more than 1/2 of them recovered without paying up, suggesting that they not only had backups handy, but were able to restore them in a timely way.
As we like to say on Sophos Naked Security:
The only backup you will ever regret is the one you didn’t make.
Time to act!
If you don’t have the experience or the time to maintain ongoing threat response by yourself, consider partnering with a service like Sophos Managed Threat Response. We help you take care of the activities you’re struggling to keep up with because of all all the other daily demands that IT dumps on your plate.
Not enough time or staff?
Learn more about Sophos Managed Detection and Response:
24/7 threat hunting, detection, and response ▶


John Flemming
It is a shame that more people are paying up, it will just drive up ransoms and scare more people. Paying rarely gets you back operational anyways, its like flushing down more money year over year.
Paul Ducklin
There’s an amusing (if that is the right word, though I suspect it is not) “ministatistic” in the report that is a good reason not to pay up. Equally amusingly, this stat is matched by a sort-of “other-way-round” detail from last year’s report.
Ransomware 2021: “4% of people who chose to pay up GOT BACK NOTHING AT ALL”
Ransomware 2022: “Only 4% of people who paid up acutally got back everything.”
Given that the entire business proposition of the crooks is that [a] you pay [b] they recover the data for you, these figures are a stark reminder that even with just one, well-defined programming job to do (write an encryption-and-decryption program that actually works), the crooks can’t get things right.
Can you imagine the outcry if, say, Microsoft Bitlocker rendered 4% of Windows computers unusable after installation due to being unable to decrypt its own encryption at all? The outcry if Apple FileVault caused at least some data loss on 96% of Mac computers by running correctly on only 4% of them?
Let’s hope that this is increasingly forcing victims to remember that the crooks are not only crooks, but also have less coding ability that you might reasonably expect give the sort of “fees” they are demanding. Interestingly, although the average ransomware payment this time was over $800,000 (!), this number seems to have been hugely inflated by a small number of countries, notably by Japan, where the average payment was over $4,000,000 (!!). In the US and the UK, for instance, the average payment was much lower at $150,000. Perhaps, even though more victims are willing to pay these days, they’re setting lower thresholds before they drop out of negotiations, due to the implicit understanding that what they are buying is not likely to do the job properly anyway.
Anonymous
Interesting language/history lesson! Btw the word “more” is missing in one paragraph
Paul Ducklin
Fixed, thanks!
REDACTED
Hey, I enjoyed this blog, where you talk about the growth of freelance full-stack developers. One of the great freelancing platforms for freelance developers is [UNWANTED LINK REDACTED]. Take a look at the freelancing platform too. It is a new yet great platform for technical experts.
Paul Ducklin
Legitimate readers may enjoy this comment: it reflects the typical attention to detail shown by comment spammers and scammers. “Hey! Thanks for writing so excellently about [RANDOM CONCEPT THAT THE ARTICLE DOESN’T EVEN MENTION]. Learn more about [RANDOM CONCEPT] by visiting [RANDOM WEBSITE].”
I don’t know what to think: that you couldn’t even be bothered to get your automated comment spambots to make the slightest effort to match topics, or that you genuinely *did* take a look at the content of the article. (Could be both, I suppose.)
Should I despair, or burst into laughter?