 Until Tuesday, the state of Virginia was using what one expert dubbed the “worst voting machine in the US” – one with security so appalling that all it would take to compromise it would be a laptop with a wireless card and some free software.
Until Tuesday, the state of Virginia was using what one expert dubbed the “worst voting machine in the US” – one with security so appalling that all it would take to compromise it would be a laptop with a wireless card and some free software.
Immediately following the publishing of a scathing report on Tuesday by the Virginia Information Technologies Agency (VITA), the Virginia State Board of Elections decertified use of the machines.
The audit was triggered by the voting machines having repeatedly crashed in the November 2014 election.
As North Carolina Public Radio reports, interference from a mobile phone (an election official was streaming music) was suspected of causing the crashes.
But when state auditors investigated, they didn’t find that particular problem.
They found a far more serious problem, discovering that mobile phones were able to connect to the machines’ wireless network, used to tally votes, and that the passwords were as easy to guess as “abcde”.
The auditors were able to easily change the vote counts remotely, without detection.
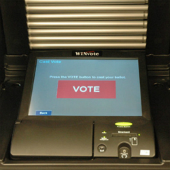
The system at the heart of the matter is the AVS WINVote touchscreen Direct Recording Electronic (DRE) machine, made by Advanced Voting Solutions.
It was used in a long list of Virginia counties in 2014, passed the required Voting Systems Standards of 2002, and was used in Pennsylvania and Mississippi until a few years ago.
Its flaws include things that are making infosec pros wince, such as the use of the Wired Equivalent Privacy (WEP) protocol to secure its Wi-Fi network.
The international tech group IEEE deprecated the protocol in 2004, and in 2005, the FBI gave a demo in which it cracked it in 3 minutes with publicly available tools.
WINVote also committed egregious password sins, the report found, using hard-coded, easy-to-crack passwords – “admin,” “abcde,” and “shoup” (the name of the company that preceded Advanced Voting Solutions) – to lock down its Windows administrator account, Wi-Fi network, and voting results database, respectively.
Jeremy Epstein, of nonprofit SRI International, is a security expert specialising in e-voting who served on a Virginia state legislative commission investigating the voting machines in 2008 and has been trying to get them decertified ever since.
He summed up the flaws like this on his Freedom to Tinker blog:
The vulnerabilities were so severe, and so trivial to exploit, that anyone with even a modicum of training could have succeeded. They didn’t need to be in the polling place - within a few hundred feet (e.g., in the parking lot) is easy, and within a half mile with a rudimentary antenna built using a Pringles can. Further, there are no logs or other records that would indicate if such a thing ever happened, so if an election was hacked any time in the past, we will never know.
And these are the steps he said that somebody could take to easily change election results, with minimal technical expertise:
- Take your laptop to a polling place, and sit outside in the parking lot.
- Use a free sniffer to capture the traffic, and use that to figure out the WEP password (which VITA did for us).
- Connect to the voting machine over WiFi.
- If asked for a password, the administrator password is "admin" (VITA provided that).
- Download the Microsoft Access database using Windows Explorer.
- Use a free tool to extract the hardwired key ("shoup"), which VITA also did for us.
- Use Microsoft Access to add, delete, or change any of the votes in the database.
- Upload the modified copy of the Microsoft Access database back to the voting machine.
- Wait for the election results to be published.
Why can’t the vendor fix the machines, you may well ask?
Because it’s no longer around, Epstein says. Its domain is now owned “by a Chinese organization of some sort.”
But even if the vendor hadn’t gone belly-up, these problems aren’t easy to fix, he said – particularly given that VITA only “scratched the surface”, using mostly off-the-shelf, open source tools, and what it found “was undoubtedly the tip of the iceberg.”
The systems don’t keep logs, so there’s no easy way to determine if they’ve been tampered with in the past.
If the rigging of votes hasn’t yet been tried on these systems, he said on his blog, it’s only because it hasn’t occurred to anybody:
If an election was held using the AVS WINVote, and it wasn’t hacked, it was only because no one tried.
Bottom line is that *if* no Virginia elections were ever hacked (and we have no way of knowing if it happened), it’s because no one with even a modicum of skill tried.
Unfortunately, Virginia voting officials are going to be hard-pressed to swap out these machines, both because of the expense and the time crunch.
Officials in Fairfax City, Virginia, told North Carolina Public Radio that it will cost about $130,000 (about £87,000) to replace each WINVote machine.
Plus, there’s an election right around the corner, in June.
The city’s general registrar, Kevin Linehan, thinks it’s riskier to roll out a new system than it is to react to the possibility of tampering.
North Carolina Public Radio quotes what he said to the state board:
My most vulnerable aspect of running an election is having properly trained officers of election. I'm looking at a very short timeline getting my officers trained in a whole new system.
Karen Alexander, who runs elections in Powhatan County, isn’t sure what to do but told the radio station that her county might borrow machines to get through June’s primary.
If worse comes to worst, she said, they’ll count the votes by hand.
Epstein’s take:
I feel for the local election officials who will have many sleepless nights to replace the WINVote systems.
Unfortunately, they have no choice, he said: the only alternative is criminal negligence.
Image of AVS WINVote from VerifiedVoting.org
Tom
Well, at least it wasn’t 12345678. The problem is that so any devices that get connected to the Internet have factory installed users with standard passwords. We have a PBX system on our network that had a user, tech, with that perennial favorite 12345678 as the password. Hackers attempt to find an open port on my firewall once every four minutes, if you know the IP and the port and you get a login screen for a name brand system (HVAC, PBX, DVR, etc.), try one of the default users and chances are you will get into the device. One phish that gets taken can give you a network user, and 40M credit cards for sale.
t1nym1ght
If you look at American election results closely, it’s pretty obvious tampering with electronic votes is pandemic.
For instance you’ll find numerous precincts in which a top-tier candidate received absolutely no votes, out of thousands cast. This is statistically possible, but highly unlikely. Plus there are always stories at the local level where someone who voted for the candidate that got zero votes steps forward and complains that their vote was obviously not counted.
Those stories never get national attention, of course. Like Stalin said it’s not the vote that counts, it’s who counts votes…
Chris
Let’s be honest; would it have really mattered if election results were hacked in the past?
Reader
Online voting spells the death of democracy. Though the U.S. is too big to be a democracy, its voting computers have killed all vestiges of the country’s democratic ideals. Most, if not all, of our voting computers have been hacked – and that is no accident. Cui bono?
RocRizzo
Democracy is already dead in the US. It is now an oligarchy. The US has the best government that corporate money can buy.
Stampy
No technical skills available to maintain & monitor them.
No logs or audit trail.
No manufacturer support.
No serious testing (clearly!)
Used to verify the very most basic layer of Democracy, Voting.
Only in America, the Land of the Free.
Words fail me, they really do.
RocRizzo
The “Help Americans Vote Act,” should have been called the Hinder Americans From Voting Act. It put in place the requirement of these hackable electronic machines. And who does the US have to thank for this? None other than the only president appointed by the Supreme Court. None other than George W. Bush, and his cronies in the Congress and Senate. They pushed it through quickly, and even after testimony from people who showed that these systems are hackable.
The systems are also made by companies who give large campaign donations to candidates. This should be forbidden.
So, another criminal act by the Bush Crime Syndicate. Please tell me again why these people are not in jail.
Cjcrowder
Make this outrageously unlawful most obvious flaw in our election results news on every network-social and public today