In one of the strangest cases I’ve seen in a while, one of my Labs colleagues recently told me about a malware campaign whose primary purpose appears to stray from the more common malware motives: Instead of seeking to steal passwords or to extort a computer’s owner for ransom, this malware blocks infected users’ computers from being able to visit a large number of websites dedicated to software piracy by modifying the HOSTS file on the infected system.
The malware also downloaded and delivered a second malware payload, an executable named ProcessHacker.jpg
Modifying the HOSTS file is a crude but effective method to prevent a computer from being able to reach a web address. It’s crude because, while it works, the malware has no persistence mechanism. Anyone can remove the entries after they’ve been added to the HOSTS file, and they stay removed (unless you run the program a second time). It was also very familiar to me, personally, because I discovered a family of malware more than 10 years ago that performed a nearly identical set of behaviors and wrote up an analysis.
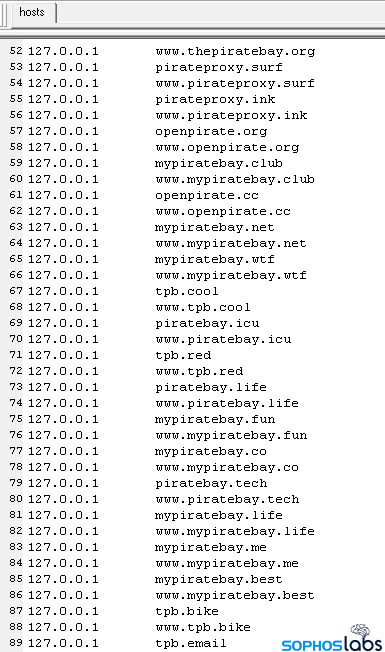
We weren’t able to discern a provenance for this malware, but its motivation seemed pretty clear: It prevents people from visiting software piracy websites (if only temporarily), and sends the name of the pirated software the user was hoping to use to a website, which also delivers a secondary payload. The file adds from a few hundred to more than 1000 web domains to the HOSTS file, pointing them at the localhost address, 127.0.0.1.
Fake games on Discord
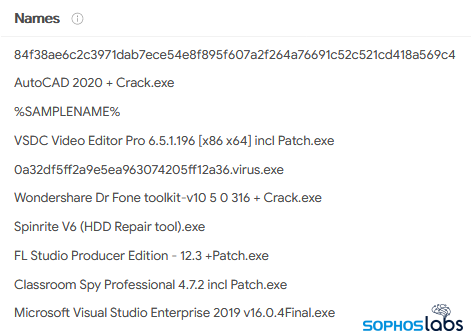
