Several months of relative calm are over for Windows administrators, as Microsoft on Tuesday released 147 patches affecting ten product families. Windows takes the lion’s share of patches with 90, with 38 for SQL Server (including ten shared with Visual Studio). The rest are spread among .NET, 365, Azure, Defender for IoT, Office, Outlook, and SharePoint. There are three critical-severity issues, all affecting Defender for IoT.
At patch time, three issues, all important-severity faults affecting Windows, are known to be under active exploit in the wild. One (CVE-2024-26234, a driver-related issue reported to Microsoft by Sophos) is publicly disclosed, as we’ll discuss below. Eleven more important-severity vulnerabilities in Windows are by the company’s estimation more likely to be exploited in the next 30 days. Six of the issues addressed are amenable to detection by Sophos protections, and we include information on those in a table below.
In addition to these patches, the release includes advisory information on five patches related to the Edge browser and five from Intel, Lenovo, and Red Hat; the regularly scheduled servicing stack updates are also included in advisory material this month. We don’t include advisories in the CVE counts and graphics below, but we provide information on all of them in an appendix at the end of the article. We are as usual including at the end of this post three other appendices listing all Microsoft’s patches, sorted by severity, by predicted exploitability, and by product family.
By the numbers
- Total Microsoft CVEs: 147
- Total Edge / Chrome advisory issues covered in update: 5
- Total non-Edge, non-Microsoft advisory issues overed in update: 5
- Publicly disclosed: 1
- Currently exploited: 3
- Severity
- Critical: 3
- Important: 142
- Moderate: 2
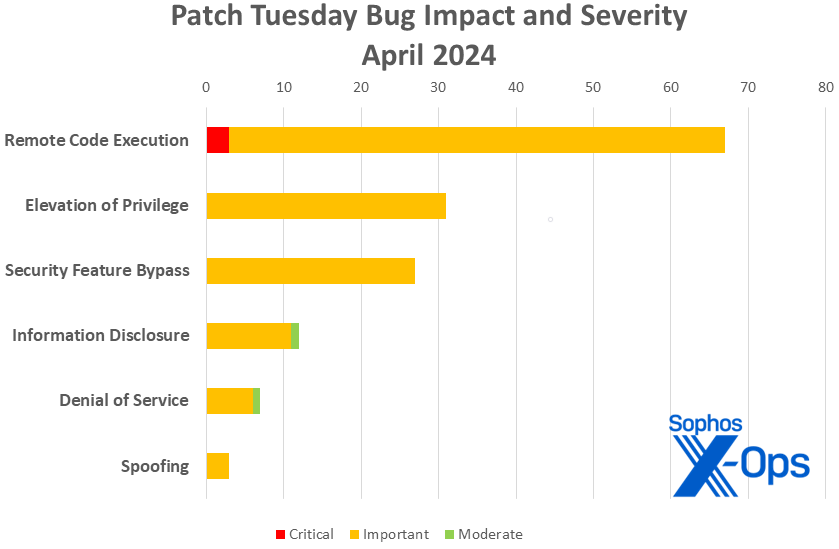
- Impact
- Remote Code Execution: 67
- Elevation of Privilege: 31
- Security Feature Bypass: 27
- Information Disclosure: 12
- Denial of Service: 7
- Spoofing: 3
Figure 1: RCEs came roaring to the forefront this month, but Security Feature Bypass makes a formidable showing (more on that in a bit)
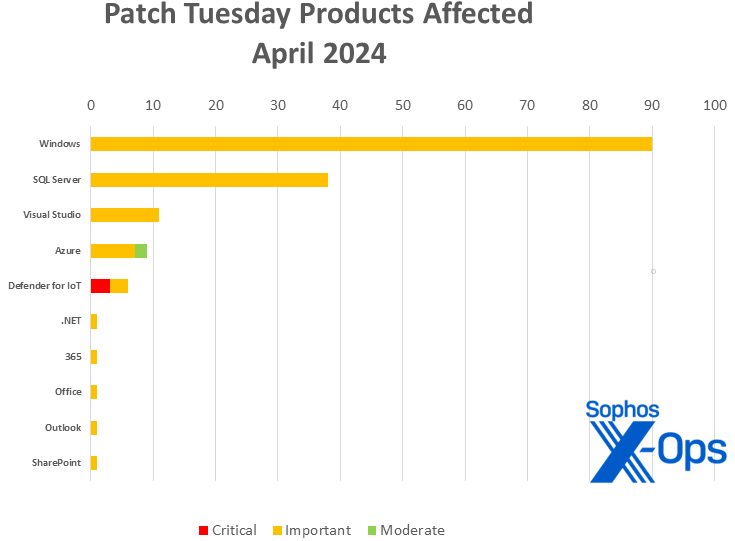
Products
- Windows: 90
- SQL Server: 38 (including 10 shared with Visual Studio)
- Visual Studio: 11 (including 10 shared with SQL Server and one shared with .NET)
- Azure: 9
- Defender for IoT: 6
- .NET: 1 (shared with Visual Studio)
- 365: 1 (shared with Office)
- Office: 1 (shared with 365)
- Outlook: 1
- SharePoint: 1
Figure 2: Windows accounts for just under two-thirds of the April 2024 patches, with nine other product families also in the mix (but five of those receiving just one patch)
Notable April updates and themes
In addition to the issues discussed above, a few specific items merit attention.
