At the DefCon Voting Village in Las Vegas last year, participants proved it was child’s play to hack voting machines: As Wired reported, within two minutes, democracy-tech researcher Carsten Schürmann used a novel vulnerability to get remote access to a WinVote machine.
This year, it was literally child’s play: the DefCon village this past weekend invited 50 kids between the ages of 8 and 16 to compromise replicas of states’ websites in the so-called “DEFCON Voting Machine Hacking Village.”
11-year-old Emmett Brewer is too young to vote, but it turned out that he’s not too young to learn how to change election results on a replica of Florida’s state website… in under 10 minutes, mind you, as the Voting Village announced on Friday:
Here’s the DefCon Voting Machine Hacking Village roundup of discoveries for the day! Day 1 / Part 1 pic.twitter.com/ovQs7uX7jK
— DEF CON VotingVillage (@VotingVillageDC) August 11, 2018
The kids were given rudimentary instruction in performing SQL injection attacks: one of the web attacks that refuses to die.
The organizers are still analyzing the results of the project, but they said that they invited the kids to tamper with vote tallies, candidate names, and party names.
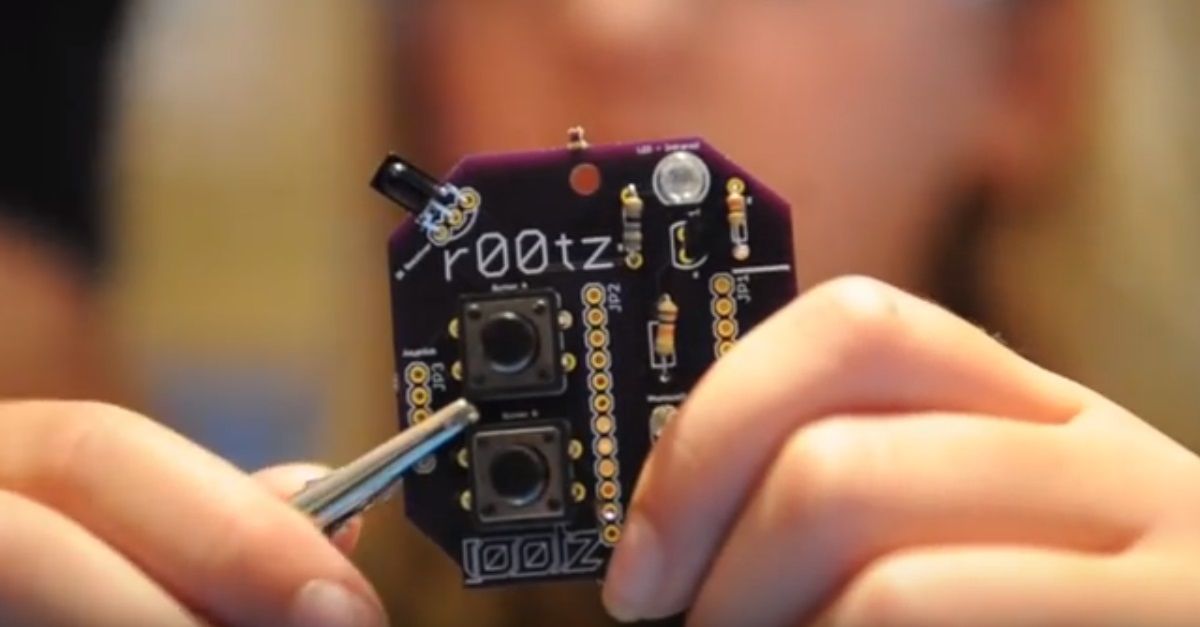
Mission accomplished: Nico Sell, the co-founder of the non-profit r00tz Asylum – an organization that teaches kids reverse engineering, soldering, cryptography, and responsible bug disclosure and which helped to organize the event – told PBS News Hour that more than 30 children managed to change state site replicas in under 30 minutes.