At least some of the malware, disguised as pirated copies of a wide variety of software packages, was hosted on game chat service Discord. Other copies, distributed through Bittorrent, were also named after popular games, productivity tools, and even security products, accompanied by additional files (more on those lower down in the story) that make it appear to have originated with a well-known file sharing account on ThePirateBay.
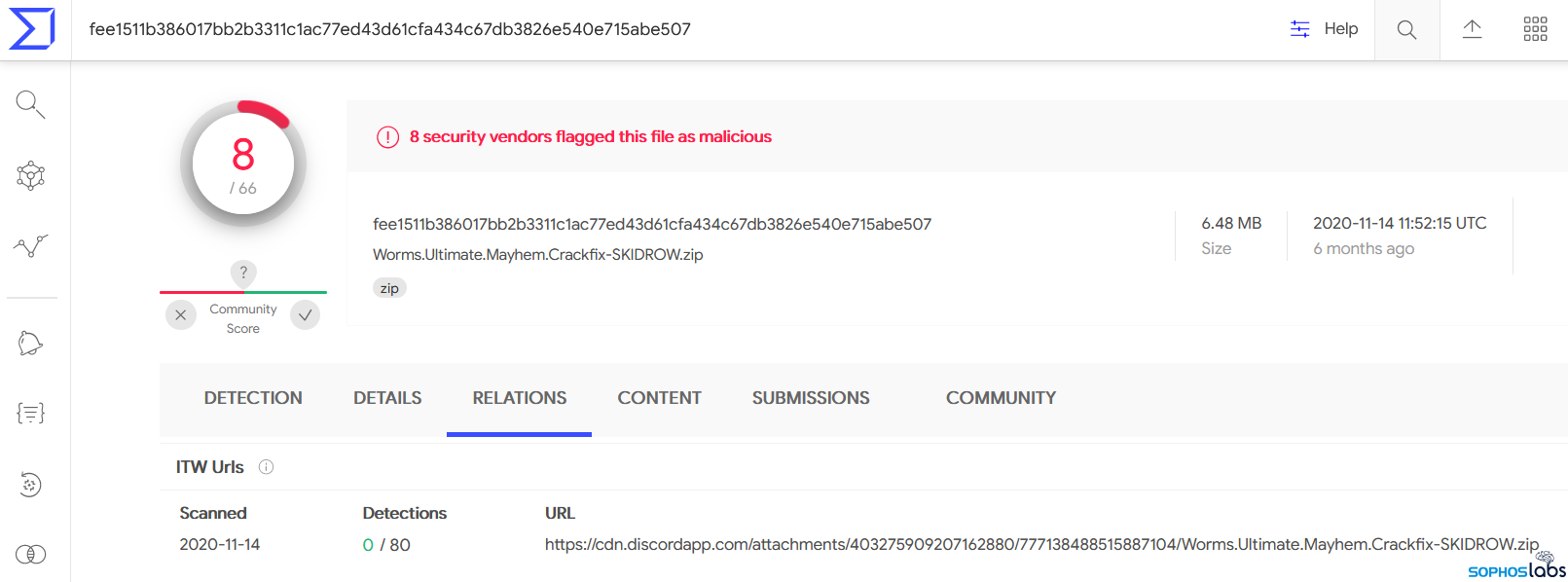
There seem to be hundreds of different software brands represented by the filenames found in a search on Virustotal for related samples. Files like “Left 4 Dead 2 (v2.2.0.1 Last Stand + DLCs + MULTi19)” and “Minecraft 1.5.2 Cracked [Full Installer][Online][Server List]” mimic the naming conventions commonly used to label pirated software.
![]()
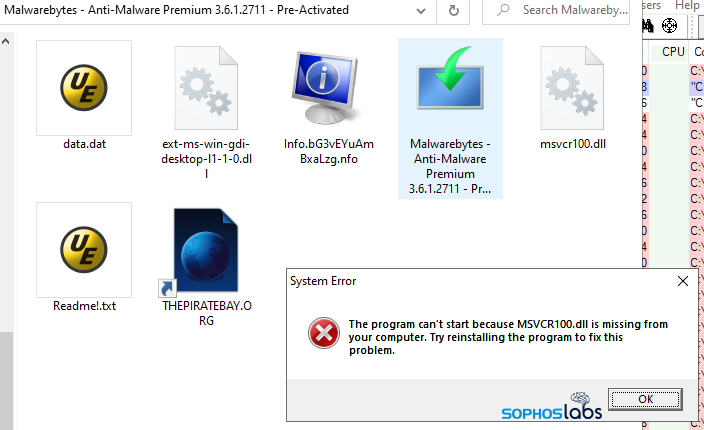
The files that appear to be hosted on Discord’s file sharing tend to be lone executable files. The ones distributed through Bittorrent have been packaged in a way that more closely resembles how pirated software is typically shared using that protocol: Added to a compressed file that also contains a text file and other ancillary files, as well as an old-fashioned Internet Shortcut file pointing to ThePirateBay.
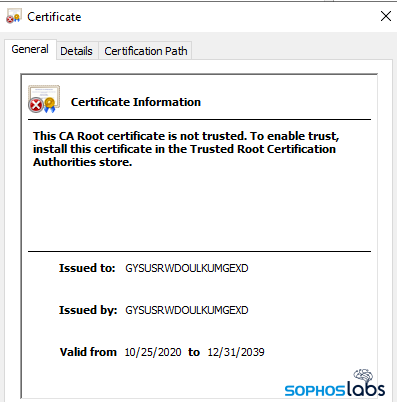
Many, but not all the malware executables were digitally signed by a bogus code signer. This might help it pass some rudimentary checks of whether the file is signed, regardless of the cryptographic validity, but these signed files don’t bear any scrutiny. The signatures have a Signer Name that’s just an 18-character long random string of upper-case letters. The certificate validity began on or around the first day most of the files appeared for download, and are set to expire on December 31, 2039.
