Many pupils are starting their new school term from home rather than the classroom.
For families with younger kids, home schooling is often the first time that their children have needed to use computers (rather than gaming consoles) in earnest.
Whether you’re new to home schooling, going back to it after a break, or an old hand, it’s worth taking a moment to ensure you’re doing it securely.
Taking the time to establish good security practices now will lay the foundations for safe IT use in the years to come.
Shared devices
Many pupils will need to use a shared device to access their schoolwork, perhaps the family laptop or a tablet that their siblings use as well.
Give each child a user account of their own on the shared device.
This enables you to set up parental controls without affecting your own access. It also helps you children get into good security habits, such as having their own password (although depending on their age they may need to share it with you).
Read Setting up a Mac for young children for our step-by-step guide to getting started for Apple users:
Internet access
To support home schooling, many teachers provide links to online learning resources.
These may be videos hosted on third-party sites like YouTube and Vimeo, materials hosted by the school, or resources on external sites, either free or purchased by the school.
Teachers may also set tasks that require students to do their own web-based research.
All of these activities require children to have access to the internet. The challenge is to enable learning while also protecting your kids from inappropriate websites and keeping adult content out of their search results.
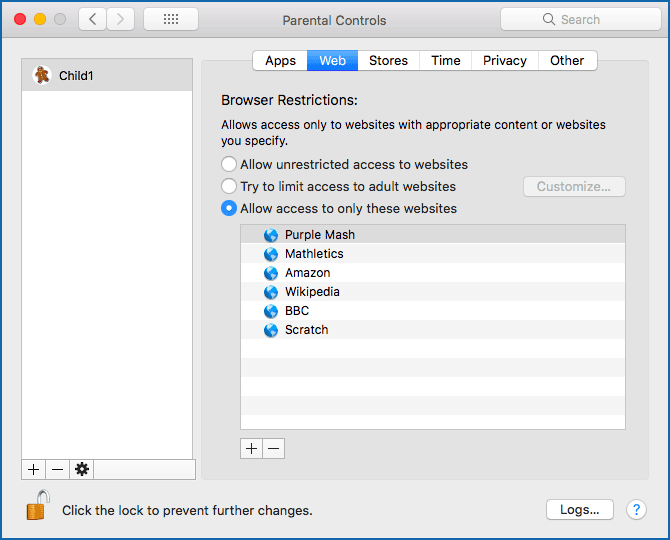
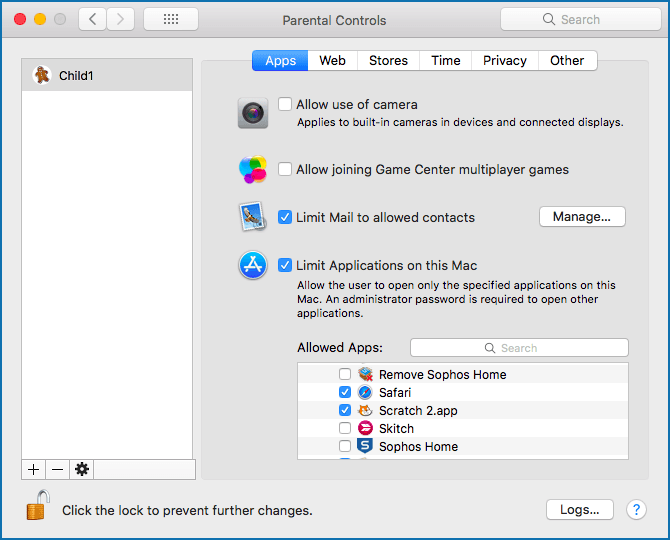
We recommend that you set up an account for your child and then enable the parental controls in your operating system to limit which sites your child can access.
If you’re a Windows 10 user, you can type family options in the search bar and enable parental controls from there. Strict web browsing on Microsoft Edge is then turned on automatically, and InPrivate (incognito) browsing is turned off. For more details, check out the Microsoft guide.
If you’re on a Mac, you do this in several ways depending on which version you’re running. Either search for instructions for your chosen version or follow the steps in our Setting up a Mac for young children article.
