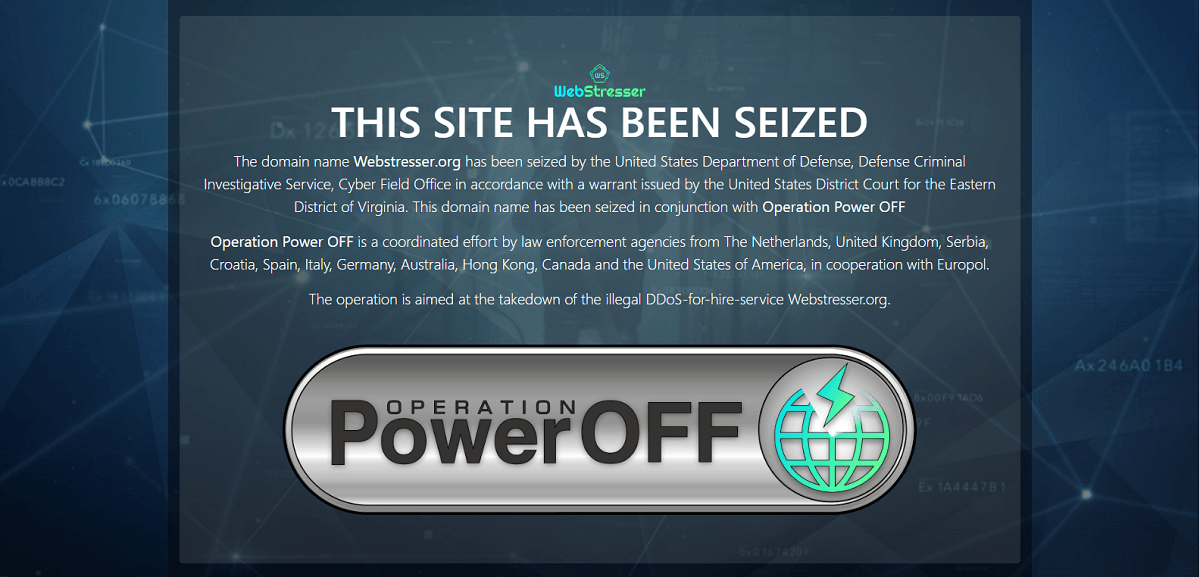
In April 2018, Dutch police inflicted a whole lot of “access denied” when they shut down Webstresser, the world’s biggest market for distributed-denial-of-service (DDoS) attacks.
Law enforcement working in multiple countries nabbed at least four of the attack-for-hire site’s admins, and then they went knocking on the doors of its users. Some got arrested, while some got away with warnings.
Well, going on a year later, it’s still mop-up time.
The UK’s National Crime Agency (NCA) announced that it’s been working with law enforcement agencies from 14 countries as part of what it’s calling Operation Power Off: an ongoing project to get at all the people and services behind DDoS attacks.
Police in the UK and Scotland have issued 8 warrants and seized more than 60 personal computers, tablets and mobile phones, the NCA said. An unspecified number of users have also received cease and desist notices. Police are eyeing another 400 Webstresser users for possible prosecution.
Webstresser: So easy to use, so devastating
At the time of the service’s shutdown in April, Europol said that its top users were in the Netherlands, Italy, Spain, Croatia, the UK, Australia, Canada and Hong Kong. With over 136,000 registered users, Webstresser was credited with being behind an estimated 6 million cyber attacks worldwide.
The Webstresser-enabled attacks targeted critical online services for banks, government institutions, police forces, and people in the gaming industry.
DDoS attacks are blunt instruments that work by overwhelming targeted sites with so much traffic that nobody can reach them. They can be used to render competitor or enemy websites temporarily inoperable out of malice, lulz or profit: some attackers extort site owners into paying for attacks to stop.
Much mayhem could be had for what was basically pocket change. According to Webstresser’s pricing table, archived on 19 April before the site was taken down, memberships started at the “bronze” level, for €15 or USD $18.99/month, went up to $49.99/month for the “platinum” service, and topped out at $102/month for “lifetime bronze.”
A service like Webstresser can be used by those with nary a smidgen of technical skill. All they had to do to paralyze target sites was to hand over a modest amount of money: PayPal payments were accepted, but the site’s admins preferred Bitcoin payments enough to offer a sweet 15% discount.
Well, so much for hiding behind cryptocurrency and supposedly anonymous usernames. Jim Stokley, Deputy Director of the NCA’s National Cyber Crime Unit, said that none of that will shield DDoS-ers from getting busted by a police force that crosses borders to track them down:
The action taken shows that although users think that they can hide behind usernames and crypto currency, these do not provide anonymity. We have already identified further suspects linked to the site, and we will continue to take action.
Our message is clear. This activity should serve as a warning to those considering launching DDoS attacks. The NCA and our law enforcement partners will identify you, find you and hold you liable for the damage you cause.
Ian
I love it. Everyone involved with DDoS attacks should be prosecuted. Not just the admins running the site.
Lorraine Nkoane in south africa
Agree with Ian