 As much as we try to help computer users to get smarter about social engineering, cybercriminals are devising attacks that are smarter and sneakier than ever.
As much as we try to help computer users to get smarter about social engineering, cybercriminals are devising attacks that are smarter and sneakier than ever.
Social engineering attacks threaten your business security at its weakest point: your users. SophosLabs detects enormous volumes of spam designed to spread malware to unwary people who should know better, but are sometimes fooled.
Spam brings malware and phishing
James Lyne, Global Head of Security Research at Sophos, warns that social engineering attacks are getting more advanced as operating systems become better secured. “There are certain stereotypes about these kinds of spam messages, but they aren’t always true,” James says in an interview with SCMagazineUK.com. “For example, scam messages don’t always have bad English, poor copies of logos or really obviously dodgy links. Sometimes they look practically identical to legitimate messages.”
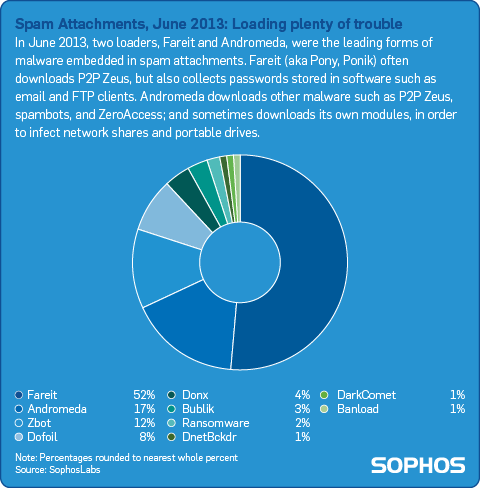
We saw many targeted attacks against users and businesses in 2013 using convincing spam emails disguised as legitimate ones. These hoax messages may attempt to trick users into divulging their usernames and passwords (known as phishing). And spam can deliver dangerous Trojan payloads: malware that compromises a computer when a user unknowingly opens a malicious file. As we reported in our Security Threat Report 2014, most of the malicious spam attachments we saw in June of 2013 were carrying loaders like Zbot/Zeus, which the cybercriminals use to load (or drop) other malware onto your infected computer.
Zbot delivering dangerous ransomware
Malicious spam attachments such as Zbot are increasingly loading the dangerous ransomware known as Cryptolocker, which encrypts all of the data and files on your computer and demands a ransom of up to $1,000 to set your files free.
One particularly tricky spam attack SophosLabs detected recently exploits the growing awareness of Cryptolocker to trick users into downloading a fake security “patch” to protect against “new malware circulating over the net,” allegedly from security vendors. (Security companies will never deliver patches in an email.)
According to Naked Security blogger Paul “Duck” Ducklin:
The email doesn’t explicitly mention the Cryptolocker ransomware that locks your files and tries to sell them back you. But there is little doubt that many recipients, having heard of the ongoing saga of Cryptolocker, will be more inclined than usual to read on.
In this fake security patch attack, the attachment is Zbot. According to Duck, Sophos detects this malware proactively for Windows as HPMal/Zbot-C. Sophos on non-Windows platforms, including gateway products, detects the malware’s various components as Troj/Agent-AEWF and Troj/Agent-AEWG. Sophos web and email filters proactively quarantine attacks of this sort by identifying the file as suspicious.
Another popular type of spam attack is the spoofed shipping delivery notice, which claims to come from the postal service in your country (e.g., USPS, Royal Mail and Canada Post) or a well-known delivery company (e.g., UPS, FedEx and DHL). We saw an increase in this type of attack during the holiday shopping season, as well as numerous Black Friday and Cyber Monday themed spams promising outlandish deals.
Targeted attacks against Mac users
Not even Mac users are immune to the threat of social engineering. According to our Security Threat Report 2014, last year Sophos identified backdoor Trojans that compromised Macs in Asia through Word documents claiming to discuss human rights abuses in Tibet. We also reported that, in February of last year, Apple employees’ Macs were compromised by hackers via a zero-day Java vulnerability. The targeted attack also victimized Facebook and Microsoft Mac business users at around the same time. These attacks may reflect hackers’ recognition that it’s easier to attack businesses through social engineering, rather than to attack the target company’s well-defended infrastructure.
Download our Free Mac Antivirus to stay protected from Mac malware.
Train your users about social engineering, phishing and spam
We can help you train and educate users about social engineering attacks. Our free security guide, called Threatsaurus, offers tips and simple explanations and a quick-reference glossary of threats. Threatsaurus includes an online version of definitions and tips for users to avoid phishing, spam and other types of security threats.
Watch this video featuring Duck’s explanation of how you can use Threatsaurus to educate your organization.
Learn more about email security
For more information about email threats, and how to protect your sensitive data, download our free whitepapers: Who’s Snooping on Your Email?, and Don’t Let Data Loss Burn a Hole in Your Budget. These papers help you identify data threats and show you how to implement a practical data loss prevention strategy (registration required).
Sophos SafeGuard Enterprise
We make it simple for you to manage your security policies and data protection across your organization. With SafeGuard Enterprise, you’ll be ready to comply with data privacy laws and keep the wrong people from seeing your organization’s or your customers’ confidential information.
- Uses a single console to manage full-disk, removable media, file-share, and cloud storage encryption
- Provides up-to-date security status for all your devices with reporting and auditing that lets you monitor and enforce compliance with internal policies and external regulations
Sign up for a free 30-day trial today.
Video: Sophos expert talks Syrian Electronic Army hack of Skype on Bloomberg TV | Sophos Blog
[…] Chet explains, Skype employees were tricked by social engineering into turning over the Twitter account password. Apparently, Skype was not making use of a security […]
Decoding Cryptolocker: How it works and how to protect your files (Presentation) | Sophos Blog
[…] the presentation below, Chet shows you the various methods of infection: from opening a malicious spam attachment to visiting booby-trapped websites, or by silent infection from malware droppers already on your […]
Botnets, zombies, and the wide world of spam (Podcast) | Sophos Blog
[…] your daily email is junk. Not only does spam make up the vast majority of all email, spam emails can carry nasty viruses that perpetuate the […]
What’s coming in Sophos UTM Accelerated (9.2): #5 – Advanced Threat Protection (ATP) | Sophos Blog
[…] date. That means the technology to protect you from viruses, email spam, web and other malware, phishing attacks, etc. Those are still the most common tools used in the initial stages of a targeted […]
Cryptolocker surfaces in fake UK Royal Mail emails, many victims willing to pay | Sophos Blog
[…] There is no chance to break the encryption, so even removing Cryptolocker won’t get your files back. We advise that you always keep your computer protected with security software, and back up your files so you can get always them back. Also, don’t open attachments in emails from people you don’t know — the cyber crooks are especially good at tricking people through social engineering. […]
April Fools! Sophos pranks our own employees – in a good way | Sophos Blog
[…] You never know when an email might be trying to trick you into giving away your passwords or downloading malware. […]
How do APTs work? The Lifecycle of Advanced Persistent Threats (Infographic) | Sophos Blog
[…] means you need the technology to protect you from viruses, email spam, web and other malware, phishing attacks, and more. Those are still the most common tools used in the initial stages of a targeted APT […]