
The US Federal Communications Commission (FCC) has fined a telecommunications company a whopping $750,000 (nearly £500,000) for blocking consumers’ Wi-Fi “personal hotspots” at convention centers around the country.
The FCC announced the fine on Tuesday, saying that Smart City Networks had been blocking personal hotspots being used by convention visitors and exhibitors who used their own data plans rather than paying Smart City “substantial fees” to use its Wi-Fi service.
Most modern mobile phones have a connection-sharing option (personal hotspot on iOS, portable hotspot on Android and internet sharing on Windows Phone) that lets you hook up one or more devices to the phone via Wi-Fi, and then connect onwards to the internet via the phone’s 3G or LTE data connection.
The FCC’s release quotes Travis LeBlanc, Chief of its Enforcement Bureau:
It is unacceptable for any company to charge consumers exorbitant fees to access the Internet while at the same time blocking them from using their own personal Wi-Fi hotspots to access the Internet.
All companies who seek to use technologies that block FCC-approved Wi-Fi connections are on notice that such practices are patently unlawful.
The company’s response: “We didn’t know that!”
Smart City said in a release that it hadn’t known that it was against FCC rules to use standard, out-of-the-box technology in order to prevent wireless devices from disrupting the operations of neighboring exhibitors on convention floors, having received no prior notice before the FCC contacted it in October 2014.
That’s also when the FCC slapped Marriott with a $600,000 fine (nearly £400,000) for blocking Wi-Fi access at its Gaylord Opryland Resort and Convention Center in Nashville, Tennessee.
Marriott didn’t go down without a fight: it banded together with the American Hotel and Lodging Association to try to talk the FCC into changing the rules and allowing it to keep blocking personal hotspots.
Marriott gave in and stopped blocking hotspots in January 2015, although it said at the time that it was going to keep on trying to get the FCC’s blessings on blocking.
The hotel chain maintained that it hadn’t intended to block personal hotspots in guests’ rooms or in lobbies, but that it was asking the FCC to allow the practice in conference rooms or other meeting spaces.
“It’s all about Wi-Fi security,” Marriott said: specifically, ensuring that guests using its Wi-Fi were protected from rogue wireless hotspots that it said could degrade service, from “insidious cyber-attacks”, and from identity theft.
“Riiiiight,” skeptics said, “it’s about security, not about what the FCC said was a charge of $250 to $1,000 per device to get onto the internet at a Marriott property.”
For its part, Smart City said that blocking hotspots resulted in “significantly less” than 1% of all devices being deauthenticated and that these same technologies are “widely used by major convention centers across the globe as well as many federal agencies.”
While Smart City thinks it has legal standing to fight the fine, its president, Mark Haley, said in the company’s release that the battle would be too costly and too much of a distraction.
But even if Smart City thinks it might have had a chance to fight, given that its case goes back to 2014, there’s no way to say “I didn’t know that” any more.
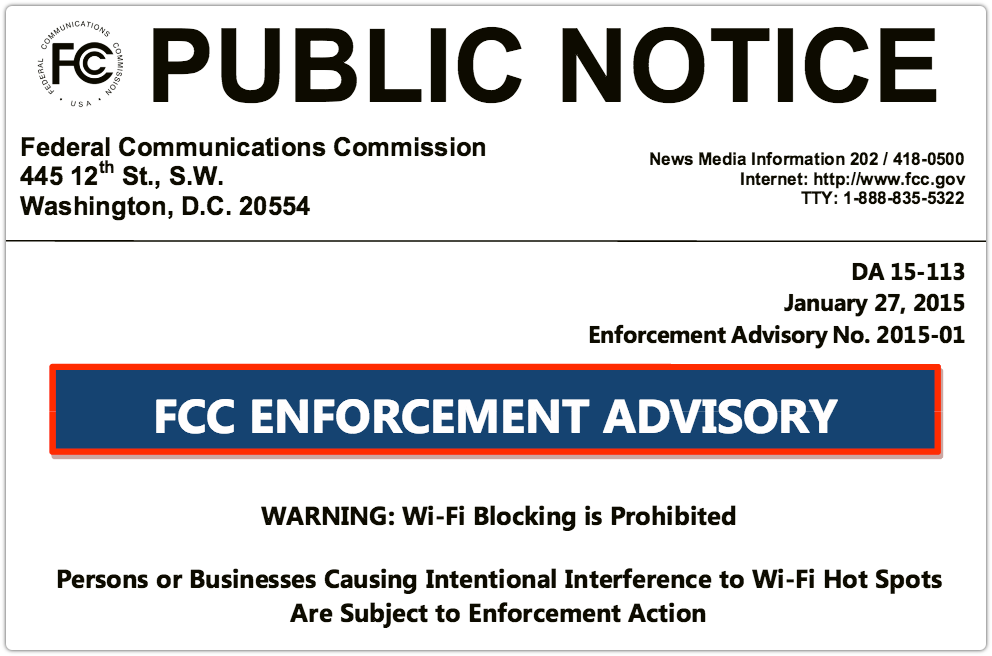
Back in January 2015, the FCC published DA 15-113A1, its first Enforcement Advisory of the year.
