The corporate network perimeter defensive line no longer exists. With increased attack sophistication and insider threats, organizations can’t guarantee that everything on the inside of their network can be trusted.
This is the principle of Zero Trust architecture. These days, organizations need to build controls immediately around the individual data assets, wherever they reside.
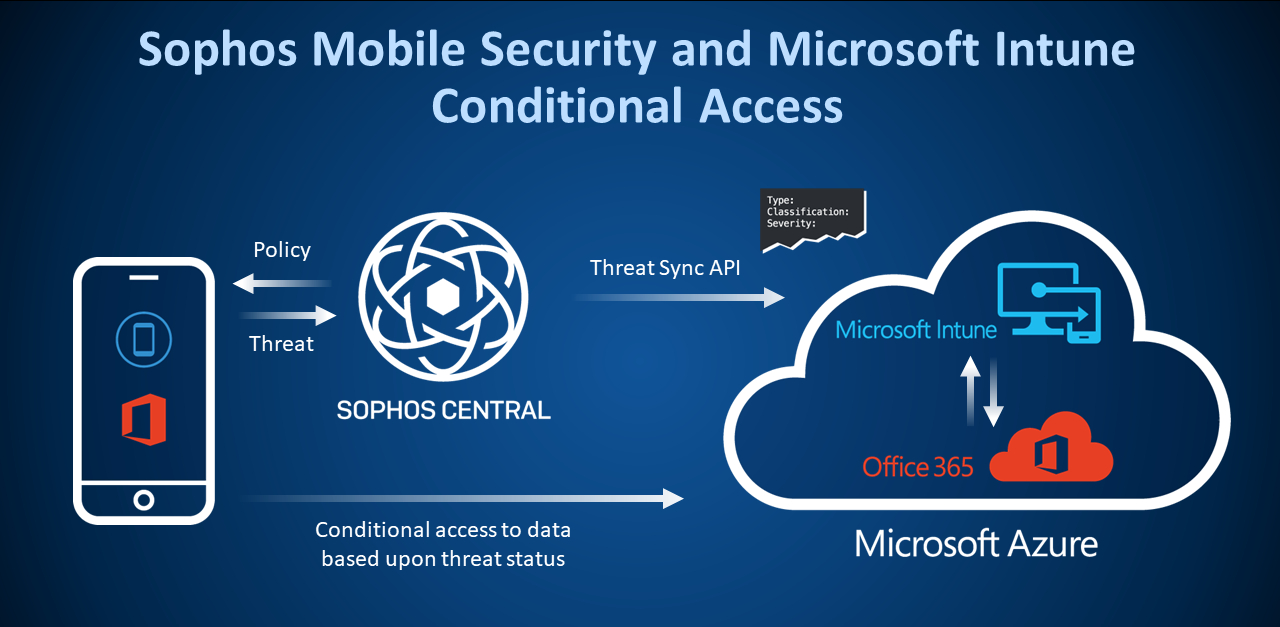
Administrators managing Microsoft Office 365 and Intune have access to the conditional access feature for exactly this purpose. Conditional access provides a set of policies that can be configured to control the circumstances in which users can access resources.
But every policy needs context. Without it, it’s easy to jump to the wrong conclusion. The more context we can provide, the better something can be understood, and the more informed a choice can be made.
Administrators want that extra context. After all, who wouldn’t want to block access to email or sensitive documents from a mobile device found running a malicious application or connected to a Wi-Fi network with a potential man-in-the-middle attack underway?
Sophos Mobile Security is our leading mobile threat defense app. It runs on both Android and iOS devices and can share threat details with Microsoft to provide that extra bit of context. Conditional access policies can now take threat detection results from Sophos into consideration when deciding whether to allow access to request resources.
To learn more about Office 365 and conditional access, visit Microsoft’s conditional access page.
To learn more about Sophos Mobile Security, visit the Sophos website.

Leave a Reply