Elasticsearch services make storing, searching and analyzing large volumes of data simple, but that’s what makes them prime targets for cybercriminals.
Available as a service, AWS Elasticsearch allows users to easily deploy and operate Elasticsearch without the management overhead. (AWS provides help on how to configured AWS Elasticsearch correctly.)
However, did you know those domains have a “public” mode that leaves data exposed to unsigned requests made to these resources (ES clusters) by attackers?
Examples of unprotected Elasticsearch clusters that have been found public include the personally identifiable information (PII) of more than 20 million Ecuadorian citizens, and over 20 million tax records belonging to Russian citizens.
When left unprotected with publicly accessible domains, attackers can easily identify exposed AWS Elasticsearch clusters using popular search engines like Shodan. Then once they gain access, hackers can copy the data remotely or index it using other internet services.
Avoid publicly accessible AWS Elasticsearch domains
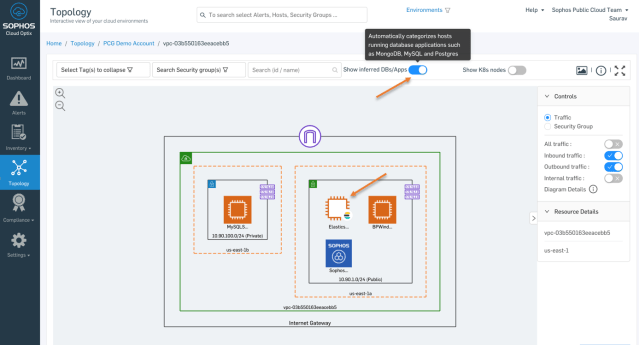
Sophos Cloud Optix helps organizations identify and prevent publicly accessible AWS Elasticsearch domains within minutes.

Using a combination of contextual topology view and AI capabilities, Cloud Optix infers the ELK stack (“ELK” is the acronym for three open source projects: Elasticsearch, Logstash and Kibana), identifying where Amazon EC2 instances are running Elasticsearch, Logstash and Kibana applications. This allows Cloud Optix users to quickly identify, during their routine security hygiene reviews, where an Amazon EC2 instance hosting Elasticsearch is receiving traffic from the Internet.
Say yes to open source, but keep data safe with this simple check from Cloud Optix.
Join us at AWS re:Invent
If you want to find out more come to our session on building security solutions using the AWS Elasticsearch Service, at AWS re:Invent.
Cloud Engineer Key Vaidya and Senior Director of MDR Platforms Dennis Griffin will share best practices on designing for scale based on their experiences developing a security monitoring and alerting system leveraging Amazon ES and other components.
What: Building Security Solutions using the Amazon Elasticsearch Service
When: Wednesday, December 4 @ 5:30 pm – 6:30 pm
Where: Mirage, Events Center B2 Red