Thanks to Chen Yu of SophosLabs for her behind-the-scenes work on this article.
SophosLabs just alerted us to a malware family that had infiltrated Google Play by presenting itself as a bunch of handy utilities.
Sophos detects this malware as Andr/HiddnAd-AJ, and the name gives you an inkling of what the rogue apps do: blast you with ads, but only after lying low for a while to lull you into a false sense of security.
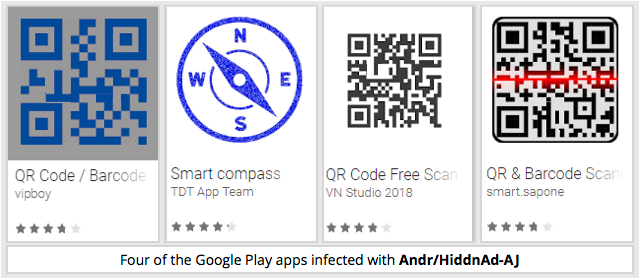
We reported the offending apps to Google, and they’ve now been pulled from the Play Store, but not before some of them attracted more than 500,000 downloads.
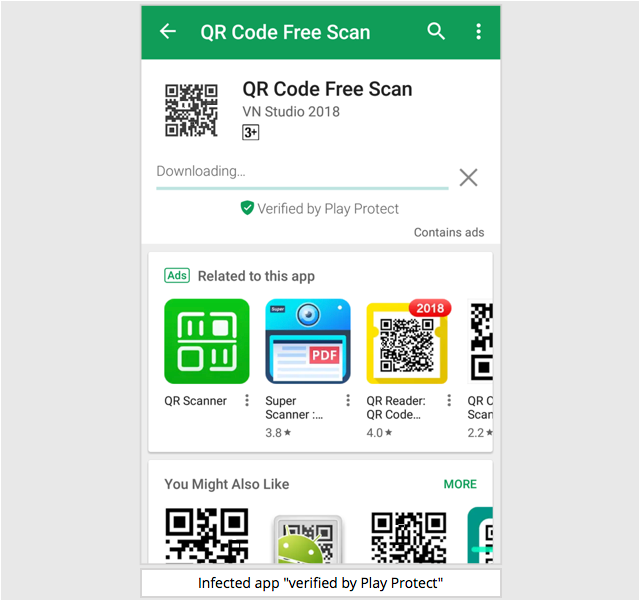
The subterfuge used by the developers to keep Google’s “Play Protect” app-vetting process sweet seems surprisingly simple.
First, the apps were, at least on the surface, what they claimed: six were QR code reading apps; one was a so-called “smart compass”.
In other words, if you were just trying out apps for fun, or for a one-off purpose, you’d be inclined to judge them by their own descriptions.
Second, the crooks didn’t fire up the adware part of their apps right away, lurking innocently for a few hours before unleashing a barrage of ads.
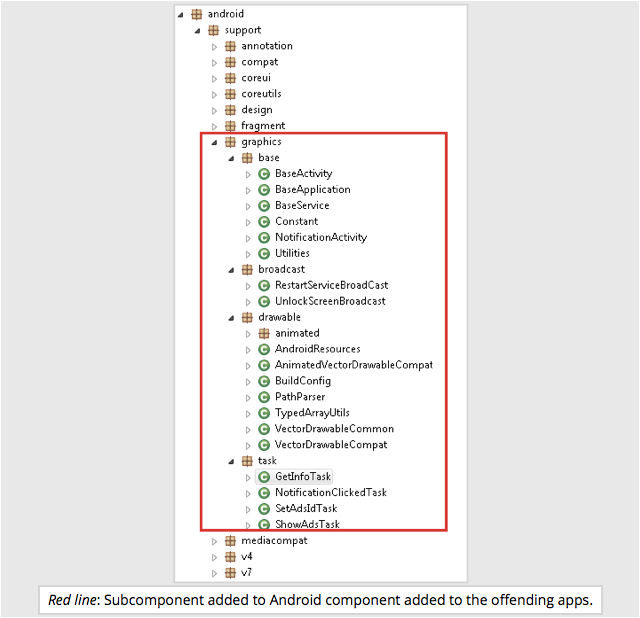
Third, the adware part of each app was embedded in what looks at first sight like a standard Android programming library that was itself embedded in the app.
By adding an innocent-looking “graphics” subcomponent to a collection of programming routines that you’d expect to find in a regular Android program, the adware engine inside the app is effectively hiding in plain sight.
