“KidsGuard?”
What an inappropriate name. It should be called KidsStalk-N-Dox, given that the makers of this consumer-grade stalkerware left a server open and unprotected, regurgitating the private data it slurped up from thousands of victims’ devices after a parent or other surveillance-happy person stealthily installed it.
The spyware app’s unprotected Alibaba cloud storage bucket was found by Till Kottmann. He’s a developer who reverse-engineers apps to see how they tick (or leak, in this case). Kottmann shared a copy of the Android version of KidsGuard with TechCrunch, which first reported on the data breach on Thursday.
Kottmann’s findings amount to “Goodness, Grandma, what enormous bites you take out of victims’ privacy with those big, keyloggy teeth of yours.”
https://twitter.com/deletescape/status/1229173045719425026
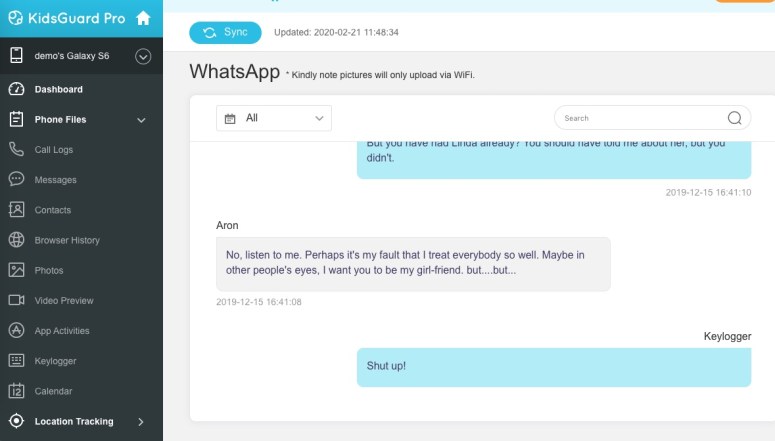
KidsGuard comes from a company called ClevGuard that promises that its “excellent products” will deliver “all the information” from a targeted device, including real-time location, text messages, browser history, photos, videos, recordings of phone calls, keylogger data for every keystroke entered and the app where it came from, and all the data from all the social apps – hopping over the end-to-end encryption of, for example, WhatsApp.
According to TechCrunch’s Zack Whittaker, the Alibaba storage bucket was apparently set to public: a common mistake with cloud storage buckets. Another mistake: it was left wide open, without a password.
After TechCrunch contacted ClevGuard, it shut down the exposed cloud storage bucket. The news outlet also contacted Alibaba, which similarly alerted the company about the leak.
Here we go again
KidsGuard is like other many other commercial-grade spyware in that the stalker needs to have physical access to a device in order to install it. It just takes a few minutes. Whittaker reports that after installation, there’s no rooting or jailbreaking required.
ClevGuard says the app can also be used for iPhones without access to the device (as long as the user doesn’t have 2FA on, in which case you would need to access the phone) if you give it the target’s iCloud credentials.
The Android version that TechCrunch and Kottmann checked out also requires that some security features be disabled, such as allowing non-Google approved apps to be installed and disabling Google Play Protect, Google’s built-in malware protection for Android.
After that, it runs in stealth mode, convincingly posing as an Android “system update” app. It’s tough for a victim to know that their device has been boobytrapped, given that there’s no app icon for them to spot.
That leaves KidsGuard to freely siphon photos, videos, recordings of phone calls, and to monitor activity on a slew of apps, including on dating apps such as Tinder. It also secretly takes screenshots of a victim’s conversations in apps such as Snapchat and Signal, which have supposedly ephemeral messages that disappear. As we’ve noted in the past with regards to Snapchat, those messages don’t disappear, KidsGuard being one of many ways for them to be captured.
Cooper Quintin, senior staff technologist at the Electronic Frontier Foundation (EFF), told TechCrunch that it’s “both alarming and sickening” that the exposed data includes not only that of adults, but also of children.
This is evidence that not only are spouseware and stalkerware companies morally bankrupt, they are also often failing to protect their stolen user data once they have it.
KidsGuard isn’t the first spyware maker that has fumbled victims’ data. It happened with MobiiSpy in March 2019. It happened twice with mSpy, which leaked millions of records in September 2018 and, before that, had its database leaked online in 2015.
For its part, Retina-X Studios, the company behind PhoneSheriff, TeenShield, SniperSpy and Mobile Spy, was repeatedly hacked, first in April 2017 and again in February 2018.
Retina-X finally threw in the towel on the surveillance business a month after that… and then had to settle charges brought by the Federal Trade Commission (FTC) for failing to keep its products from being used as illegal stalking apps.
What to do
Whittaker put together a “detect-and-destroy” guide for identifying and removing KidsGuard from your Android phone, but first, you need to to check whether the app has been installed: Go to Settings > Apps, and see if “System Update Service” is listed. This is the name that ClevGuard has given the stalkerware to hide it from the user.
If you think your Android device has been infected with KidsGuard stalkerware, check out the rest of his guide for instructions on removing it.
For iPhone users, Paul Ducklin has the following advice:
If someone has full remote access to your iCloud then you’re in big trouble. They can find out loads about you, and can change it all, too, including resetting your own password and locking you out of your account. So don’t delay, use 2FA today.
If you suspect someone else has access to your iCloud but hasn’t locked you out, go in yourself, change your password and review your settings.
Latest Naked Security podcast
LISTEN NOW
Click-and-drag on the soundwaves below to skip to any point in the podcast.

Anonymous
Wow, this is nuts!
epic_null
Hmm… I’m thinking that I wanna run an experiment to make sure physical access is actually needed – it would not ne the first time I’ve installed an app by remote, and I would not put it past most people to just accept permissions on something called “system update service” without thinking.