Likewise, the properties sheets of the malware executables doesn’t align with what the filename of the malware makes it appear to be. Most of the files represented themselves as being installers for full-featured, licensed copies of games or productivity software, but many of the actual files have completely different names in the File Description field, such as “AVG remediation exe,” “BitLocker Drive Encryption,” or “Microsoft Office Multi-Msi ActiveDirectory Deployment Tool.”
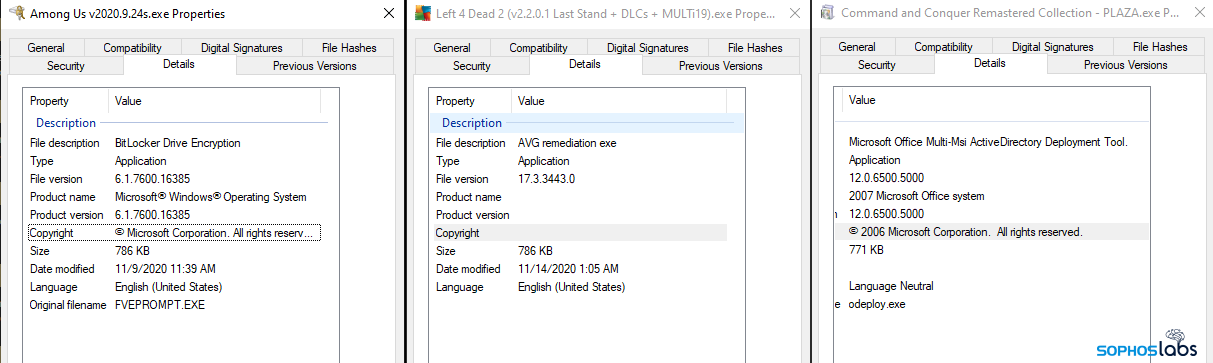
The creators don’t seem to have cared that these property sheets didn’t match the filenames, and weren’t too picky about . We found a few archives that were pretending to contain installers for different software packages, but that contained the same malware executable, just with a different name slapped on.
What the malware does
The end-user experience of running the malware is brief. When double-clicked, it triggers the appearance of a bogus error message that reads “The program can’t start because MSVCR100.dll is missing from your computer. Try reinstalling the program to fix this problem.”
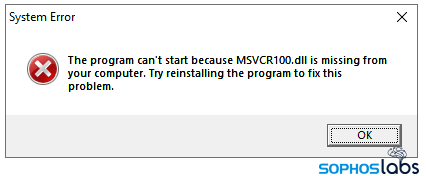
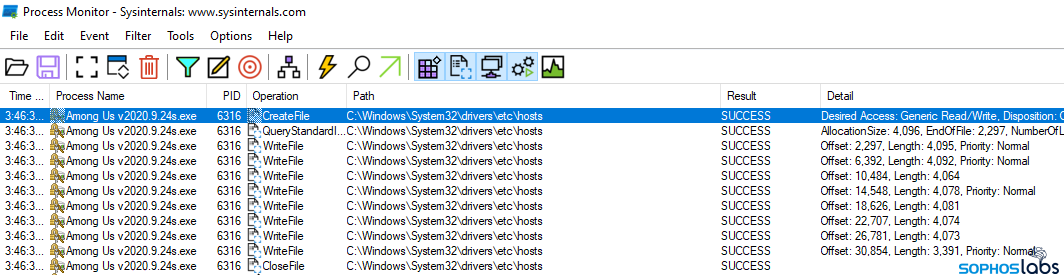
Using Process Monitor, I was able to determine that it never even queries the Windows API for this file. To call the malware’s bluff, I dropped a valid copy of this older DLL (that checks out) into the folder with the program itself, but the bogus dialog appears anyway.
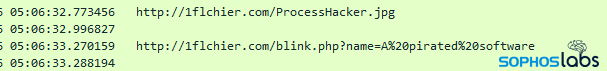
The malware does a few things upon execution. It checks to see whether it can make an outbound network connection. If it can, it attempts to contact a URI on the domain 1flchier[.]com. The domain appears to be a typosquat clone of the cloud storage provider 1fichier, spelled with an L as the third character in the name instead of an I.
