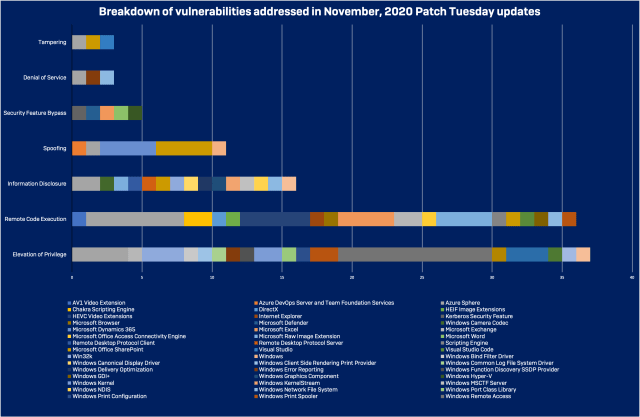
The eleventh Patch Tuesday of 2020 has arrived, with 112 new updates—of which 18 have been classified as critical by Microsoft, with another 92 marked as important. And one of the critical fixes is for a vulnerability that has already reportedly been used by an “in the wild” exploit.
CVE-2020-17087, a Windows kernel local elevation of privilege vulnerability, was first publicly reported by Google’s Project Zero in October after the discovery of active exploits. The vulnerability is in the Windows kernel’s cryptography driver (cng.sys).
A bug in one of the functions of the driver (CfgAdtpFormatProperty) causes it to be vulnerable to a buffer overflow attack that causes memory corruption in the kernel pool, or heap. It could be used for sandbox escape or other privilege escalation purposes by malicious code. Project Zero went public with the bug report and a proof of concept for exploitation on October 30, just seven days after it was discovered, because of evidence it was already being used in targeted attacks.
However, the kernel memory corruption bug is only ranked as “important” by Microsoft, despite its active exploitation. Some of the other bugs are a more clear and present danger to particular sets of Windows users.
Browser bugs
Two of the vulnerabilities of more widespread concern are tied to Microsoft’s Internet Explorer and Edge browsers. While Internet Explorer may be declining in use, some of its components are still used by Windows—and are still vulnerable to attack.
The critical vulnerabilities in question are both related to memory corruption—CVE-2020-17053 (in a component of Internet Explorer) and CVE-2020-17048 (in the Chakra Scripting Engine, part of the Edge browser). The Internet Explorer component bug is an arbitrary pointer de-reference vulnerability, while the Chakra Scripting engine bug is a “use after free” memory vulnerability in the JScript9 component. Both of these vulnerabilities are likely to be exploited, and could be used to remotely execute arbitrary code.
Azure Sphere
The single largest source of bugs this month was Azure Sphere, which had 15 vulnerabilities disclosed—two of them critical. These include six separate unsigned code execution vulnerabilities, which allow remote code execution (one, CVE-2020-16982, was rated as critical), and five elevation of privilege vulnerabilities (with CVE-2020-16988 rated as critical).
The remaining vulnerabilities in Azure Sphere are rated as “important”:
| CVE | Name |
|---|---|
| CVE-2020-16986 | Azure Sphere Denial of Service Vulnerability |
| CVE-2020-16981 | Azure Sphere Elevation of Privilege Vulnerability |
| CVE-2020-16989 | Azure Sphere Elevation of Privilege Vulnerability |
| CVE-2020-16992 | Azure Sphere Elevation of Privilege Vulnerability |
| CVE-2020-16993 | Azure Sphere Elevation of Privilege Vulnerability |
| CVE-2020-16985 | Azure Sphere Information Disclosure Vulnerability |
| CVE-2020-16990 | Azure Sphere Information Disclosure Vulnerability |
| CVE-2020-16983 | Azure Sphere Tampering Vulnerability |
| CVE-2020-16970 | Azure Sphere Unsigned Code Execution Vulnerability |
| CVE-2020-16984 | Azure Sphere Unsigned Code Execution Vulnerability |
| CVE-2020-16987 | Azure Sphere Unsigned Code Execution Vulnerability |
| CVE-2020-16991 | Azure Sphere Unsigned Code Execution Vulnerability |
| CVE-2020-16994 | Azure Sphere Unsigned Code Execution Vulnerability |
Another Azure-related vulnerability, CVE-2020-1325, is a spoofing vulnerability in Azure DevOps Server and Team Foundation Services. No details on this bug were provided.
Network File System
Not too many people use Network File System (NFS) outside of organizations that need compatibility across Windows, Linux and Unix for file sharing. The most concerning of these are CVE-2020-17051 and CVE-2020-17056, two major vulnerabilities affecting the NFS Service for Windows Server. When combined, they could lead to a very reliable route to exploitation against the latest versions of Windows Server, including 2016 and 2019.