We also suggest that you:
- Use a home antivirus product that includes parental web filtering. This gives you control over the web content your children can access on the computer.
- Take advantage of search engine features to restrict access to adult websites. While these filters are not 100% effective, they do reduce the likelihood of inappropriate results appearing on screen.
To filter Google results, review Google’s Filter explicit results using SafeSearch instructions.
If you are a Bing user, see Microsoft’s advice on how to Block adult content with SafeSearch.
Educational apps
Home schooling often requires you to download new apps. These could be dedicated educational resource apps or apps that enable you to work online, such as to annotate digital documents or to attend online classes.
Whichever apps you use, stick to the official app stores. (On an iPhone, you have no choice but to use the Apple App Store; on Android you have the freedom to go “off market”, but we recommend that you stick with Google Play.)
It’s worth also reading other people’s opinions and experiences of new apps before downloading them to make sure that the apps do not include traps such as fleeceware, treacherous programming that sneakily fleeces you for money after a “free” trial period.
By the way, we suggest that you ignore the reviews and star ratings on the app stores themselves. You have no idea who gave those ratings or left the reviews, or even if they ever used the app at all.
Fake ratings and official-looking app store reviews can be bought online at a price that’s almost literally ten-a-penny. Look for reviews in independent user forums or for discussions in online cybersecurity groups.
Should you wish to enforce tight app controls, some parental control features allow you to limit your children to specific apps.
Passwords
Home schooling is often the first-time children need to manage passwords. They likely have a password for their school email and online learning resources, and if they have a separate account on a shared device, they will have a password for that too.
Some passwords, such as those for online resources that the school has allocated, will have been set by the school and you may be unable to change them. However, for all passwords that you’re able to update, it’s good practice to change the default to something that only you know.
Creating hard-to-crack passwords is something children can do for themselves, which gives them a sense of ownership.
This is a great opportunity to introduce them to passphrases: start with words that reflect their interests to make the phrases easier to remember, and then work together to make them more complex.
Depending on the age and ability of your child, you may want to start with simple pass phrases before moving to more complex, mutated ones when they’re ready. For example:
Child’s phrase Simple passphrase Complex/mutated passphrase ------------------ ----------------- -------------------------- Ice cream is yummy Icecreamisyummy IceC^eam?YuMMy! My teddy Eddy Myteddyeddy MyTeddy//E4d3d2y1
Even a simple passphrase is likely to be significantly more secure than the default password provided.
With default passwords set up by someone else, you can never be sure how many other accounts were set up with the same password, or how many other people have access to the list of defaults that were chosen.
No one wants to start their week with the hassle of re-setting forgotten passwords, and it’s worth acknowledging that children often forget their passwords or phrases.
You could introduce a password manager, but the low-tech approach of writing down the password or phrase and keeping it a safe place that’s separate from the device is often a more practical solution for families.
Historically, password advice has often included rules such as “never write down your passwords”, but if you write them down and lock them away (rather than putting them on a PostIt stuck on your monitor!), the risk of an intruder breaking into your house and stealing them is very slim.
If you have older children, they might benefit from watching our own How to pick a proper password video:
No video? Watch on YouTube. No audio? Click on the [CC] icon for subtitles.
Device security
A prerequisite for secure home studying is a secure device. Make sure your devices are fully patched and up-to-date and have good quality security software installed.
Sophos Home (free and paid versions are available) and Sophos Intercept X for Mobile (free) provide business-level cybersecurity for your personal Windows computers, Macs and Android phones, including web filtering.
You can manage the protection for multiple devices from a single Sophos Home account, making it easy to keep all your family’s computers and phones secure.
Privacy
Home schooling is a good reason to talk about digital privacy with your children. There are many steps you can take to maintain your online privacy, including:
- Checking the permission settings in your browser. Ensure that location, camera, microphone, and notifications are set to “Ask before access” (or similar wording).
- Using the privacy options in iOS and Android devices. Read iOS 14 and Android 11 privacy tips – top 5 things to check for practical advice from the Sophos team.
