A lot of people say you shouldn’t write headlines that contain questions.
Either you already know the answer, in which case you might as well say it outright, or you don’t, which means that your article isn’t going to help your readers figure it out.
But sometimes there isn’t much choice, as happened a month ago when we wrote an article entitled Global spam drops by more than half – now what?
What indeed?
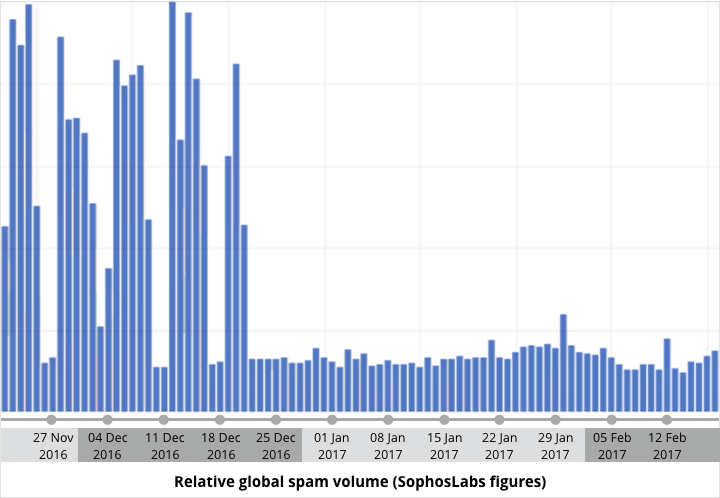
Last month’s story documented a dramatic drop in spam that seemed to be down to a well-known botnet going silent, causing global spam volumes to fall dramatically:
LEARN MORE: How botnets and zombies work ►
That sounds like an unequivocal outcome, so why the question, “What next?”
The reason we asked is that the drop-off in spam didn’t seem to be down to anything that we had done as a community to diminish the size of the botnet:
Why [this botnet, known as Necurs] has gone quiet this time, and how long the “outage” will last, is unknown, as of course is when or if it will return to its former volume. [. . .]
We also know that the Necurs botnet isn’t completely dead, just very much quieter than it was. In other words, if your computer is part of the Necurs botnet, it’s still infected, it’s still awaiting instructions, and it could receive a command to wake up and start sending spam again in the future.
As far as we could tell, most of the people who had been infected just before the spam volume plummeted were still infected afterwards, leaving the crooks free to come back for more at any time.
In other words, the drop in spam rate seemed to be down to the crooks themselves.
Apparently, they took a break from spamming for an as-yet unknown reason that could range anywhere from going on vacation to lying low from law enforcement or some rival gang.
So, “what next” depended on whether we, as a community, took the trouble to check whether we ourselves were amongst the zombified users whose computers could well come back to haunt the internet in the future.
Back to the future
That future might now have arrived, with global spam volumes in the past 24 hours bouncing back up to about half the level of the peaks shown in the graph above.
Yesterday, the hourly spam rate topped out more than five times higher that what you might call the background spam rate above, making it look as though the “resting” Necurs zombies still out there and undetected have been called back into service.
Interestingly, this time it isn’t malware that’s being blasted out, but an old-school type of scam that we’ve haven’t seen for a while, mainly because it didn’t work very well in the past: pump-and-dump.
