Cloud environments can be busy places. With multiple users able to access, create, and configure cloud resources, it can be easy to miss the weak signals of attack behavior and reconnaissance activity.
To achieve necessary visibility across dispersed environments in Amazon Web Services and improve security posture, Sophos provides solutions which integrate with a variety of AWS services, including AWS Security Hub, AWS CloudTrail, AWS IAM Access Analyzer, and Amazon Inspector.
In this article we’ll take a closer look at how Sophos Cloud Optix, the Sophos Cloud Security Posture Management service, integrates and enhances Amazon GuardDuty.
How Amazon GuardDuty helps
Simply put, Amazon GuardDuty is your eyes and ears, detecting unusual and malicious behavior or threats in your AWS cloud environment that could compromise AWS accounts, data, resources or workloads. It’s looking for three primary types of threats to your organization:
-
- Attacker reconnaissance: Failed login attempts, unusual API calls, and port scanning
- Compromised resources: Resources used for cryptojacking, unusual spikes in network traffic, and temporary access to Amazon EC2 instances by an external IP address
- Compromised accounts: API calls from unusual locations, attempts to disable AWS CloudTrail, and unusual infrastructure deployments
The easy button for Amazon GuardDuty
Your AWS environment can generate a lot of alerts, so optimizing AWS security posture, knowing which Amazon GuardDuty alerts to prioritize, and identifying and blocking malicious behaviors before they become breaches is a challenge without specialist AWS platform skills.
Sophos Cloud Optix provides the easy button for AWS services, unlocking greater value from Amazon GuardDuty. Beginning with aggregation of Amazon GuardDuty alerts from multiple regions and accounts into the Sophos Cloud Optix dashboard, you benefit from a single pane of glass across your environments.
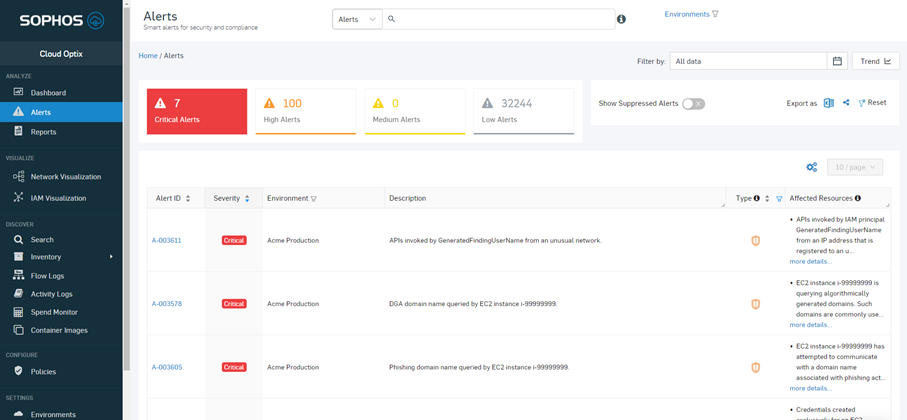
Risk prioritization of all alerts, including alerts from Sophos’ security posture assessments and threat detection, then helps busy security teams focus on and fix their most critical security issues.
Once turned on, other enabled integrations in Sophos Cloud Optix – such as Jira, Slack, Teams, and ServiceNow – automatically work for Amazon GuardDuty, allowing security teams to identify, assign, track, and ultimately respond faster to security threats.
Sophos managed security for AWS
As an AWS Security Competency Program and Advanced Technology Partner, Sophos has worked with AWS to develop a comprehensive cybersecurity approach to provide 24/7 protection and monitoring of essential AWS Resources.
A combination of automated Sophos protection and security experts, the Sophos Managed Threat Response team leverages Amazon GuardDuty to achieve the visibility needed to quickly identify critical cloud security events used in breach attempts across Amazon Web Services environments.
Get started with Sophos
Sophos Cloud Optix and Sophos Managed Threat Response are available via AWS Marketplace and will count towards any AWS-contracted consumption commitments already in place.
Sophos customers that would like to try out Sophos Cloud Optix for their cloud environments can start a trial from within the Sophos Central console. If you don’t have a Sophos Central account, you can register for free a trial on Sophos.com.
Organizations interested in Sophos Managed services for AWS can get in touch here for more information.