Startup Issues Stack Up
Secure Boot Security Feature Bypass Vulnerability – 24 patches
BitLocker Security Feature Bypass Vulnerability – 1 patch
Lenovo: CVE-2024-23593 Zero Out Boot Manager and drop to UEFI Shell – 1 patch
Lenovo: CVE-2024-23594 Stack Buffer Overflow in LenovoBT.efi – 1 patch
Secure Boot and BitLocker are having an interesting month. All 25 Microsoft patches are important-severity issues. Microsoft says that none of them are currently under active exploitation and that they believe exploitation is less likely in the 30 days after release. The two issues from Lenovo are likewise related to boot processes, are characterized by Microsoft as important-severity Security Feature Bypass faults and are thought to be less likely to be exploited within the next 30 days. (It should be noted that Microsoft mentions the Lenovo releases simply as advisory information.)
CVE-2024-26234 – Proxy Driver Spoofing Vulnerability
As mentioned above, back in December, Sophos X-Ops opened an investigation of a suspicious-looking executable that claimed to be signed by a valid Microsoft Hardware Publisher Certificate. You can read about what happened next in our writeup of what we discovered. For Microsoft’s part, the company has added the relevant files to its rolling revocation list, which is updated in this patch cycle under this CVE. It is the sole issue this month that is considered to be publicly disclosed.
A Tough Month for SQL Server
Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability – 13 patches
Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability – 24 patches
Microsoft WDAC OLE DB Provider for SQL Server Remote Code Execution Vulnerability – 3 patches
Microsoft WDAC SQL Server ODBC Driver Remote Code Execution Vulnerability – 1 patch
These 41 patches are all important-severity issues with CVE numbers likely assigned from Microsoft’s CAN block (almost all of them are sequential, which usually indicates that they were drawn from the same block at about the same time). Microsoft says that none of them are currently under active exploitation and that they believe exploitation is less likely in the 30 days after release.