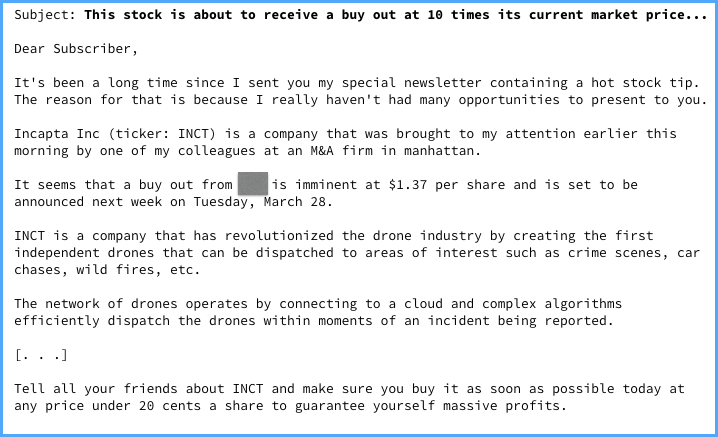
Instead of phishing recipients into clicking malicious links, taking dodgy surveys or opening booby-trapped attachments, you talk them into buying shares:
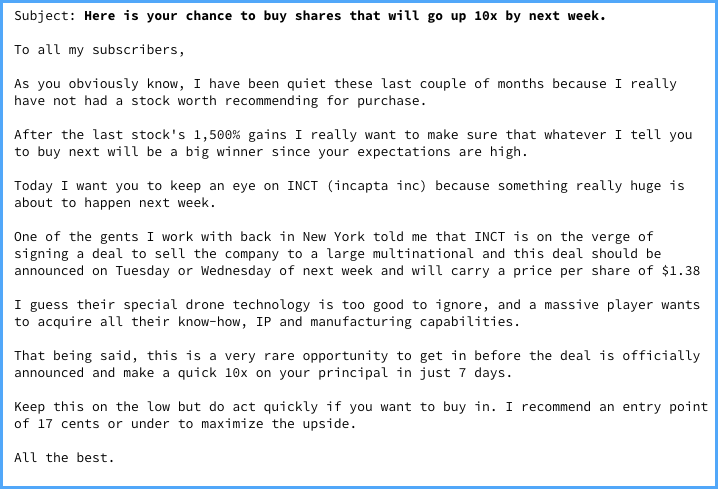
The theory is that if you pick a cheap stock, concoct a believable story to talk it up, and buy in just before your victims start receiving their emails…
…then your initial bulk purchase will push the stock up a bit, add veracity to your claims that the stock will soon be flying, and encourage more and more victims to buy into the scam, pumping up the stock further and further.
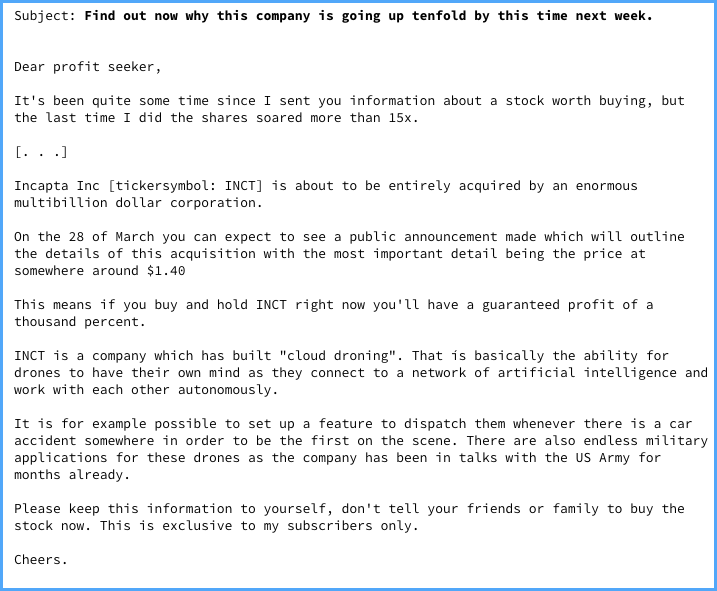
When you’ve waited as long as you dare (you need to get out before word gets around amongst either the community or the regulators!), you dump your stocks for a tidy profit and leave your victims to find out whether their shares will hold their value or, more likely, settle swiftly back to their former levels or worse.
Did it work?
The timing of this scam was interesting.
InCapta, Inc (INCT), the company targeted in this scam, is what is often called a “penny stock”, listed by an alternative securities company in the USA called OTC, formerly Pink Sheets.