And here’s a vote for both gender equality and for there being serious problems with voting technologies: an 11-year-old girl tripled the number of votes on the Florida replica site within about 15 minutes. That’s pretty pathetic, Sell said:
These are very accurate replicas of all of the sites. These things should not be easy enough for an 8-year-old kid to hack within 30 minutes. It’s negligent for us as a society.
All but four of the kids managed to exploit the bugs – which included SQL injection flaws and similar common coding blunders. They changed vote tallies to number 12 billion, rewrote party names, and rechristened candidates. The new names included “Bob Da Builder” and, as a noted thumb’s-up for Matt Groening’s Futurama, “Richard Nixon’s Head.”
The National Association of Secretaries of State (NASS) responded to the news by telling DefCon to bring it on: it’s “ready to work with civic-minded members of the DEFCON community wanting to become part of a proactive team effort to secure our elections,” the association said in a statement.
But NASS isn’t convinced that the success the VotingVillage had in pummeling replica sites reflects reality. From its statement:
Our main concern with the approach taken by DEFCON is that it utilizes a pseudo environment which in no way replicates state election systems, networks or physical security. Providing conference attendees with unlimited physical access to voting machines, most of which are no longer in use, does not replicate accurate physical and cyber protections established by state and local governments before and on Election Day.
It would be extremely difficult to replicate these systems since many states utilize unique networks and custom-built databases with new and updated security protocols. While it is undeniable websites are vulnerable to hackers, election night reporting websites are only used to publish preliminary, unofficial results for the public and the media. The sites are not connected to vote counting equipment and could never change actual election results.
Sell disagrees. She told PBS News Hour that the NASS statement shows that secretaries of states aren’t taking the issue seriously. Even if the voting results that can be tampered with aren’t the “real” voting results, she said, the release of bogus results “could cause complete chaos.”
Besides, while the state websites were replicas, the vulnerabilities were not:
The vulnerabilities that these kids were exploiting were not replicas. They’re the real thing.
How do we fix this mess?
On Monday, University of Pennsylvania computer science professor and cryptographer researcher Matt Blaze said that the “overwhelming consensus” among experts is that, for one thing, we need voting systems that are backed up by a paper trail:
Number one question at @VotingVillageDC this week: given how insecure voting systems are, what should we do? Overwhelming consensus among experts:
— matt blaze (@mattblaze) August 13, 2018
1 - Paper ballots (precinct-counted optical scan)
2 - Mandatory risk-limiting audits
3 - More resources to protect back-end systems
That, in fact, is what representatives from DefCon and the Atlantic Council concluded in October 2017.
Things have clearly not changed much in the past 10 months. As The Register reports, besides the kids’ success in flipping the replica state sites onto their backs, the results achieved by the adults in Voting Village included:
- Premier/Diebold’s* TSX voting machines were found to be using SSL certificates that were five years old. One participant used physical access to upload a Linux operating system to the device and turn it into a music-playing device. (Somebody did the same to a WinVote last year: In fact, they Rickrolled it.)
- Diebold’s Express Poll 5000 machines were even easier to crack, thanks to having an easily accessible memory card that can be swapped out while voting. The card contains supervisor passwords in plain text, as well as unencoded personal records for all voters, including the last four digits of their taxpayer IDs, addresses, and driver’s license numbers. When election officials aren’t looking, meddlers can insert specially programmed memory cards and thereby change voting tallies and voter registration information. What’s more, the root password was, for the love of Pete, “Password.” Stored in plain text.
More results of three days of picking apart the country’s ramshackle e-voting technologies:
Voting Village Hack roundup, Day 1 / part 2 (of 2) pic.twitter.com/vqAF4RmZ7C
— DEF CON VotingVillage (@VotingVillageDC) August 11, 2018
Here’s the roundup of the Def Con Voting Machine Hacking Village discoveries, Day 2! @defcon #VotingVillage pic.twitter.com/YncpPxuGnT
— DEF CON VotingVillage (@VotingVillageDC) August 12, 2018
Voting Village discovery roundup, Day 3 (final day). Expect our official report later this year! pic.twitter.com/TGpeCihm13
— DEF CON VotingVillage (@VotingVillageDC) August 13, 2018
The upcoming midterm elections are right around the corner in November. Given the slow, slow progress we’ve seen with addressing vulnerabilities in voting technologies, it’s hard to imagine there won’t be election tampering.