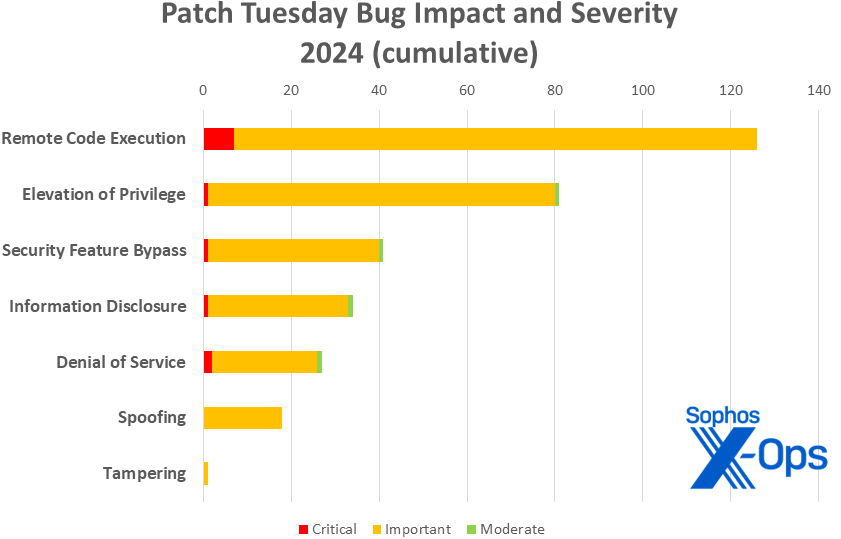
Figure 3: Security Feature Bypass leaps to third place in the cumulative patch totals for 2024, though RCE still leads the pack
Sophos protections
| CVE | Sophos Intercept X/Endpoint IPS | Sophos XGS Firewall |
| CVE-2024-26209 | Exp/2426209-A | Exp/2426209-A |
| CVE-2024-26211 | Exp/2426211-A | Exp/2426211-A |
| CVE-2024-26212 | Exp/2426212-A | sid:2309495 |
| CVE-2024-26218 | Exp/2426218-A | Exp/2426218-A |
| CVE-2024-26230 | Exp/2426230-A | Exp/2426230-A |
| CVE-2024-26234 | Mal/Proxcat-A | N/A |
As you can every month, if you don’t want to wait for your system to pull down Microsoft’s updates itself, you can download them manually from the Windows Update Catalog website. Run the winver.exe tool to determine which build of Windows 10 or 11 you’re running, then download the Cumulative Update package for your specific system’s architecture and build number.
Appendix A: Vulnerability Impact and Severity
This is a list of April patches sorted by impact, then sub-sorted by severity. Each list is further arranged by CVE. In an effort to keep our readers informed, we also provide CVSS base and temp scores as those become available, since those may differ from Microsoft’s self-assessments.
Remote Code Execution (68 CVEs)
| Critical severity | |
| CVE-2024-21322 | Microsoft Defender for IoT Remote Code Execution Vulnerability |
| CVE-2024-21323 | Microsoft Defender for IoT Remote Code Execution Vulnerability |
| CVE-2024-29053 | Microsoft Defender for IoT Remote Code Execution Vulnerability |
| Important severity | |
| CVE-2024-20678 | Remote Procedure Call Runtime Remote Code Execution Vulnerability |
| CVE-2024-21409 | .NET, .NET Framework, and Visual Studio Remote Code Execution Vulnerability |
| CVE-2024-26179 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability |
| CVE-2024-26193 | Azure Migrate Remote Code Execution Vulnerability |
| CVE-2024-26195 | DHCP Server Service Remote Code Execution Vulnerability |
| CVE-2024-26200 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability |
| CVE-2024-26202 | DHCP Server Service Remote Code Execution Vulnerability |
| CVE-2024-26205 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability |
| CVE-2024-26208 | Microsoft Message Queuing (MSMQ) Remote Code Execution Vulnerability |
| CVE-2024-26210 | Microsoft WDAC OLE DB Provider for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-26214 | Microsoft WDAC SQL Server ODBC Driver Remote Code Execution Vulnerability |
| CVE-2024-26221 | Windows DNS Server Remote Code Execution Vulnerability |
| CVE-2024-26222 | Windows DNS Server Remote Code Execution Vulnerability |
| CVE-2024-26223 | Windows DNS Server Remote Code Execution Vulnerability |
| CVE-2024-26224 | Windows DNS Server Remote Code Execution Vulnerability |
| CVE-2024-26227 | Windows DNS Server Remote Code Execution Vulnerability |
| CVE-2024-26231 | Windows DNS Server Remote Code Execution Vulnerability |
| CVE-2024-26232 | Microsoft Message Queuing (MSMQ) Remote Code Execution Vulnerability |
| CVE-2024-26233 | Windows DNS Server Remote Code Execution Vulnerability |
| CVE-2024-26244 | Microsoft WDAC OLE DB Provider for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-26252 | Windows rndismp6.sys Remote Code Execution Vulnerability |
| CVE-2024-26253 | Windows rndismp6.sys Remote Code Execution Vulnerability |
| CVE-2024-26256 | libarchive Remote Code Execution Vulnerability |
| CVE-2024-26257 | Microsoft Excel Remote Code Execution Vulnerability |
| CVE-2024-28906 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28908 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28909 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28910 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28911 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28912 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28913 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28914 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28915 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28926 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28927 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28929 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28930 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28931 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28932 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28933 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28934 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28935 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28936 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28937 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28938 