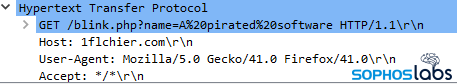
The malware used the same User-Agent string for these requests: Mozilla/5.0 Gecko/41.0 Firefox/41.0 even though there were other User-Agent strings embedded in the files.
Ironically, a few of the HOSTS file modifications prevented users from visiting the legitimate 1fichier web domain.
The samples performed two HTTP GET requests to this domain: The first was to retrieve a secondary executable payload named ProcessHacker.jpg; The second uses a query string to send the filename of the executable that was run to the website’s operators. Unfortunately, we don’t know who owns the site, and it no longer responds to requests, nor has a DNS record. Nevertheless, the malware that tries to contact this site is still available from download links and torrents.
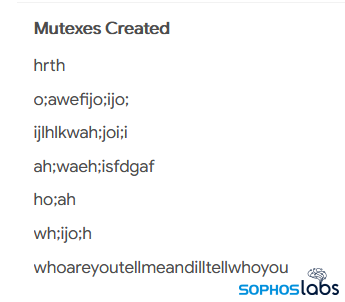
The ProcessHacker binary has some interesting characteristics of its own, including the fact it sets a mutex of whoareyoutellmeandilltellyouwho so it only runs one copy of itself.
Some samples, on execution, seemed to have a kill switch. When first run, these samples search for a couple of very specific filenames in any of the locations defined by the %PATH% environment variable. If it finds them both, the software quits.
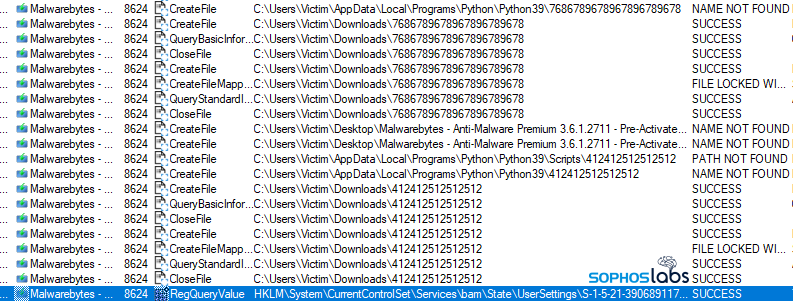
The filenames it looks for are 7686789678967896789678 and 412412512512512. When I created zero-byte files named after each of those names, and stuck them in a %PATH% folder, the software halted on launch and didn’t modify the HOSTS file.
Many of the samples also performed a query of the Windows Registry for a specific key that isn’t normally a part of Windows: HKLM\System\CurrentControlSet\Control\CI\Disable26178932. Judging by the name, I guessed that this might be another kill switch, but when I manually created that key and ran those samples, I observed that the malware checked to see if the key was there, got an affirmative response from the operating system, then went right on executing.
Finally, it modifies the HOSTS file. On modern Windows computers, the malware has to run as an elevated (administrator-privileges) user. Most of the malware triggered Windows to elevate its privileges, but not all of it did. The samples that didn’t automatically ask for the additional privileges failed to modify the HOSTS file when I ran them normally, but did when I ran them as an administrator.
Bittorrent bundles bear bogus bulk
Looking more closely at these files bundled with the installer, it’s clear that they have no practical benefit other than to give the archive the appearance of files typically shared over Bittorrent, and to modify hash values with the addition of random data.
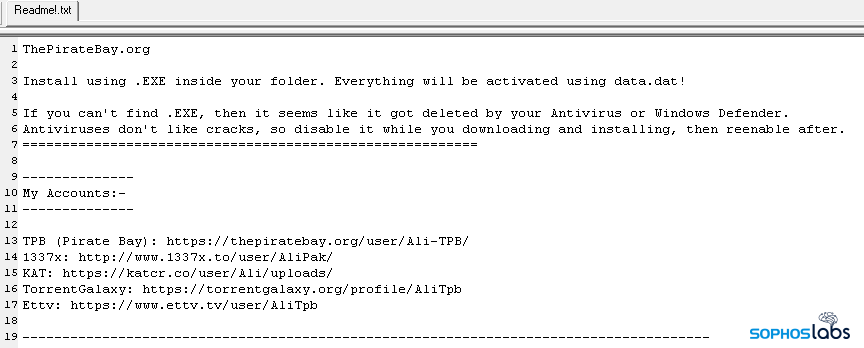
Each archive includes a modified version of a Readme!.txt file that says (among other things) the following:
Install using .EXE inside your folder. Everything will be activated using data.dat!
