In the 2018 Malware Forecast released this week, we see Android malware on the march, with ransomware an ever-increasing threat. According to SophosLabs analysis, the number of attacks on Sophos customers using Android devices increased almost every month in 2017.
The number of malicious Android apps has risen steadily in the last four years. In 2013, just over a half million were malicious. By 2015 it had risen to just under 2.5 million. For 2017, the number is up to nearly 3.5 million.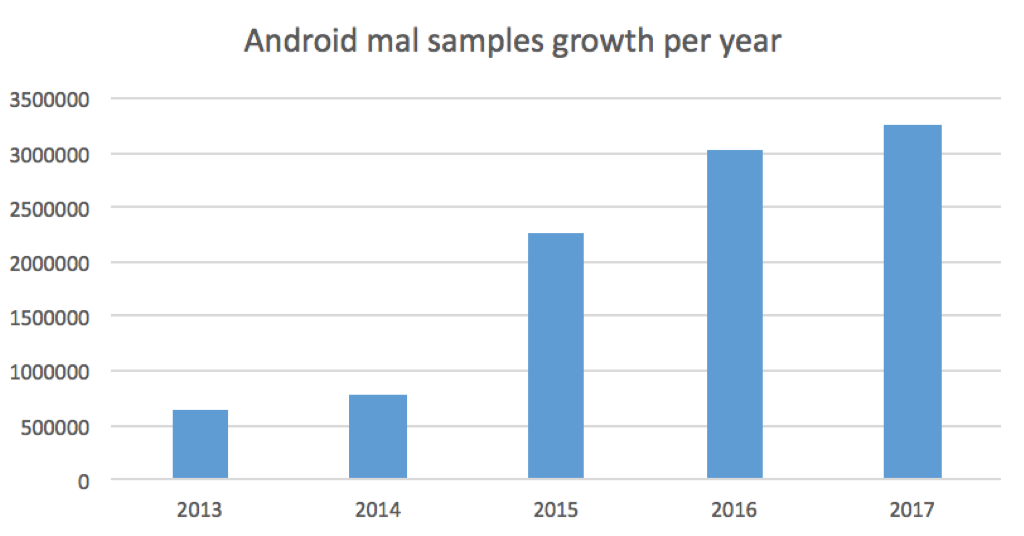
Rowland Yu, a SophosLabs security researcher focusing on mobile malware, said that in September alone, more than 30% of the malicious Android malware processed by SophosLabs was ransomware.
Looking at the top Android malware families since the beginning of 2017, Rootnik was most active – 42% of all such malware stopped by SophosLabs. PornClk was second most active at 14%, while Axent, SLocker and Dloadr followed behind at 9%, 8% and 6%, respectively.
Many apps on Google Play were found to be laced with Rootnik, and that family was also seen exploiting the DirtyCow Linux vulnerability in late September.
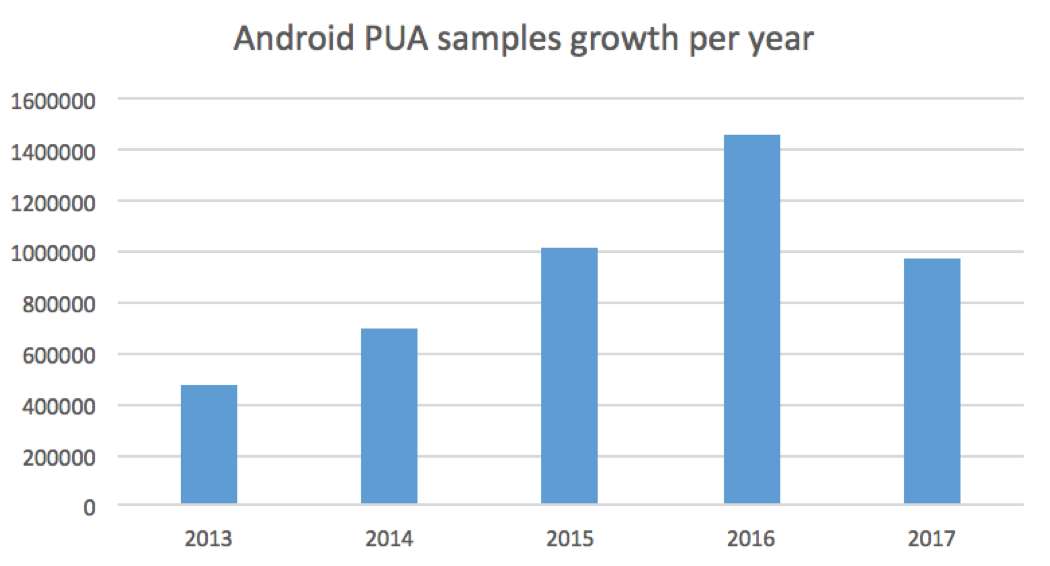
Meanwhile, SophosLabs witnessed a drop in the number of PUAs (Potentially Unwanted Applications – applications that some regard as a problem and others are prepared to tolerate, such as adware).
The numbers had risen every year between 2013 and 2016, but 2017 saw a drop from 1.4 million down to below 1 million.
Of the PUAs seen by SophosLabs this year, Android Skymobi Pay accounted for 38% of all activity, followed by Android Dowgin (16%) and Android Riskware SmsReg (12%).
For more insight into the threat of Android malware, download the Sophos 2018 Malware Forecast. Businesses can protect themselves from the threat of Android malware and PUAs with Sophos Mobile, while home users can protect themselves for free with Sophos Mobile Security for Android.

Leave a Reply