Some people are so rude.
They hold up traffic while they pull donuts in their fume-spewing, garish Lamborghinis; they inflict epilepsy-threatening laser shows on their wedding guests; they remove adorable lion cubs from their lion mothers to film the animals on their oriental carpets…
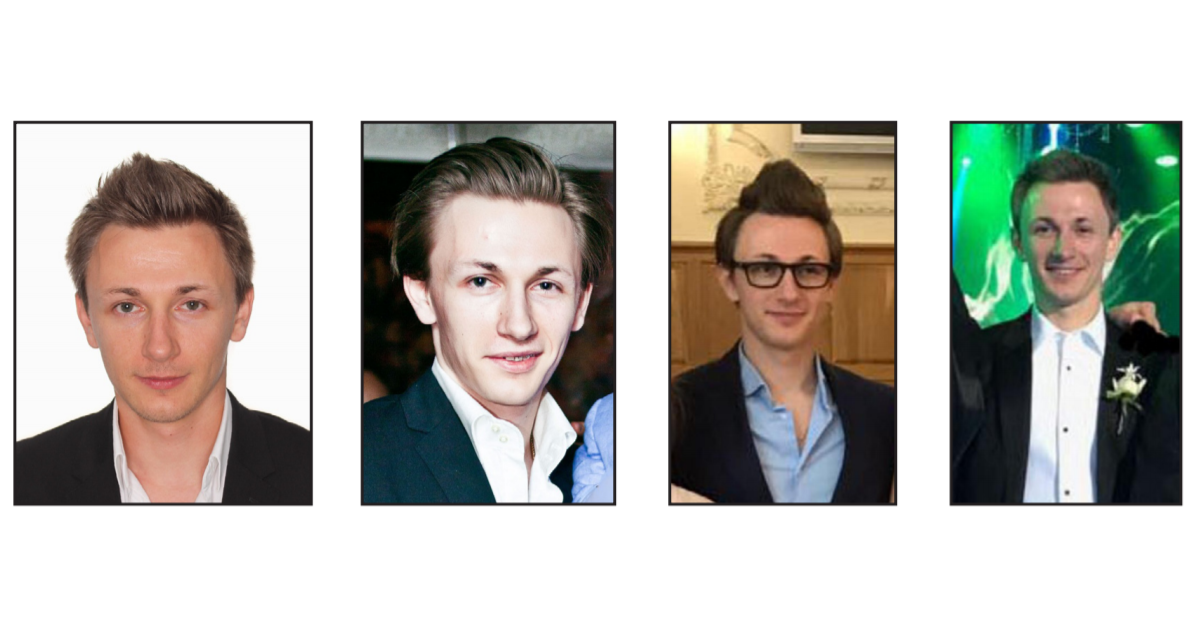
Members of Evil Corp are living a lavish lifestyle, funded by the life savings of their victims.
— National Crime Agency (NCA) (@NCA_UK) December 5, 2019
If Maksim Yakubets, who used the online identity of ‘Aqua’, ever leaves the safety of Russia he will be arrested and extradited to the US. pic.twitter.com/BdoaxZrFBK


…and they allegedly run Evil Corp (a.k.a TA505) – the threat group behind the ZeuS and Dridex banking Trojans that have siphoned tens of millions out of banks and bank customers’ accounts over nearly a decade.
If you can pry him out of his Lamborghinis – and Russia – you might be able to claim a $5 million bounty on the head of the man of whom I speak: Maksim “Aqua” Yakubets. Yakubets, 32, of Moscow, was indicted in the US on Thursday for allegedly being that head honcho of Evil Corp.
Yakubets is the star of many Richie Rich-kid brag videos like the one above, showing off things like his crashing of a hoverboard, his fondling of Lamborghini controls, and his disregard for traffic laws. The UK’s National Crime Agency (NCA) released a slew of photos and video montages showing the lavish lifestyle of Yakubets and his alleged cronies, of which there are quite a few.
One of his alleged cronies was also indicted in the US on Thursday: Igor Turashev, 38, from Yoshkar-Ola, Russia, for his alleged role in the “Bugat” malware conspiracy – another name for Dridex, which is also known as Cridex.
For its part, the NCA has been working on the group’s core malware strains – Dridex – since 2014. The NCA says that unraveling Dridex has involved “unprecedented” cooperation between itself, the FBI and the National Cyber Security Centre.
The NCA calls Evil Corp “the world’s most harmful cybercrime group,” responsible for deploying malware causing financial losses worth hundreds of millions of pounds in the UK alone. On Thursday, the US State Department, in partnership with the FBI, announced a reward of up to $5 million under the Transnational Organized Crime Rewards Program for information leading to the arrest and/or conviction of Yakubets.
