This morning, Sophos is publishing its newest threat report. The report encapsulates the work of multiple teams within Sophos, including SophosLabs, Cloud Security, Data Science, and Rapid Response. The daily work of these and other groups in the company help protect Sophos’ customers from an ever-increasing variety and intensity of acts of malfeasance targeting their computer systems and data.
The past year presented the world with challenges that humans haven’t faced in more than a century. While the internet gave us the ability to cope with a global pandemic better than was possible in 1918, we faced new complications in 2020 from ransomware, cryptojackers, and digital theft targeting every conceivable platform – even security appliances.
In our threat report (which you can download here), we’ve attempted to bring a bit of order to the chaos of the past year. We’ve structured the report to discuss the four key domains in which we focused our protection efforts in 2020 and which will guide our planning into 2021:
- The increasingly dire threat of ransomware in all its new forms
- Conventional Windows malware, including tools criminals use to steal data and deliver malicious payloads
- Unconventional malware that targets platforms not traditionally thought of as part of an organization’s attack surface
- How the pandemic impacted attacker behavior as much as how we now work, play, shop, go to school, and socialize – and the challenges involved in protecting those functions.
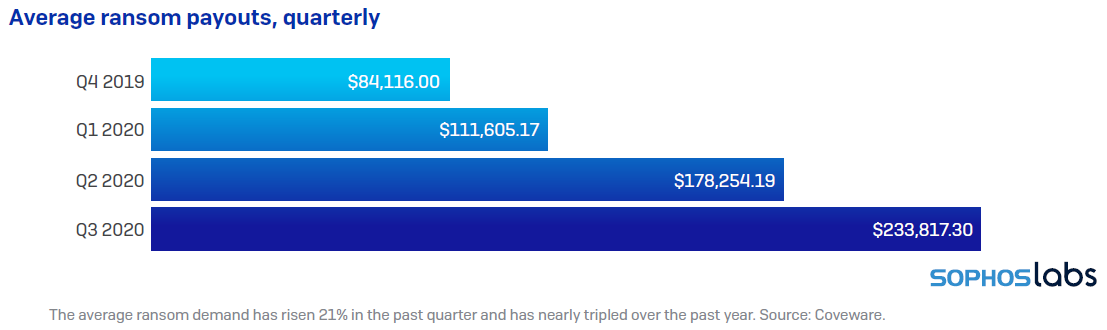
This was the year that ransomware, for instance, decided that merely encrypting our data and holding it hostage wasn’t quite evil enough. Threat actors discovered that even organizations with the best backups still are willing to pay big money to prevent sensitive data being leaked to the world, turning ransomware attacks into a hybrid hostage-extortion crisis.
It was also a year when threat actors pushed the ransomware envelope in another way: Initial ransom demands skyrocketed into the millions of dollars per incident, though some criminals made it clear they were willing to bargain with their victims.
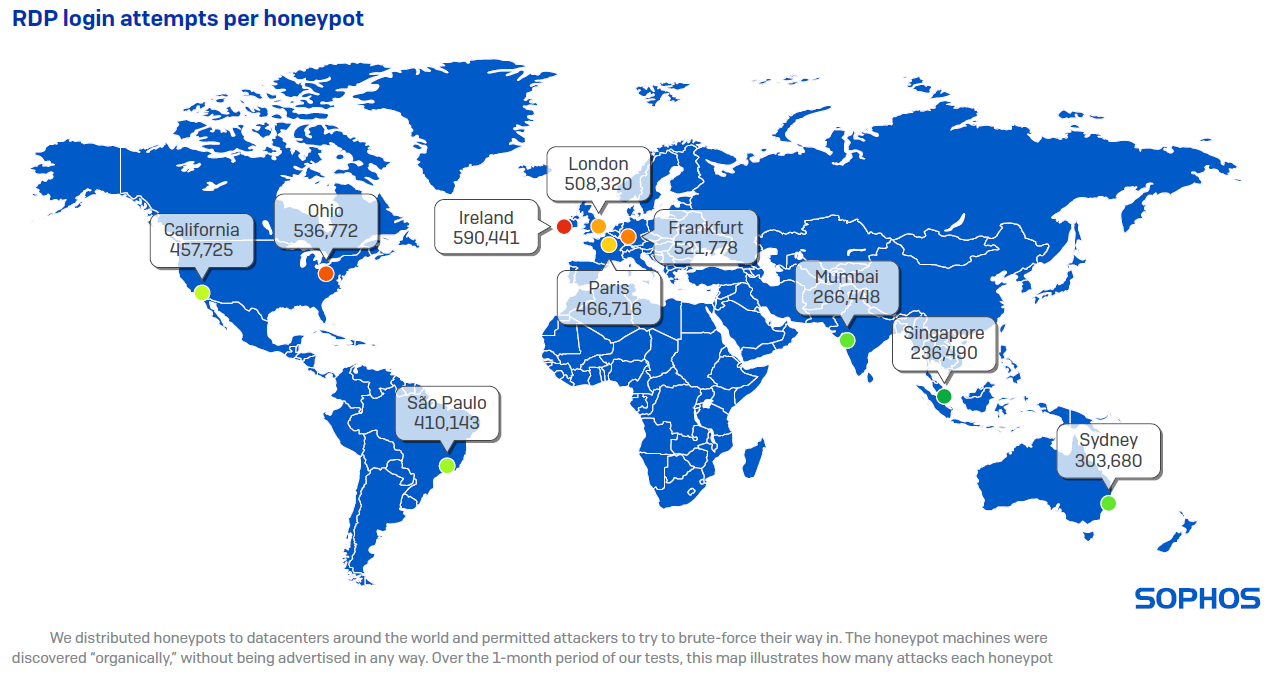
As office workers shifted into a work-from-home, lockdown mode, businesses had to devise new ways to provide their employees with secure access into internal computer systems, extending the enterprise perimeter to encapsulate thousands of homes. And as organizations rapidly deployed these remote-access features, attackers devised new ways to use them against us, targeting our VPNs and other internet-facing services and devices for special attention.