Let’s just say that this notice didn’t exactly mince its words:
WARNING: Wi-Fi Blocking is Prohibited
Persons or Businesses Causing Intentional Interference to Wi-Fi Hot Spots Are Subject to Enforcement Action

JR
I’d like to know what exactly these companies are using to block the signals… just some general frequency jamming? If so, the FCC should also be going after whoever makes such a device.
Charles Lawry-Martinez
When I read it my first assumption was they are purchasing the signal blockers that are used for things like movie theaters. So they are available to these companies to purchase, I guess there just isn’t any oversight on what said companies can use them for. Although using them to drum up more money for yourself seems like a straight forward no-no. And the security logic Marriott gave was a joke. I could pay to connect to their wireless with my wifi pineapple and then rebroadcast and have a physical and mobile man in the middle attack anyways. For the small cost of their internet I could make a ton in stolen data. I also have a personal signal blocker, but it has always been for security testing. Example being can I hook up my cantenna to the jammer and broadcast it concentrated at my hovering drone and cause it to lose the connection with the controller and get it stuck in whatever it’s last command was. So I don’t know about making these completely illegal, but there should be more laws around what you can use them for.
Paul Ducklin
According to the FCC, it’s pretty simple: Wi-Fi blocking is prohibited. End of story.
Michael Sparks
It’s definitely a new twist on the historic ban on “jamming.” Jamming in the traditional sense is interfering with an RF transmission by transmitting over or beside it so as to disrupt the signal. What Marriott was doing was not interfering with the RF transmission at all, but following the rules of 802.11 networks to send a deauthentication packet. The CB equivalent of this is transmitting on top of another person who is trying to talk (illegal) vs inserting yourself into the conversation and telling them to shut up (legal). I’m a little surprised they haven’t taken the viewpoint that this is IEEE 802.11 functioning as designed, and that maybe the standard needs an addendum on handling unwanted traffic like that.
jkwilborn
Just shows how they ‘care’ about you. Just a normal person would say that it’s not right to block wifi. If they cared, they wouldn’t…
Jack
TR Barrett
JR,
I think I saw this on here when the Marriott WiFi blocking went down or I may have saw this on another page.
But Marriott was using a device that carefully crafted a packet that made it seem that your WiFi connection was falling out of sync or de-authenticated.
I agree with you, they should be going after not only just the people deploying these devices but the manufactures too. (The enforcement bureau did this with the cell phone quiet zone technology. And huge fines for users of these devices.)
Hope this helps!
Betan Testravosky
On the Delaware Expressway into Philadelphia a lot of commuters have personal signal jammers in their cars to whack other drivers on the expressway who are driving talking/texting on their phones. You can pick them up for a reasonable price on eBay from China … like fireworks, not illegal to own it – you’re just not supposed to use it.
4caster
Is this problem common outside the USA? As a BT customer in the UK I sometimes try to make VOIP calls (BT SmartTalk, Skype or FaceTime) through BT WiFi Hotspots in places like motorway service areas, airports, train stations or large shopping malls. Usually I can obtain no VOIP connection, and often no WiFi service at all. Is this because operators of such places are jamming VOIP calls?
James B
They use de-authentication packets as part of the 802.11 protocol. This effectively ties the client up trying to authenticate to the hotspot. This is an old DoS hack put to a new use. It is called jamming, but it is not jamming in the traditional RF sense.
Paul Mew
It’s pretty standard in most enterprise wireless kit now, it basically DOS’s the ‘rogue’ access point. To be fair the technology is intended to improve security, but it sounds like that’s a side-benefit here, with the main goal being revenue.
Paul Ducklin
Bumping someone off a WPA2 access point that they control themselves and that has a password no-one else knows, and forcing them onto an alternative access point that is either open or uses a password that everyone currently on the network has been given…
..is supposed to *improve* security?
Charles Lawry-Martinez
I replied to the first comment on this article before reading the others, but that was my first thought when I read the Marriott response as well. If they are using de-authentication packets and forcing people to connect to their networks it’s the same logic as my wifi pineapple except instead of data collection to turn into revenue later down the line you are going straight for the revenue stream by setting yourself up as the gatekeeper to the internet. I have a feeling the comments Marriott made on this matter will be taken as a challenge by some people.