OTC’s most informal market is called OTC Pink, and it comes with some clearly-labelled risks:
The Pink Open Market offers trading in a wide spectrum of securities through any broker. With no minimum financial standards, this market includes foreign companies that limit their disclosure, penny stocks and shells, as well as distressed, delinquent, and dark companies not willing or able to provide adequate information to investors. As Pink requires the least in terms of company disclosure, investors are strongly advised to proceed with caution and thoroughly research companies before making any investment decisions.
But even a tiny amount of research into INCT would reveal it claims to be a media company that makes TV shows, amongst other things, and that on the day of this spam campaign, it apparently issued a press release of its own announcing a new weekly programme it would be doing.
Not a word about drones, or about cloud computing, or indeed about anything to corroborate the spammers’ claims at all.
At first sight, it looks as though the scam worked: the share price rose steeply at the start of 2017-03-20, closing at 13 cents on Friday but hitting 24 cents by 09:30 on the Monday morning
The price then wandered back down to about 15 cents over the day’s trading:
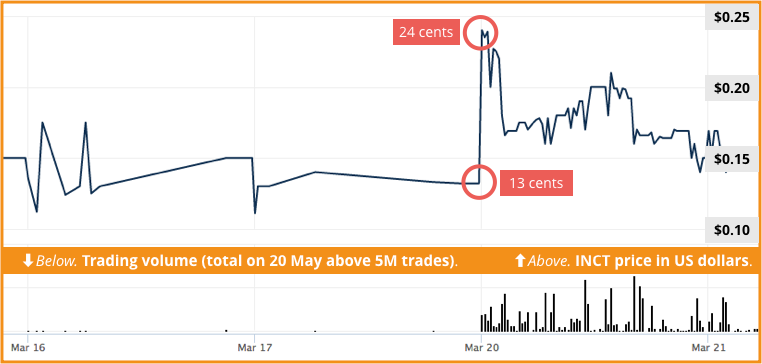
With more than five million trades on Monday, the INCT shares were busier that they have been for the past year; ironically, however, only a small number of those trades happened at the peak price of 24 cents, which would have limited the amount of “dump money” that anyone could have extracted at that peak.
We suspect that spam recipients were also influenced by a dramatic 17-fold rise in INCT’s price just three months ago, where about two million trades happened at a price point of just 7.5 cents, followed by a rise over Christmas until the price had reached $1.31, very close to the spammers’ recent promises:
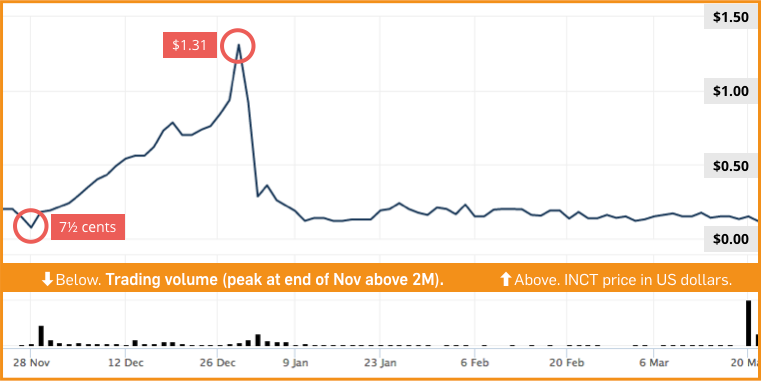
Someone may well have cashed out fairly tidily in January 2017 (we haven’t found evidence of an INCT stock spam at that time, in case you were wondering), and that part of the stock price graph may very well have convinced people that this week’s third-party claims offering 100% returns were legitimate after all.
What to do?
- If it sounds too good to be true, assume that it is.
- It if sounds illegal, assume that it is.
- If it’s an unsolicited bulk email that swears you to secrecy…
…you and the other 30 million recipients, then, please…
Stop. Think. Before you connect. (Or, in this case, don’t connect.)

Adam
Wouldn’t that bit about “I found out from a friend that works at this company about an upcoming deal that hasn’t been announced yet and will boost their stock price 10x” be considered Insider Trading if one acted on that info and bought the stock? Or am I off-base, here?