- Taking care when the camera is on. Be mindful of what’s in the background when your camera is active. Don’t give apps or websites access to your camera unless you know you need to, and don’t reveal anything you shouldn’t.
The most important tip when it comes to privacy is education.
Talk with your children about the importance of privacy when sharing personal content – what they share, how they share it, and with whom. There’s a huge difference between providing your teacher with a link to a video on a personal drive and uploading it to YouTube for public viewing.
Home Wi-Fi
It’s worth taking a few minutes to check that your home Wi-Fi network is secure, both to protect your personal information and, if a family member is working from home, your company network.
Once an attacker has a foothold on one device inside your network, it’s much easier for them to snoop on what’s going on in your family’s digital life, as well as to break into other devices, including your personal or work laptop, and from there perhaps even to get access to your work network.
Check out the recent home Wi-Fi security advice from the Sophos support team for more details:
Be proactive
Managing home schooling alongside everything else is a major effort for most families, and it can be difficult to find the time and energy to focus on good security as well.
If that sounds familiar (and we write from experience), set aside some time on the weekend when there is less pressure to hand in schoolwork. Many of the items we’ve covered only need to be set up once.
Education is, as always, the key to good security.
One unexpected advantage we’ve found of home schooling is that the increased number of shared mealtimes has provided the perfect opportunity to talk about security and privacy as a family.
LEARN MORE ABOUT HOME WI-FI SECURITY
No video? Watch on YouTube. No audio? Click on the [CC] icon for subtitles.

Richard
Hi Sally, this is a great article, full of useful and practical advise.
We use Sophos Home, but “This enables you to set up parental controls without affecting your own access” is not quite true, because you can only change website filtering for the whole machine, not individual users.
Paul Ducklin
Hi, Richard. Apologies for the delay in answering – I just did a review of “old comments” and this one came up, heigh ho, so here you are… I hope iy’s a case of “better late than never”.
You’re right that Sophos Home doesn’t let you vary its web filtering settings per user. I wish it did, but it doesn’t.
When we talk about “parental controls” in that section of the article, we’re talking about the controls provided by the operating system itself, usiong the operating system’s own security subsystem, such as limiting kids to specific named websites or specific pre-installed apps. Simply put, although Sophos Home doesn’t let you vary your background web filtering settings across multiple users, the operating system parental controls don’t let you vary your controls _unless_ you have multiple users. And that’s why we made the suggestion we did.
TBH, even on a laptop that is used exclusively by a child, I’d recommend using those high-level, very broad brush system-level controls for limiting what kids can do on the web, e.g. by creating a short and explicit top-level list of sites by name, rather than merely by the category of each page on the site as determined by a web filter.
Then use Sophos Home to protect everyone who shares the device (including background processes accessong the web for things like updates and data downloads, not not merely for accessing websites in a browser) so that the security blocker will kick in if any pages on any of those allowed sites should suddenly “go rogue” with malware, e.g. due to malvertising (poisoned ads on otherwise legitimate sites), or other dangerous and unwanted content.
To me, one of the most important reasons for setting up more than one account (and you can do this even on a laptop that only you ever use) is that if you want to try something new, such as a new app, you can log out and come back in as your temporary alter ego, install the new app for that user only, and test it out with a completely different set of files to the ones in your regular account. You won’t accidentally open an important existing file and save it back by mistake in an incompatible format, for example.
I have a couple of spare accounts on my Linux laptop for that purpose, with names like “tryit” and “guest”, which I use when I want to protect myself from myself. I’m not talking about cybersecurity research stuff like deliberately visiting hacked sites to get screenshots of malware – that I do in a VM on a different computer – but general experiments such as “seeing if I want to migrate to a different audio editor”, or “playing around with an video capture tool I haven’t tried before”, so that all the configutration and temporary files that get fiddled with or created aren’t in the midst of my “day job data” and therefore are less likely to affect it.
HtH.
David Pottage
I don’t agree with using mutated passwords, especially with children, as they are too hard to remember. They are also hard to type on the soft keyboards frequently found on phones & tablets. As spelt out in xkcd-936, password mutation does not actually help with security because the amount of entropy is not that high. Long multi word passphrases have more entropy, and are much easier to remember. They are also less prone to shoulder surfing when entered on a soft keyboard because you don’t have to switch between the alphabetic, numeric and symbol keymaps.