But on the plus side, Blaze said that at least election officials were paying attention at DefCon:
It’s been incredible the response we’ve received. We’ve had over 100 election officials come through here and they expressed over and over again how much they have appreciated learning from this opportunity.
…and on the minus side, earlier this month, Republican senators blocked $250m in emergency election security funding proposed by Senator Patrick Leahy.
Hacking Village cofounder Jake Braun said that the sum needed to be 10x that amount to get the November elections “anywhere close to secure,” The Register reports.
Image courtesy of R00tz.org / YouTube.
Jan Doggen
Please avoid clickbait titles. First it is a replica, later is is “planted bugs”.
Anonymous
I completely agree! This article is a bit below Naked Security’s standards… The security of electronic voting mechanisms is a critically important issue; a story about kids who were guided to attack dummy websites with known, planted vulnerabilities is not helpful, here.
mike@gmail.com
Another Lisa Vaas special.
Anna Brading
You’re right, the headline was misleading. We’ve changed it now.
mike@gmail.com
The title is just as bad as before honestly. Let me fix that for you:
“Children learn to hack on training sites” This has so little to do with elections, the stretch here is obviously being made for political reasons.
Natasha
What’s with the picture? Were they hacking by modifying chips? MSN used almost the same picture.
Hugh Peck
Agree with Jan Doggen. The headline is more fitting for Yahoo “News”, The New York Post or even The National Enquirer. There has been a slow shift on NS away from plain hard computer/internet news reporting, to trying to be “cute”, humorous or sensationalist, often from this author, although certainly not limited to this one. After several years of reading NS I’m about ready to unsubscribe and stop visiting the site.
Claude
Was the kid Russian?!?!?!?!
Decentralized polls, voter ID and paper ballots are great firewalls for the entire process, and future-proof to boot.
John Griffith
I just retired from IT at one of the 5 largest banks in the United States. If there is one thing I have learned since 1985 – If it can be coded, it can be broken. Good Luck USA, the new millennium is upon us. ,
mike@gmail.com
If you think the NASS response that this isn’t a replication of an actual environment isn’t merited, then you don’t know enough about enterprise environments and should definitely go intern in someones IT department before continuing further.
Definitely another click-bait special, and poor journalism.
mike@gmail.com
Let me guess my comments are “stuck in the spam filter again” …
Jim Gersetich
So, if the NASS is so good, where are THEIR testing processes? If they think it’s invalid, why don’t they invite the same 50 kids to try their hand with the real thing? (In a test environment, of course.)
Mahhn
Defcon was great as always, was hoping to see Sophos people again (did 2 years ago) but no luck. All the voting machines were hacked and, web sites – one of the presentations was 2 guys that breached several states absentee voting sites and reported to them the problems and fixes to the host/states (some responded immediately, some refused to listen for months). The conventions closing ceremony noted how realistic the voter hacking village was and urged people there to get involved in protecting our election system against foreign interest. Expect more security fixes from defcon to be implemented than the slackers that make the websites and devices. Word – Password.
Gerry Keane
An Irish Government Minister bought electronic voting machines without proper consultation in 2002. There was a bit of an uproar after the purchase and a commission was set up to investigate if electronic voting machines were secure. The conclusion was they were not secure and without a proper paper trail, you could not verify the election results.
The electronic voting machines were kept in storage, never used and finally sold for scrap 2012. Between purchase and storage, it wasted €55 million of taxpayers money.
Ron W.
Does really someone believes that result websites are based on SQLite databases? And even changing such a result-number on a website is by far not changing the voting result itself. But – of course – the clickbait for DefCon and nakedsecurity is tremendously higher with such posts.