In 2017, attackers developed new ransomware delivery techniques, leading to global outbreaks such as WannaCry, NotPetya and, most recently, Bad Rabbit. It’s a trend that’s expected to continue in the next year, according to the 2018 Malware Forecast released by Sophos on Thursday.
The report reviews malicious activity analyzed by SophosLabs in 2017 to predict what might happen in 2018. Here’s a taster of what the report has to say about this summer’s ransomware activity.
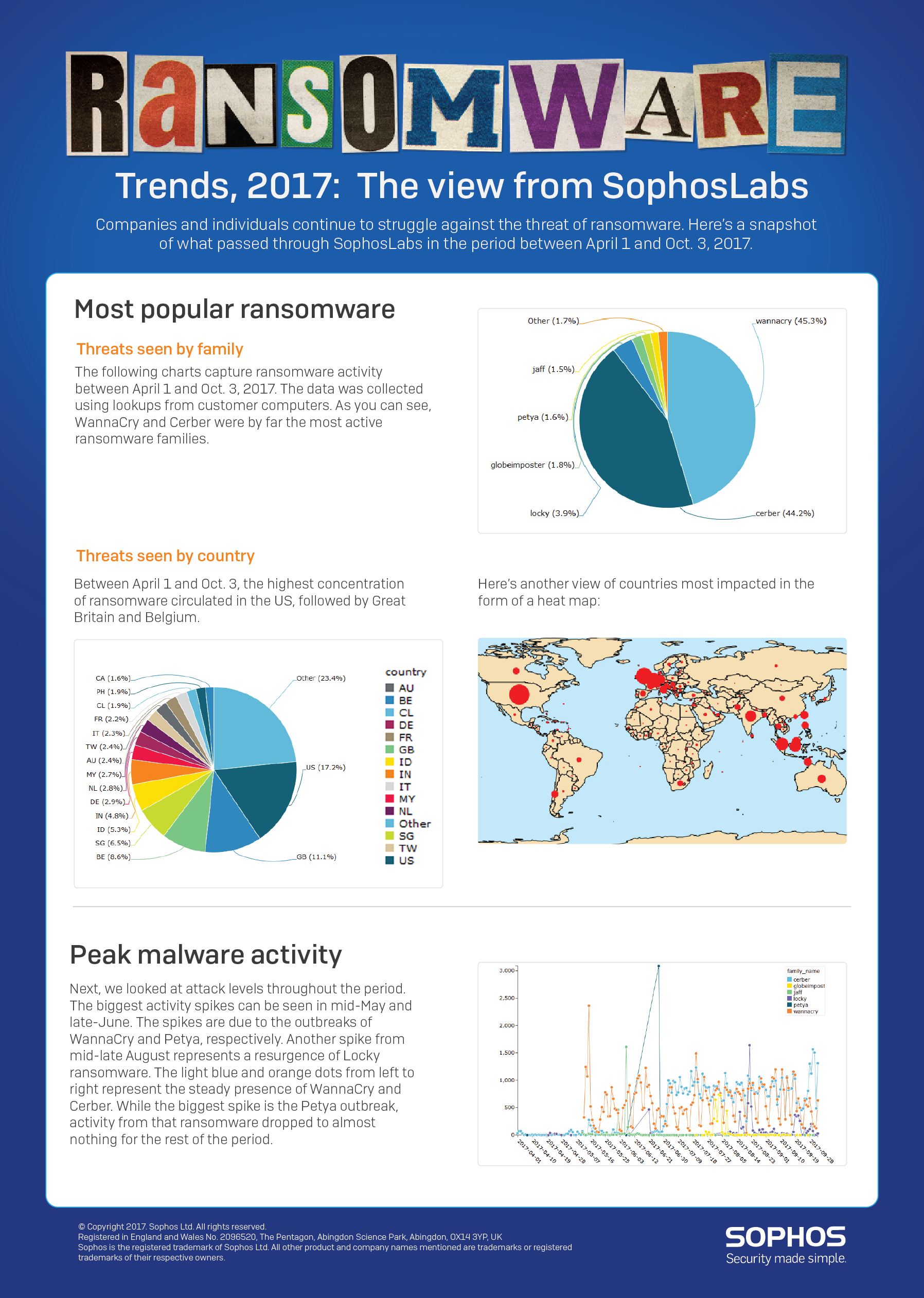
Ransomware from 1 April – 3 October 2017
Ransomware remains a vexing problem for many companies. In the forecast SophosLabs looks at the most prolific ransomware families and attack vectors over a six-month period up to October 2017.
WannaCry
WannaCry, unleashed in May 2017, was the number-one ransomware intercepted from customer computers, dethroning longtime leader Cerber, which first appeared in early 2016.
WannaCry accounted for 45.3% of all ransomware tracked through SophosLabs, with Cerber accounting for 44.2%.
For the first time, we saw ransomware with worm-like characteristics, which contributed to the rapid expansion of WannaCry. This ransomware took advantage of a stolen NSA exploit known as EternalBlue, which targeted an old Windows vulnerability to help it spread.
Even though WannaCry activity has tapered off, SophosLabs researcher Dorka Palotay doesn’t think that’s the last we’ve seen of the techniques it used:
We’re expecting cybercriminals to build upon WannaCry and NotPetya and their ability to replicate, and this is already evident with Bad Rabbit ransomware, which shows many similarities to NotPetya.
NotPetya
The Sophos 2018 Malware Forecast also reports on the acute rise and fall of NotPetya, ransomware that wreaked havoc in June 2017. NotPetya was initially distributed through a Ukranian accounting software package, limiting its geographic impact.
It was able to spread via the EternalBlue exploit, just like WannaCry, but because NotPetya came later it found many fewer machines that were unpatched and vulnerable.
The motive behind NotPetya is still unclear because there were many missteps, cracks and faults in its attack. For instance, the email account that victims were supposed to use didn’t work, and victims could not decrypt and recover their data, according to Palotay:
NotPetya spiked fast and furiously before taking a nose dive, but did ultimately hurt businesses. This is because NotPetya permanently destroyed data on the computers it hit. Luckily, NotPetya stopped almost as fast as it started. We suspect the cybercriminals were experimenting, or their goal was not ransomware, but something more destructive like a data wiper.
Cerber and Locky
With all the sound and fury produced by WannaCry and NotPetya it would be easy to miss the danger posed by older, more persistent threats.
Cerber, an example of Ransomware as a Service (RaaS), is sold as a ransomware kit on the Dark Web and remains a dangerous threat despite being eclipsed by WannaCry in the summer.
The creators of Cerber make money by charging the criminals who use it a percentage of each ransom they’re paid, and are constantly updating it and making improvements in an attempt to stay one step ahead of security software.
Although Locky accounted for barely 4% of the ransomware stopped by SophosLabs it showed signs of resurgence over the summer. New variants displayed the usual Locky behavior, using the same ransom note and Tor payment site, and spread via email attachments like script files and Word documents.
The view from SophosLabs
The trends are captured in the following ransomware graphic, also released today (click to enlarge and use the magnifying glass to zero in on specific stats):
For more insight into what to expect next year download the Sophos 2018 Malware Forecast.

Leave a Reply