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28939 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28940 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28941 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28942 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28943 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28944 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28945 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-29043 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-29044 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-29045 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-29046 | Microsoft WDAC OLE DB Provider for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-29047 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-29048 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-29050 | Windows Cryptographic Services Remote Code Execution Vulnerability |
| CVE-2024-29066 | Windows Distributed File System (DFS) Remote Code Execution Vulnerability |
| CVE-2024-29982 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-29983 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-29984 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-29985 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
Elevation of Privilege (31 CVEs)
| Important severity | |
| CVE-2024-20693 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2024-21324 | Microsoft Defender for IoT Elevation of Privilege Vulnerability |
| CVE-2024-21424 | Azure Compute Gallery Elevation of Privilege Vulnerability |
| CVE-2024-21447 | Windows Authentication Elevation of Privilege Vulnerability |
| CVE-2024-26158 | Microsoft Install Service Elevation of Privilege Vulnerability |
| CVE-2024-26211 | Windows Remote Access Connection Manager Elevation of Privilege Vulnerability |
| CVE-2024-26213 | Microsoft Brokering File System Elevation of Privilege Vulnerability |
| CVE-2024-26216 | Windows File Server Resource Management Service Elevation of Privilege Vulnerability |
| CVE-2024-26218 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2024-26229 | Windows CSC Service Elevation of Privilege Vulnerability |
| CVE-2024-26230 | Windows Telephony Server Elevation of Privilege Vulnerability |
| CVE-2024-26235 | Windows Update Stack Elevation of Privilege Vulnerability |
| CVE-2024-26236 | Windows Update Stack Elevation of Privilege Vulnerability |
| CVE-2024-26237 | Windows Defender Credential Guard Elevation of Privilege Vulnerability |
| CVE-2024-26239 | Windows Telephony Server Elevation of Privilege Vulnerability |
| CVE-2024-26241 | Win32k Elevation of Privilege Vulnerability |
| CVE-2024-26242 | Windows Telephony Server Elevation of Privilege Vulnerability |
| CVE-2024-26243 | Windows USB Print Driver Elevation of Privilege Vulnerability |
| CVE-2024-26245 | Windows SMB Elevation of Privilege Vulnerability |
| CVE-2024-26248 | Windows Kerberos Elevation of Privilege Vulnerability |
| CVE-2024-28904 | Microsoft Brokering File System Elevation of Privilege Vulnerability |
| CVE-2024-28905 | Microsoft Brokering File System Elevation of Privilege Vulnerability |
| CVE-2024-28907 | Microsoft Brokering File System Elevation of Privilege Vulnerability |
| CVE-2024-28917 | Azure Arc-enabled Kubernetes Extension Cluster-Scope Elevation of Privilege Vulnerability |
| CVE-2024-29052 | Windows Storage Elevation of Privilege Vulnerability |
| CVE-2024-29054 | Microsoft Defender for IoT Elevation of Privilege Vulnerability |
| CVE-2024-29055 | Microsoft Defender for IoT Elevation of Privilege Vulnerability |
| CVE-2024-29056 | Windows Authentication Elevation of Privilege Vulnerability |
| CVE-2024-29989 | Azure Monitor Agent Elevation of Privilege Vulnerability |
| CVE-2024-29990 | Microsoft Azure Kubernetes Service Confidential Container Elevation of Privilege Vulnerability |
| CVE-2024-29993 | Azure CycleCloud Elevation of Privilege Vulnerability |
Security Feature Bypass (26 CVEs)
| Important severity | |
| CVE-2024-20665 | BitLocker Security Feature Bypass Vulnerability |
| CVE-2024-20669 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-20688 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-20689 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-26168 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-26171 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-26175 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-26180 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-26189 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-26194 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-26228 | Windows Cryptographic Services Security Feature Bypass Vulnerability |
