Apple just released iOS 10.2, the latest upgrade for its iDevices.
Lots of the articles you may have seen so far talk about the new features that were introduced, listed by Apple on the Software Update screen as follows:
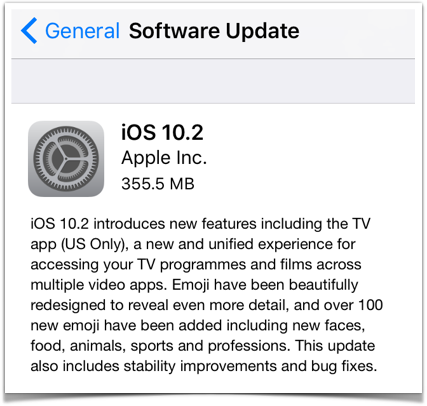
So, there’s a “new and unified experience for movies and TV shows”, but only in the US, and more than 100 new emojis.
We weren’t sure about the plural of emoji, for which our trusty New Oxford American Dictionary offered either emoji or emojis. We decided not to be like sheep, plural sheep, and plumped for emojis.
Of course, the reason for getting this update isn’t really so you have access to a bunch of newly miniaturised food icons, but on account of security.
One big reason for updating is a recently reported trick to bypass the Find my iPhone security feature.
In an ironic bug, activating Find my iPhone is supposed to make your phone almost impossible for a crook to use, including making it effectively worthless for resale.
But to make the feature work, your device needs to be inaccessible to someone who picks it up, yet able to connect to a network so that you can go through the online security validation needed to remove the Authentication Lock if you get the device back.
That means popping up the iOS connection dialog so you can choose a network and enter a Wi-Fi password if needed, and that’s where researchers found a bypass.
By entering an absurdly long password until the processor began to bog down, and then loading up the CPU even more by rotating the screen back and forth, as well covering and uncovering the webcam to change the brightness, they crashed the dialog.
With a bit of luck and good timing on the Home button, they could get to the main screen, apparently without authenticating, thus skipping over the Authentication Lock and effectively rendering Find my iPhone useless.
It seems that the bug allowing a crook to bypass the lockout (and presumably to resell your device without getting caught out), designated CVE-2016-7638, has now been fixed.
Five more lockscreen holes
It turns out, however, that the 10.2 update patches a whole raft of other lockscreen problems, including ones that could be considered more serious.
In Apple’s own words:
- CVE-2016-7664. A person with physical access to an iOS device may be able to access photos and contacts from the lock screen.
- CVE-2016-7601. The device may not lock the screen after the idle timeout.
- CVE-2016-7653. A user may be able to view photos and contacts from the lockscreen.
- CVE-2016-4781. A person with physical access to an iOS device may be able to unlock the device.
- CVE-2016-7597. A person with physical access to an iOS device may be able to keep the device unlocked.
There were also two remote code execution bugs – the sort of hole that can be used for a jailbreak if you’re a good guy, or to implant malware if you aren’t.
One vulnerability involved booby-trapped USB devices, referred to as “image devices”, though Apple isn’t saying if that means storage devices like SD cards, or capture devices like microphones and keyboards.
Plugging in what Apple rather generically calls a “malicious HID device” (HID is short for human interface device, so HID device is tautological) can cause your iPhone to run unauthorised program code.
What to do?
Given the numerous lockscreen problems, we consider this an urgent update.
Head to Settings | General | Software Update if you haven’t updated already.
(We updated almost immediately after receiving the security announcement email via the Apple Product Security mailing list, and have had no problems at all after a full working day of phone use, for what that recommendation is worth.)

Leave a Reply