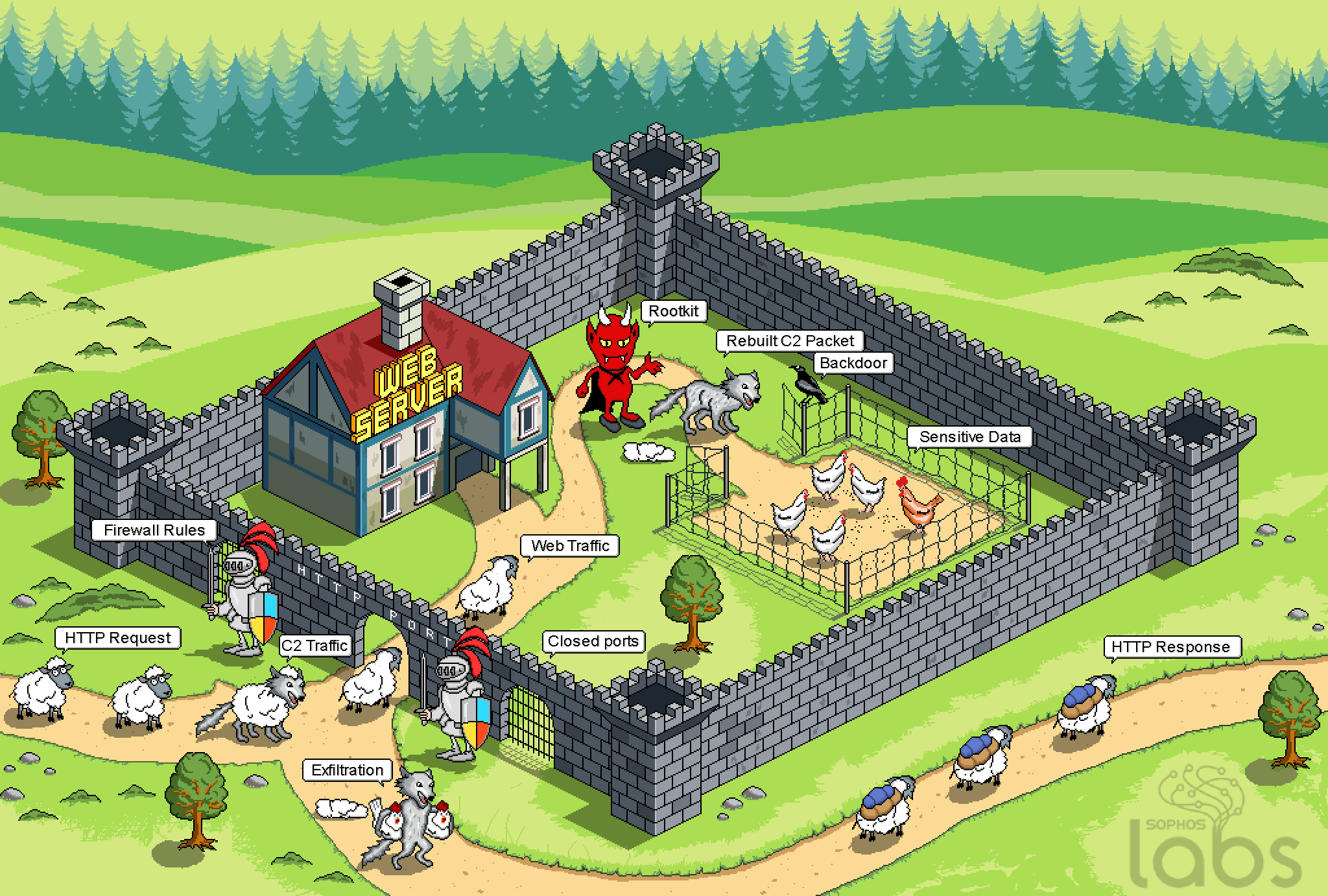
For instance, in incidents where we were called in to investigate, we discovered that Windows’s built-in RDP was not only targeted as an initial point of access, but once threat actors gained a foothold inside the perimeter, they began to take advantage of RDP to navigate laterally within an organization.
When the Sophos Rapid Response team investigates incidents, they attempt to determine the root cause of attacks. Beyond RDP, the Rapid Response team have also found that attackers increasingly make use of mundane, conventional, common malware to deliver ransomware and other more serious payloads. Any detection, no matter how banal, may be the precursor to a devastating attack.
Attackers also put effort into targeting attacks at technology not traditionally considered part of the attack surface: Networked IoT devices, firewalls, Linux servers, and Macs did not evade the attention of criminals who leveraged vulnerabilities to install cryptominers or other malicious code. And the attackers who did target Windows servers and workstations increasingly employ the tools created by the security industry to probe for or exploit weaknesses, using our analysis tools against us.
The pandemic factored into everything we did in information security this year, and it sharpened one point: In times of crisis, when systems all around us are under stress, protecting what still works is vitally important to maintaining our ability to survive and thrive. Under attack from all sides, the information security industry and many thousands of practitioners set aside competition and stepped up to work together, as a community, to push back against the darkness.

Leave a Reply