| CVE-2024-26240 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-26250 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-28896 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-28897 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-28898 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-28903 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-28919 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-28920 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-28921 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-28922 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-28923 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-28924 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-28925 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-29061 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-29062 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-29988 | Internet Shortcut Files Security Feature Bypass Vulnerability |
Information Disclosure (12 CVEs)
| Important severity | |
| CVE-2024-26172 | Microsoft DWM Core Library Information Disclosure Vulnerability |
| CVE-2024-26207 | Windows Remote Access Connection Manager Information Disclosure Vulnerability |
| CVE-2024-26209 | Microsoft Local Security Authority Subsystem Service Information Disclosure Vulnerability |
| CVE-2024-26217 | Windows Remote Access Connection Manager Information Disclosure Vulnerability |
| CVE-2024-26220 | Windows Mobile Hotspot Information Disclosure Vulnerability |
| CVE-2024-26226 | Windows Distributed File System (DFS) Information Disclosure Vulnerability |
| CVE-2024-26255 | Windows Remote Access Connection Manager Information Disclosure Vulnerability |
| CVE-2024-28900 | Windows Remote Access Connection Manager Information Disclosure Vulnerability |
| CVE-2024-28901 | Windows Remote Access Connection Manager Information Disclosure Vulnerability |
| CVE-2024-28902 | Windows Remote Access Connection Manager Information Disclosure Vulnerability |
| CVE-2024-29063 | Azure AI Search Information Disclosure Vulnerability |
| CVE-2024-29992 | Azure Identity Library for .NET Information Disclosure Vulnerability |
Denial of Service (7 CVEs)
| Important severity | |
| CVE-2024-26183 | Windows Kerberos Denial of Service Vulnerability |
| CVE-2024-26212 | DHCP Server Service Denial of Service Vulnerability |
| CVE-2024-26215 | DHCP Server Service Denial of Service Vulnerability |
| CVE-2024-26219 | HTTP.sys Denial of Service Vulnerability |
| CVE-2024-26254 | Microsoft Virtual Machine Bus (VMBus) Denial of Service Vulnerability |
| CVE-2024-29064 | Windows Hyper-V Denial of Service Vulnerability |
| Moderate severity | |
| CVE-2024-20685 | Azure Private 5G Core Denial of Service Vulnerability |
Spoofing (3 CVEs)
| Important severity | |
| CVE-2024-20670 | Outlook for Windows Spoofing Vulnerability |
| CVE-2024-26234 | Proxy Driver Spoofing Vulnerability |
| CVE-2024-26251 | Microsoft SharePoint Server Spoofing Vulnerability |
Appendix B: Exploitability
This is a list of the April CVEs already under exploit in the wild, and those judged by Microsoft to be more likely to be exploited in the wild within the first 30 days post-release. The list is arranged by CVE.
| Exploitation detected | |
| CVE-2024-26234 | Proxy Driver Spoofing Vulnerability |
| CVE-2024-28903 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-28921 | Secure Boot Security Feature Bypass Vulnerability |
| Exploitation more likely within the next 30 days | |
| CVE-2024-26158 | Microsoft Install Service Elevation of Privilege Vulnerability |
| CVE-2024-26209 | Microsoft Local Security Authority Subsystem Service Information Disclosure Vulnerability |
| CVE-2024-26211 | Windows Remote Access Connection Manager Elevation of Privilege Vulnerability |
| CVE-2024-26212 | DHCP Server Service Denial of Service Vulnerability |
| CVE-2024-26218 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2024-26230 | Windows Telephony Server Elevation of Privilege Vulnerability |
| CVE-2024-26239 | Windows Telephony Server Elevation of Privilege Vulnerability |
| CVE-2024-26241 | Win32k Elevation of Privilege Vulnerability |
| CVE-2024-26256 | libarchive Remote Code Execution Vulnerability |
| CVE-2024-29056 | Windows Authentication Elevation of Privilege Vulnerability |
| CVE-2024-29988 | Internet Shortcut Files Security Feature Bypass Vulnerability |
Appendix C: Products Affected
This is a list of April’s patches sorted by product family, then sub-sorted by severity. Each list is further arranged by CVE. Patches that are shared among multiple product families are listed multiple times, once for each product family.