On the other hand, I definitely agree with writing down and safely storing a child’s password. A few months ago I had to deal with a child who was crying his eyes out because he had forgotten the password to his iPad, and each time he entered a wrong guess he got a longer lock out before it would let him try again. (My approach was to get the child to to write down all the possible passwords that it could be, so that no time was lost trying the same one more than once.) In the end I could not get in, so I had to factory reset the iPad, and thankfully apple’s iCloud backup restored virtually everything.
Paul Ducklin
For the record, Ihave always disagreed with Randall of XKCD in respect of that cartoon (the famous “correct horse battery staple” one). I think he has wildly over-exaggerated the entropy of the “random four-word password” system, where you pick four random dictionary words and memorise them. (The UK government has for many years been recommending three “random” words, perhaps assuming that most of us simply won’t reliably remember four words after all.)
The problem is that is *isn’t* inevitably easier to remember four truly randomly chosen words from a dictionary than it is to remember a little jingle or phrase that you convert into a sequence of letters and numbers, and most people *don’t* choose four random words from anywhere in the dictionary. They are more likely IMO to choose four words that [a] are in their everyday vocabulary and [b] already sort-of go together naturally. Thus you are very unlikely to get “correct horse battery staple”, and much more likely to end up with “red sky at night”. Rather than 100,000 words-to-the-power-4 password choices, as XKCD wants you to believe, you’re probably looking at 1000 words-to-the-power-4 or lower, which is one hundred million times less entropy!
Anyway, insisting that “multi-word phrases are easier to remember” is a bit like saying “it’s much easier to write with your right hand than to struggle with your left” – true for some people and not for others.
(I’m not sure about the shoulder-surfing argument, either. I find it easier to track characters as they’re typed in on someone’s phone if they spell out words. On occasions when I have had to reauthenticate phone apps while out on the road, e.g. in a bank, I am much more worried about CCTV cameras making a recording from which the keys typed could be recovered later in slo-mo.)
Lastly, you will notice that in the mutated passwords in the article, which older children might like to try, the examples aren’t simple substitutions of, say, “3” for “E” and “4” for “A”. We’ve also added ectra characters, as in typing “E4d3d2y1” as a mutation of “Eddy”.
Oh, and post-lastly, going for wacky/mutated phrases helps to bypass the annoying problem (which should not exist, but does) that so many websites stupidly demand that you mix up the characters in your password to satisfy those intransigent “at least one digit, one punctuation and a mix of upper/lowers” rules. It really does get my goat when a website tells me that 32 hex characters representing 128 bits directly from /dev/urandom is too insecure to be acceptable, while “Pa55word!” rates as top strength. But I digress.
Mahhn
Digression up staging (not a proud thing) I really don’t like that we have (as industry standards) password length limits that are so short. Sure you can put in pA55w0rd@123 but you can’t put in 1wenT2ThesToreTheoTherdayandforgoTwhaTiwenT4, or even Thisismylongpassword(2021)hackmeifyoucan
or my favorite, but I don’t spell it the same every time Supercalafragulisticexpaldocious+1
I think I would really use something like; imsickofworkingalone@home4FlashPortalaccess. and maybe change the last part depending. Seriously though, I don’t use those, but I do like passphrases, I agree they are easier to remember.
Paul Ducklin
I can see the reason for a password length limit, just to discourage users from setting passwords that necessitate a giant network packet up front.
But not 10 characters, or 16, or even 32. (In particular, passwords shorter than the hash you plan to use seem particularly peculiar.)
My feeling is that 128 characters would give everyone as much expressiblity as they might ever reasonably need. Bus short limits like 16 characters – does Android still have that restriction? – I just don’t get. It’s as though you are worried I might be taking security *too* seriously.
Sometimes I have 17 characters simply because it’s 14 characters of wildly random nonsense plus a little finishing flourish that I like typing (because I am playing out the phrase that the password stands for in my head, and smiling as I type).