CVE-2020-17051 is a heap overflow in the NFS driver (nfssvr.sys), affecting all versions of Windows Server. Although this critical vulnerability is triggerable remotely and likely to be exploitable, it requires write access to a directory in order to create a symlink. By forging a specific NFS message, the attacker fully controls the size of the buffer that will be used when copying data to a heap chunk with fixed size (for example, as with the code “memcpy($kernel_address, $controlled_content, $controlled_size)”). While this requires prior heap shaping (or “heap feng-shui“), it could allow an attacker to overwrite a following heap chunk. Overwriting function pointers would lead to code execution.
CVE-2020-17056 is a out-of-bound read in the same driver (nfssvr.sys). Even though such vulnerability can also cause a “blue screen of death” on the remote target, its most valuable use would be to leverage it into leaking kernel data by attacker, and therefore defeating kernel address space layout randomization (kASLR). It is therefore a perfect target to combine with CVE-2020-17051 to achieve stable code execution.
Since NFS is not installed by default, most Windows Server users will not be affected by these bugs. For those who are, the best short-term mitigation is to disable NFS—but patching is essential for those who need NFS for file services.
Other “criticals”
The remaining most serious bugs patched are all remote code excution vulnerabilities. Among them are bugs in Microsoft Windows’ Print Spooler, Scripting Engine, and a number of video and image file extensions:
| CVE | CVE Title |
|---|---|
| CVE-2020-17105 | AV1 Video Extension Remote Code Execution Vulnerability |
| CVE-2020-17101 | HEIF Image Extensions Remote Code Execution Vulnerability |
| CVE-2020-17106 | HEVC Video Extensions Remote Code Execution Vulnerability |
| CVE-2020-17107 | HEVC Video Extensions Remote Code Execution Vulnerability |
| CVE-2020-17108 | HEVC Video Extensions Remote Code Execution Vulnerability |
| CVE-2020-17109 | HEVC Video Extensions Remote Code Execution Vulnerability |
| CVE-2020-17110 | HEVC Video Extensions Remote Code Execution Vulnerability |
| CVE-2020-17058 | Microsoft Browser Memory Corruption Vulnerability |
| CVE-2020-17078 | Microsoft Raw Image Extension Remote Code Execution Vulnerability |
| CVE-2020-17079 | Microsoft Raw Image Extension Remote Code Execution Vulnerability |
| CVE-2020-17082 | Microsoft Raw Image Extension Remote Code Execution Vulnerability |
| CVE-2020-17052 | Scripting Engine Memory Corruption Vulnerability |
| CVE-2020-17042 | Windows Print Spooler Remote Code Execution Vulnerability |
More reasons to patch
Also of note is a vulnerability in Microsoft’s implementation of the Kerberos network authentication protocol (CVE-2020-17049). These bugs are reported as security feature bypass vulnerabilities. No details were provided.
Among the bugs Microsoft provided partners proof of concept exploits was CVE-2020-16998, a DirectX Elevation of Privilege Vulnerability, rated as important. The bug is another “use after free” memory corruption vulnerability, in the DirectX driver dxgmms2.sys. While this bug seems likely to be exploited, it is not considered a risk for remote code execution; its only viable use appears to be for escalation of privileges or sandbox evasion only.
There are also three separate elevation of privilege vulnerabilities in Windows’ 32-bit kernel subsystem (Win32k)— CVE-2020-17010, CVE-2020-17038, and CVE-2020-17057. All three patched bugs are use-after-free vulnerabilities that require only low privileges to be exploited—resulting in system-level access if successful.
Sharepoint has a total of seven vulnerabilities patched this month, including one remote code execution bug. CVE-2020-17061 is a deserialization vulnerability, and one that is likely to be exploited. But it requires user authentication, so attackers would have to have legitimate or stolen credentials to take full advantage of it.
Sophos protection
Here is a list of protection released by SophosLabs in response to this advisory to complement any existing protection and generic exploit mitigation:
| CVE | SAV | IPS |
| CVE-2020-17087 | Exp/202017087-A | |
| CVE-2020-17052 | Exp/202017052-A | SID:2304462 |
| CVE-2020-17053 | Exp/202017053-A | SID:2304463 |
| CVE-2020-17051 | SID:2304505 | |
| CVE-2020-17056 | SID:2304507 |
Sophos aims to add detections for critical issues, based on the type and nature of the vulnerabilities, as soon as possible and where we have been given sufficient information to be able to do so. In many cases, existing detections in endpoint products such as Intercept X will catch and block exploit attempts without the need for updates.

Leave a Reply