Apple’s well-received iOS 12 is barely out of the gates and already someone has found a way to beat its lock screen security to access a device’s contacts, emails, telephone numbers, and photos.
As bypasses go, this one’s elaborate, requiring two Apple devices, 16 steps to be executed in the correct sequence to view contacts, numbers and emails, plus a further 21 steps to view photos (and Face ID to be either turned off or taped over).
That immediately rules out a casual or opportunist attack – anyone wanting to exploit the weakness would need physical access to the device, plenty of time, and step-by-step instructions.
The weakness
The flaw was revealed to the world in a Spanish-language video from a researcher, Jose Rodriguez, who has built a reputation for finding at least two other iOS lock screen bypasses.
One of Siri’s helpful features is the ability to do all sorts of things even when an iPhone or iPad are locked, including phone people, send a text message, and tell users about their meetings. From the description, it is this which makes the bypass possible, albeit via a convoluted route.
An annoying pattern
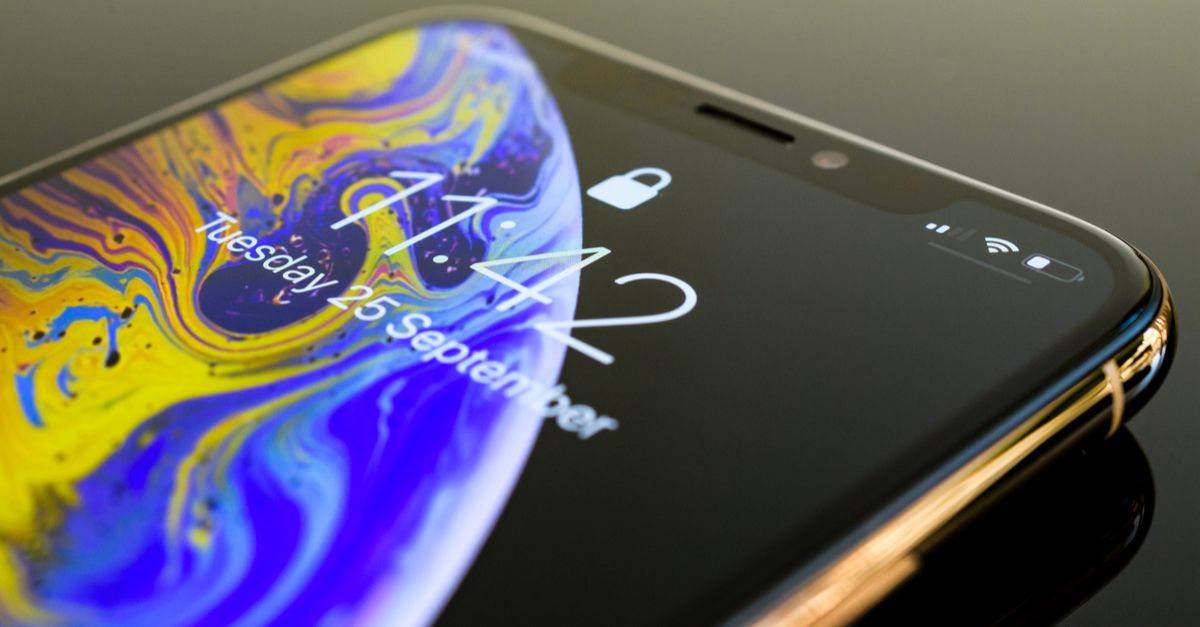
According to third parties, the latest bypass proof-of-concept sequence seems to work on all Apple devices running iOS 12 (and the iOS 12.1 beta), including the new XS.
It’s been a running theme going back to iOS 6 in 2013, when Rodriguez discovered his first lock screen bypass in a version of iOS which had supposedly patched a previous one.
Two years later, he was back with another one in iOS 9, followed by several discovered in later versions in 2016.
The pattern is easy to spot – Apple releases a new version of iOS and has to patch it for a lock screen flaw not long after. Things quieten down until the next annual release and the cycle starts again. While bypasses have become tougher for researchers to find over time, find them they have.
This reinforces why iOS 12’s default to allow automatic security updates is a good idea. In the meantime, the bypass can be mitigated by disabling Siri’s lock screen access: Settings > Face ID & Passcode or Settings > Touch ID & Passcode > disable Allow access when locked.
Mahhn
Glad I kicked Siri to the curb years ago. Not the first time it’s held backdoors open. If I could only uninstall it…..
Rich Pasco
I heard of an intruder who gained access to a house by shouting in through the window something like, “Hey Siri, unlock the font door!”
roleary
It was a neighbor who did it in front of the home owner. Naked Security covered it in 2016.
Still, Siri appears to be a security hole in general.