It’s the largest ever bounty for a cybercriminal to date, the Justice Department (DOJ) said.
Indictment
A federal grand jury in Pittsburgh returned a 10-count indictment, unsealed on Thursday, against Yakubets and Turashev, charging them with conspiracy, computer hacking, wire fraud, and bank fraud, in connection with the distribution of Bugat/Dridex.
Peter Mackenzie, Sophos’s Global Malware Escalations Manager, calls Dridex “the most advanced banking Trojan in the world” – one that’s cost organizations and individuals millions of dollars over the years. It also has strong links to high-profile targeted BitPaymer ransomware attacks and is normally deployed via Emotet.
As we’ve explained in the past, Emotet is malware that’s designed to evade detection, dig in hard and multiply.
It’s a banking Trojan that injects code into the network stack of infected Windows computers, inserts itself into software modules that can then steal address book data and perform denial of service (DoS) attacks on other systems, and serves up a host of other Trojans.
In fact, as Peter has noted before, he believes Emotet’s raison d’être is to cluster-bomb endpoints with as many Trojans as possible. Some will explode right away, most can be removed safely, and a few will squirrel themselves away for years to come in places where people forget to check, then wait “for that unlucky victim to step on them.”
The sum of all that nastiness = an incredible amount of time and hard work spent fighting Dridex, Peter says.
Dridex has NOT dried up
Unfortunately, court indictments aren’t going to mop up Dridex anytime soon. On Thursday, the US Department of Homeland Security (DHS) warned that Dridex malware attacks targeting private-sector financial firms through phishing campaigns are still going strong.
According to the Cybersecurity and Infrastructure Security Agency (CISA), via the US National Cyber Awareness System, the phishing emails are using a combination of legitimate business names and domains, professional terminology, and urgent language that tries to get its targets to click on attachments. The sender email addresses are sometimes simulating individuals (name@domain.com), sometimes admin accounts (admin@domain.com, support@domain.com), or “do not reply” addresses (noreply@domain.com).
The subject lines and names of attachments can include typical terms such as “invoice”, “order”, “scan”, “receipt”, “debit note”, and “itinerary”, among others.
Sometimes, the message bodies are empty, and sometimes they’re chock full of text providing context for whatever pretext the attackers have adopted. Sometimes the messages say that the content has been scanned for viruses, and sometimes the text directs victims to a link or attachment.
CISA has a long list of mitigations that organizations can take to reduce risks, as well as tips on how security admins can configure their organizations’ defenses to detect Dridex and to avoid potential attacks. If your company is in retail or finance, you’re hopefully already on alert, given that Evil Corp/TA505 is known for focusing mainly on those sectors.
One last photo of Yakubets
We know that even if Yakubets gets caught, the organization he’s allegedly running likely won’t crumble: the NCA says that he’s allegedly employed dozens of people to run Evil Corp’s operation from the basements of Moscow cafes.
At any rate, one previous arrest proved to be barely a bump in the road for these guys: in 2015, the NCA and FBI took down the Dridex botnet and arrested Andrey Ghinkul, a Dridex distributor known as “Smilex.”
Within weeks, Evil Corp adapted the malware and infrastructure to resume its criminal activities.
But let’s hope that this last image will hopefully, at least in part, counterbalance all those Lamborghinis and laser-show wedding images by leading some bounty hunter to bring one more Evil Corp boss to justice:

DeanLJ (@DeanLJ)
Seriously thought that 4th mug shot was Zuckerburg, had to do a double take.
Lisa Vaas
The third one looks like Rachel Maddow, but probably just because of the glasses.
Mahhn
” FBI, announced a reward of up to $5 million under the Transnational Organized Crime Rewards Program for information leading to the arrest and/or conviction of Yakubets” So I’m guessing just dropping him off in a duffle bag to the FBI won’t earn a penny, you have to provide information to prove he did these crimes. That bites, could have been easy money. A few thousand in bribes would get him bagged, then it’s just smuggling him to the US that would be a bother. Can we trade Russia Zuckerburg? might work out good for everyone.
Mike Lynch
Call the Mandalorian! 🤠
Peter DC
But I have to mention : how can any operating system be so weak that opening an attachment will wreak havoc, no clear trail left behind, impossible to clean ? And how come those who built that are billionaires not paupers ? If Boaeing bullds a faulty plane that causes severe damage, the CEO gets fired and the company is barred from selling/flying their product. If Microsoft releases a weak product that causes tremendous damage… CEO gets lauded, becomes world’s richets man, tells us how we ought to live ?!