For all its apparent innocence, however, this malware not only pops up advertising web pages, but can also send Android notifications, including clickable links, to lure you into generating ad revenue for the criminals.
When you run one of the these infected apps for the first time, it “calls home” for configuration information to a server controlled by the crooks.
Each configuration download gives the malware:
- A Google Ad Unit ID to use.
- A list of URLs to open in your browser to push ads on you.
- A list of messages, icons and links to use in the notifications you’ll see.
- The time to wait before calling home for the next configuration update.
This makes it easy for the crooks to adapt the behaviour of the malware remotely, changing both its ad campaigns and its aggressiveness easily, without needing to update the malware code itself.
When SophosLabs tested these samples, the first configuration settings pushed out by the crooks were very low-key.
For the first six hours, the list of ads was empty, meaning that the behaviour of the apps was unexceptionable to start with…
…before flooding the device with full screen ads, opening various ad-related webpages, and sending notifications with ad-related links in them, even when the apps’ own windows were closed.
What to do?
As mentioned, Google no longer endorses these apps, and if you install our free Sophos Mobile Security for Android product, we’ll detect and optionally remove these ad-foisting apps if you already have them on your device.
Despite Google’s failure to spot the roguery of these particular “utilities” before blessing them into the Play Store, we nevertheless recommend sticking to Google Play if you can.
Google’s app vetting process is far from perfect, but the company does at least carry out some pre-acceptance checks.
Many off-market Android app repositories have no checks at all – they’re open to anyone, which can be handy if you’re looking for unusual or highly specialised apps that wouldn’t make it onto Google Play (or trying to publish unconventional content).
But unregulated app repositories are also risky, for all the same reasons.
Mahhn
Great job Sophos.
To keep beating the dead horse; Has Google notified any of the 500,000 people that this is malware and should be removed? Or did they just lead to then leave their customers with criminals?
At least facebook apologized, good luck getting that much from google.
Paul Ducklin
I have to admit I don’t know whether current Android behaviour is for the Google Play app to autodelete software that has been disowned by Google since you installed them – I imagine that would be a step too far, in case you had data tied to the app that would get removed.
(I’m currently in my iOS phase – had a few years on Android, now having a few years on the competition.)
Laurence Marks
I’ve wondered this myself–does Google Play delete app deemed to be undesirable. Any idea how you would find out? If Sophos researchers still had samples, they could answer this.
I’ve also wondered why games (Sudoku, Solitaire, etc.) get so many updates when they have minimal permissions. Is it merely to update the embedded ads? How could you tell?
Paul Ducklin
I asked SophosLabs and apparently Google Play itself won’t retroactively remove anything for you, even after an app gets banished. If you have Play Protect turned on, you ought to get a warning next time Google scans your device for malware (or whatever euphemism Google uses it these days) and you would presumably choose to uninstall it at that point…
James
How can Earth be [redacted to preserve QR mystery] when most of us either have or will end up dying here?
Paul
Can you please provide any IOCs regarding the apps (e.g. hashes)?
Paul Ducklin
The 7 hashes I have for the apps referred to here are:
b3b.flashlight.qrcode.barcode.scanner 10e3ceb69f1e4818ebd5e481f9c86c076cd15052559553fdf1a52a00a8059208
twobv2.barcode.qrcode.flashlight.scanner 12b9cff2408db664f136194b13424f2b2372979a66b1cbd2a9aba7fae0adb22c
victory.barcode.qrcode.flashlight.scanner 161cf72020cf3b45726c2416c444bfbef37dd6e833b693fbd379752828f7d762
com.qrbarcode.goit.ftth 2a3a20788f04d5db1818a671d9076ce9374a526bb85c3eefc25fd7f9b584afef
b3b.app.direction.compass 8e4750fcf8bee1fe6e7204ab66c7decba6495c8ab82167fa901a32d0e7e7c87b
smart.qrcode.scanner c0f8d15340d3b3d7a0e3e29a8b78323a446a5af91aedafde1d6ac03abd9fd8e5
rich.barcode.qrcode.flashlight.scanner cf378c1ce9556007f290025d83d1552b8a9b8f73d86a7db200a47d41c8b9c51f
HtH.
Manisha
Can you please share the name of these apps.
Paul Ducklin
See comment above. I added the names to the hashes.
komal
Can you please share the list of apps? or their APK file names?
Paul Ducklin
See comment above. I added the names to the hashes.