Sophos researchers have recently released detailed research into Gootloader, a complex malware delivery platform used in a wide range of attacks, including ransomware.
Gootloader attackers hack into legitimate websites and subtly alter the content so the website can show different content to different visitors.
The criminal operators manipulate search engine optimization (SEO) so that when someone types a question into a search engine such as Google, the hacked websites appear among the top results.
What happens next depends upon their country location:
- Users from a country that is not a target are shown benign fake web content and nothing further happens.
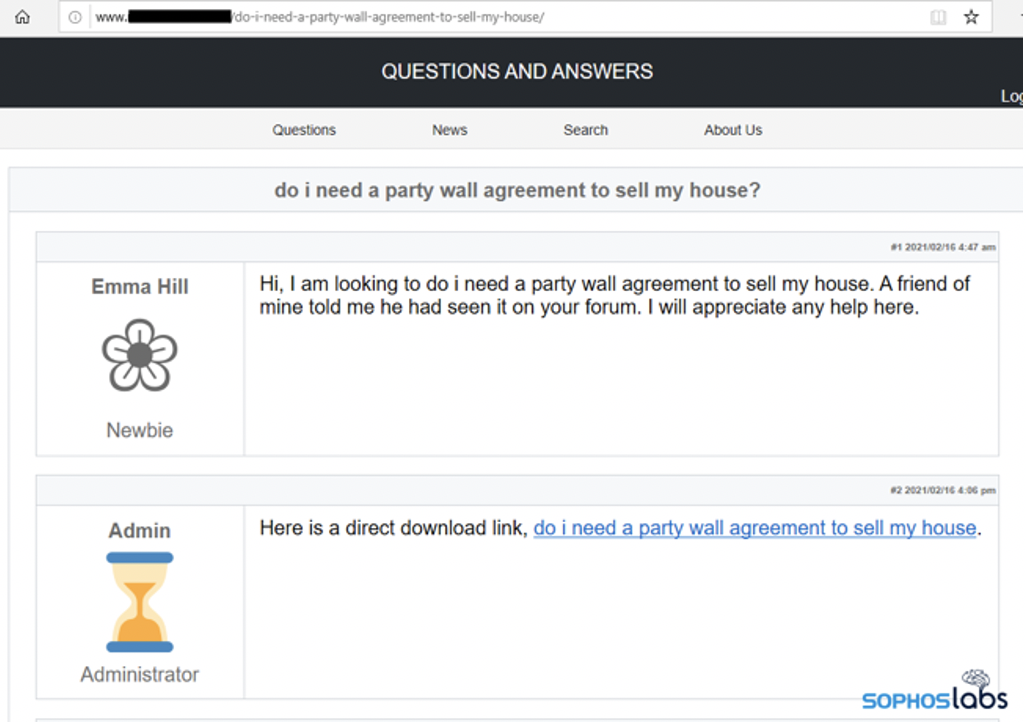
- Users from a target country are shown a page featuring a fake discussion forum on the very topic they queried, using the same terms they typed into the search engine. The fake discussion forum includes a post from a “site administrator,” with a link to a download. The download is a malicious file. If targets click on it, the next stage of infection begins.
Different countries, different attacks
Gootloader is currently delivering Kronos financial malware in Germany, and a post-exploitation tool called Cobalt Strike in the US and South Korea.
The attackers have also delivered REvil ransomware and the Gootkit trojan itself as payloads. Earlier operations targeted France.
Stopping Gootloader with Sophos Intercept X
Sophos Intercept X protects users by detecting the actions and behaviors of malware like Gootloader in multiple ways.
- The first stage javascript files is detected as: AMSI/GootLdr-A
- The PowerShell loader is detected as: AMSI/Reflect-H or Exec_12a
AMSI (Anti-Malware Scanning Engine) is included in all Sophos endpoint and server subscriptions managed through Sophos Central, and is available for Windows 10 and Server 2016+.
The PowerShell loader is detected as Exec_12a, this is a detection from our new behavioral engine which is included in all Sophos endpoint and server subscriptions managed through Sophos Central, with no minimum platform requirements.
Both the AMSI and Exec_12a policies are on by default and customers do not need to take any action to benefit from these protection features.
In both cases, admins will be notified of any detections via the local UI popup and the Events display in Sophos Central. In addition, both will likely generate threat cases for customers with Intercept X Advanced, and Intercept X Advanced with EDR subscriptions.
- Dynamic Shellcode protection identifies Gootloader in memory and automatically blocks it
Dynamic Shellcode protection is included in all Intercept X Advanced and Intercept X Advanced with EDR subscriptions for both endpoint and server. For more information on this feature, click here.
- IOCs for threat hunting and proactive blocking
Sophos EDR customers can access Indicators of Compromise on the SophosLabs Github, including SHAs, domains and IPs that customers can use as part of their Live Discover threat hunting, or proactive blocking.
Additional best practice advice to stop Gootloader
 In addition to benefiting from the protections in Intercept X, here are some additional steps you can take to avoid Gootloader:
In addition to benefiting from the protections in Intercept X, here are some additional steps you can take to avoid Gootloader:
- Be wary of Google search results that point to websites for businesses that have no logical connection to the advice they appear to offer and/or offer advice that precisely matches the search terms used in the initial question.
- Look out for a ‘message board’-style page that looks identical to the example in this article, and featuring text and a download link that also precisely matches the search terms used in the initial Google search. The fake Gootloader websites look the same regardless of whether they are in English, German or Korean.
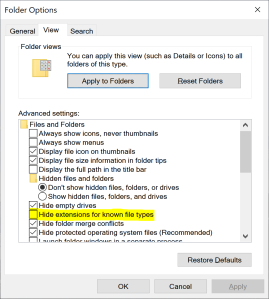
- Windows users can turn off the “Hide Extensions for Known File Types” view setting in the Windows file explorer as this will allow them to see that the .zip download delivered by the attackers contains a file with a .js extension
- Script blockers like NoScript for Firefox could help a web surfer remain safe by preventing the initial replacement of the hacked web page
Try Intercept X today
Visit our website for more information on Intercept X for endpoints and servers, and to start a no-obligation 30-day free trial.
For more information on Gootloader, read the detailed research report from SophosLabs.

Leave a Reply