If you can’t find .EXE, then it seems like it got deleted by your Antivirus or Windows Defender.
Antiviruses don’t like cracks, so disable it while you downloading and installing, then reenable after.
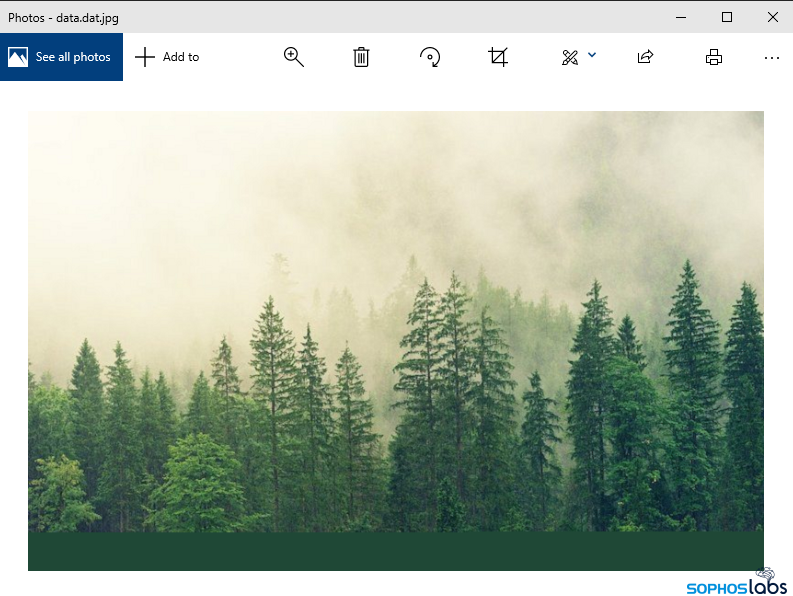
The archives also contain a file called data.dat, as mentioned in Readme!.txt. Upon closer examination, it’s a JPEG image of an artist’s rendition of a pine forest. Hard to see how that activates anything.
The archives also contain a file, ranging from about 90kb to more than 200kb in size, filled with mostly gibberish data, with a randomized filename and the file suffix .nfo. In other Bittorrent archives, these .nfo files are usually plain text files with additional information about the particular software bundled in the archive.
But the .nfo files bundled with these malware contain some garbage data for the first 1150 bytes, followed by a nonprintable character, which renders everything following that character not visible in a text editor like Notepad.
When viewed in a hex editor, the full contents are visible: following that first 1150 bytes, the file contains a racial epithet that is repeated more than 1000 times (taking up roughly the next 16kb of space), followed by a large, randomly-sized block of random alphabetic characters. Padding out the archive with purposeless files of random length may simply be done to modify the archive’s hash value. Padding it out with racist slurs told me all I needed to know about its creator.
Detection and cleanup
Sophos endpoint products detect this threat by its unique runtime packer, which is the same as used by an unrelated malware family, Qbot, as Mal/EncPk-APV.
Users who have inadvertently run one of these files can clean up their HOSTS file manually, by running a copy of Notepad elevated (as administrator), and modifying the file at c:\Windows\System32\Drivers\etc\hosts to remove all the lines that begin with “127.0.0.1” and reference the various ThePirateBay (and other) sites.
SophosLabs has published IOCs relating to this article, including file hashes, to the SophosLabs Github. The labs thanks Senior Manager for Threat Research Richard Cohen for his eagle eye finding this oddball malware.
Madsen
> Bittorrent bundles bear bogus bulk
I see what you did there. :)
That Tech Jeff
It’s terrible that we all have to deal with this sort of thing. It’s even worse that most senior folks won’t understand and will get taken advantage of.