The world’s biggest market for distributed-denial-of-service attacks (DDoSes) – Webstresser.org – has been dismantled, Europol announced on Wednesday.
At least four of the attack-for-hire site’s admins have been arrested, and police are knocking on the doors of its users, some of whom have been arrested and some of whom are just receiving warnings.
Europol says that the service’s top users are in the Netherlands, Italy, Spain, Croatia, the UK, Australia, Canada and Hong Kong. The illegal service was shut down and its infrastructure seized in the Netherlands, the US and Germany.
In its announcement, Europol said that Webstresser is behind more than four million cyberattacks worldwide, though the number may be considerably higher.
On Wednesday, after Croatian police said they’d arrested a 19-year-old man as one of the alleged operators of the attacks-for-hire service, Forbes said that police had boosted the estimated number of Webstresser attacks to six million.
Updated - another arrest was confirmed in Croatia and the number of attacks launched is actually 6 million.
— Thomas Brewster (@iblametom) April 25, 2018
Massive. https://t.co/8j1Y4T5Lae
Webstresser had over 136,000 registered users as of this month. Investigators working on the so-called Operation Power Off arrested the four alleged Webstresser admins on Tuesday in the UK, Canada, Croatia and Serbia.
This was a complex investigation, Europol said. It was led by the Dutch Police and the UK’s National Crime Agency with the support of Europol and a dozen law enforcement agencies from around the world.
The Webstresser attacks targeted critical online services for banks, government institutions, police forces, and people in the gaming industry.
DDoS attacks are blunt instruments that work by overwhelming targeted sites with so much traffic that nobody can reach them. They can be used to render competitor or enemy websites temporarily inoperable out of malice, lulz or profit: some attackers extort site owners into paying for attacks to stop.
Hiring a service to paralyze your enemies’, your competition’s and/or your targets’ sites makes it as easy as simply handing over the money, no technical skill required. Gert Ras, head of the Netherlands National High Tech Crime Unit, told Forbes that Webstresser accepted payments via PayPal and Bitcoin. These guys liked it best when customers paid in virtual currency: Bitcoin payments got users a 15% discount.
DDoS stressers are sometimes marketed as legal testing tools, although they are anything but.
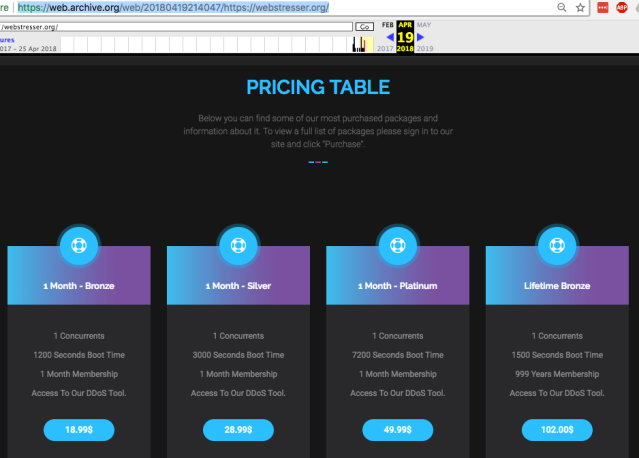
It was cheap. As you can see from Webstresser’s pricing table, archived on 19 April before the site was taken down. Memberships started at the “bronze” level, for EUR 15 or USD $18.99/month, went up to $49.99/month for the “platinum” service, and topped out at $102/month for “lifetime bronze.”
It might well have been cheap, but it was professional. The services Webstresser offered:
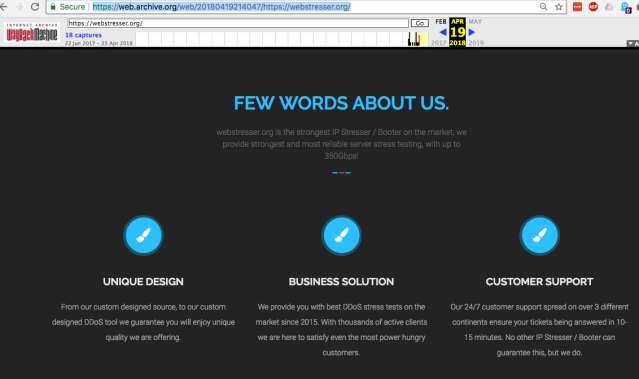
Ras told Forbes that Webstresser is “the most professional” DDoS service he’s seen. It advertised attacks up to 350Gbps. That’s a sizable hit. For the sake of comparison, last month we saw what was deemed to be the largest DDoS to date. The attack peaked at 1350Gbps with a follow-up reaching 400Gbps.
Europol said that some people with technical acumen may get involved in “seemingly low-level fringe cybercrime activities, unaware of the consequences that such crimes carry.”
But those penalties can be severe:
If you conduct a DDoS attack, or make, supply or obtain stresser or booter services, you could receive a prison sentence, a fine or both.
If you’ve got that kind of skill set, Europol says, put it toward something a bit more positive that will earn you an honest buck instead of time behind bars:
Skills in coding, gaming, computer programming, cyber security or anything IT-related are in high demand and there are many careers and opportunities available to anyone with an interest in these areas.

Will
Not that this is material to the story, but I’m guessing “lifetime bronze” is just $102, not $102/month, as that would make little sense. :)
John
You do realize that the way to curb the filth is to arrest more (no “warnings”) and execute those arrested immediately.
John
The moderators must be sipping spirits!