We’re sure you know what ransomware is by now.
ICYMI, ransomware is malicious software that scrambles your files with a randomly generated cryptographic key…
…and then sends the one and only copy of that decryption key to the crooks.
Who promptly offer to sell it back to you so that you can unlock your data and get your business moving again.
And we’re sure you’ve heard of a strain of ransomware known as SamSam – named, apparently, after a French cartoon – that we’ve written about depressingly often on Naked Security.
The crooks behind SamSam have been using a tricky technique that is quite different to that used by early strains of ransomware from a few years ago, such as CryptoLocker, CryptoWall and TeslaCrypt.
Instead of using mass spamming techniques to blast their malware to millions of recipients in the hope of collecting thousands of dollars each from thousands of victims scattered all over the world, the SamSammers used a more pin-point approach.
They identified lists of networks where they knew there was a security hole, such as a remote access portal with a guessable password, and picked just one network at a time to attack.
By scrambling hundreds of computers in a single network at the same time – often, ironically, by employing the same sort of sysadmin techniques that a legitimate IT staffer might use to distribute a genuine software update – the crooks generally ended up in a very strong position from which to extort money.
“All-you-can-eat buffet” pricing
Indeed, their extortion demands reflected the power they wielded – they generally “offered” a “price” of about $8000 per computer…
…or $50,000 for what you might call the “all-you-can-eat buffet” option, offering what was effectively a network-wide licence to decrypt all your computers for one lump sum.
You can probably imagine getting by for a few days with 5% or even 10% of your network out of action, but not if 50% of more of all your laptops and servers are frozen and unusable.
And that’s what the SamSammers were banking on: a situation where some organisations had little choice but to pay up.
The biter bit
Well, justice, of a sort, is in the process of being served.
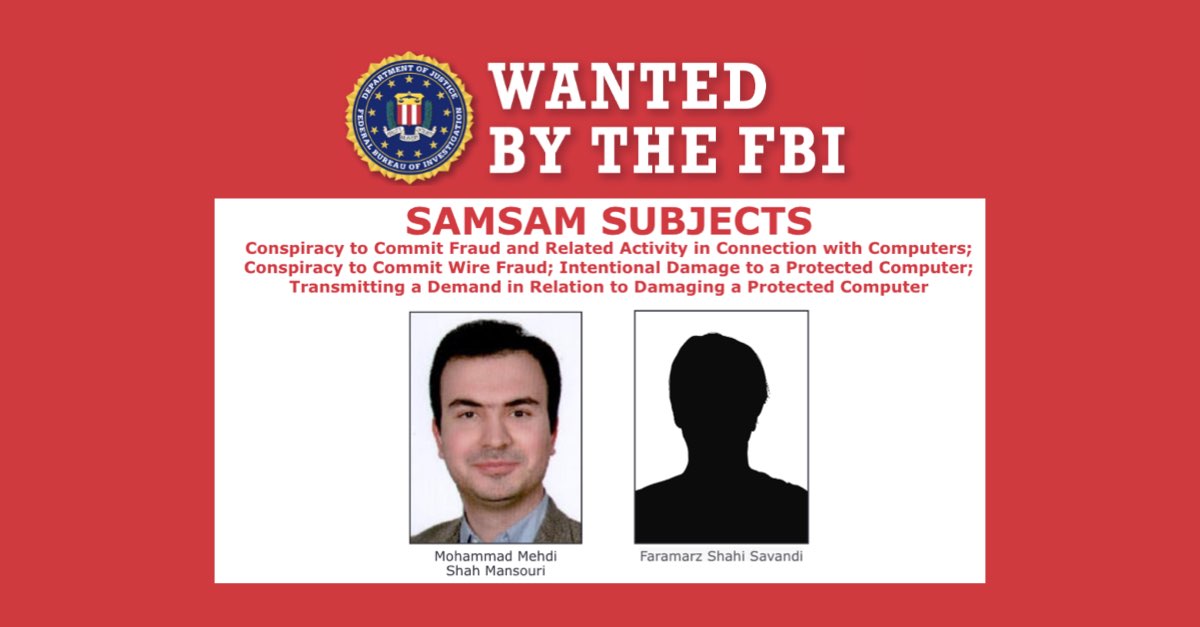
The FBI claims to have identified two of the perpetrators of this long-running cybercrime, publicly naming them as Mohammad Mehdi Shah Mansour (27) and Faramarz Shahi Savandi (34), both allegedly resident in Tehran, the capital of Iran.
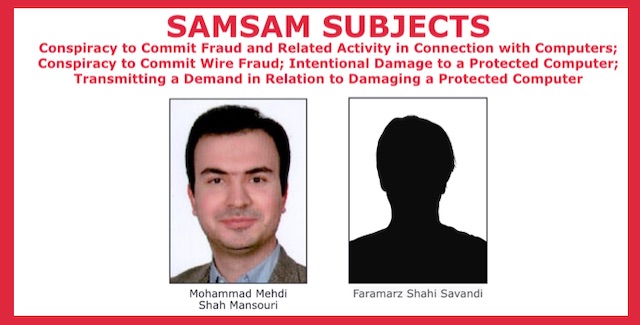
Indeed, the US Department of Justice has published an indictment, unsealed today in the US District Court of New Jersey, charging the pair with a raft of criminal offences, including:
- Conspiracy to commit fraud and related activity in connection with computers.
- Conspiracy to commit wire fraud.
- Intentional damage to a protected computer.
- Transmitting a demand in relation to damaging a protected computer.
Additionally, the US Department of the Treasury has publicly identified two other Iranians, Ali Khorashadizadeh and Mohammad Ghorbaniyan, whom the Treasury accuses of helping Mansour and Savandi to convert their extortion “earnings” – paid in Bitcoin by their victims – into Iranian currency.
What happens next?
If the defendants are, indeed, in Iran, it seems unlikely – at least in the current political climate – that they will ever be sent for trial in or by the United States.
That doesn’t mean they’re home free, of course – if they’ve made as much money as we suspect, they might fall foul of any number of rules and regulations in Iran, so for all we know they might face investigation on home soil.
Anyway, even if this revelation serves to scare the SamSammers into inactivity, there’s still plenty of cybercrime about, and plenty of other ransomware (and ransomware gangs) to take over where the SamSam crew left off.
So don’t let this announcement lull you into a false sense of security – the history of ransomware is full of stories about new strains that took over when existing ransomware groups were taken down.
Fortunately, the same advice that we gave to help to protect you from SamSam will help you against ransomware – and cybercrime – in general, so please revisit it now!
We also urge you to read the SophosLabs 2019 Threat Report, in which we analyse the state of play in cybercrime today, including a section on ransomware in general and SamSam in particular.

Bryan
We’re sure you know what ransomware is by now.
ICYMI, ransomware is…
Humorous irony of the day: As a regular Naked Security reader (and person with non-rock residency), I *do* know what ransomware is…
…but after a couple guesses involving “in case you might…[abort, retry, fail?]” I had to Google “ICYMI.”
:,)
PeterM
Same here :-)
mycelium11235
“Teheran”
Should be Tehran.
Mark Stockley
Fixed, thanks