Windows (90 CVEs)
| Important severity | |
| CVE-2024-20665 | BitLocker Security Feature Bypass Vulnerability |
| CVE-2024-20669 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-20678 | Remote Procedure Call Runtime Remote Code Execution Vulnerability |
| CVE-2024-20688 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-20689 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-20693 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2024-21447 | Windows Authentication Elevation of Privilege Vulnerability |
| CVE-2024-26158 | Microsoft Install Service Elevation of Privilege Vulnerability |
| CVE-2024-26168 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-26171 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-26172 | Microsoft DWM Core Library Information Disclosure Vulnerability |
| CVE-2024-26175 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-26179 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability |
| CVE-2024-26180 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-26183 | Windows Kerberos Denial of Service Vulnerability |
| CVE-2024-26189 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-26194 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-26195 | DHCP Server Service Remote Code Execution Vulnerability |
| CVE-2024-26200 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability |
| CVE-2024-26202 | DHCP Server Service Remote Code Execution Vulnerability |
| CVE-2024-26205 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability |
| CVE-2024-26207 | Windows Remote Access Connection Manager Information Disclosure Vulnerability |
| CVE-2024-26208 | Microsoft Message Queuing (MSMQ) Remote Code Execution Vulnerability |
| CVE-2024-26209 | Microsoft Local Security Authority Subsystem Service Information Disclosure Vulnerability |
| CVE-2024-26210 | Microsoft WDAC OLE DB Provider for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-26211 | Windows Remote Access Connection Manager Elevation of Privilege Vulnerability |
| CVE-2024-26212 | DHCP Server Service Denial of Service Vulnerability |
| CVE-2024-26213 | Microsoft Brokering File System Elevation of Privilege Vulnerability |
| CVE-2024-26214 | Microsoft WDAC SQL Server ODBC Driver Remote Code Execution Vulnerability |
| CVE-2024-26215 | DHCP Server Service Denial of Service Vulnerability |
| CVE-2024-26216 | Windows File Server Resource Management Service Elevation of Privilege Vulnerability |
| CVE-2024-26217 | Windows Remote Access Connection Manager Information Disclosure Vulnerability |
| CVE-2024-26218 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2024-26219 | HTTP.sys Denial of Service Vulnerability |
| CVE-2024-26220 | Windows Mobile Hotspot Information Disclosure Vulnerability |
| CVE-2024-26221 | Windows DNS Server Remote Code Execution Vulnerability |
| CVE-2024-26222 | Windows DNS Server Remote Code Execution Vulnerability |
| CVE-2024-26223 | Windows DNS Server Remote Code Execution Vulnerability |
| CVE-2024-26224 | Windows DNS Server Remote Code Execution Vulnerability |
| CVE-2024-26226 | Windows Distributed File System (DFS) Information Disclosure Vulnerability |
| CVE-2024-26227 | Windows DNS Server Remote Code Execution Vulnerability |
| CVE-2024-26228 | Windows Cryptographic Services Security Feature Bypass Vulnerability |
| CVE-2024-26229 | Windows CSC Service Elevation of Privilege Vulnerability |
| CVE-2024-26230 | Windows Telephony Server Elevation of Privilege Vulnerability |
| CVE-2024-26231 | Windows DNS Server Remote Code Execution Vulnerability |
| CVE-2024-26232 | Microsoft Message Queuing (MSMQ) Remote Code Execution Vulnerability |
| CVE-2024-26233 | Windows DNS Server Remote Code Execution Vulnerability |
| CVE-2024-26234 | Proxy Driver Spoofing Vulnerability |
| CVE-2024-26235 | Windows Update Stack Elevation of Privilege Vulnerability |
| CVE-2024-26236 | Windows Update Stack Elevation of Privilege Vulnerability |
| CVE-2024-26237 | Windows Defender Credential Guard Elevation of Privilege Vulnerability |
| CVE-2024-26239 | Windows Telephony Server Elevation of Privilege Vulnerability |
| CVE-2024-26240 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-26241 | Win32k Elevation of Privilege Vulnerability |
| CVE-2024-26242 | Windows Telephony Server Elevation of Privilege Vulnerability |
| CVE-2024-26243 | Windows USB Print Driver Elevation of Privilege Vulnerability |
| CVE-2024-26244 | Microsoft WDAC OLE DB Provider for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-26245 | Windows SMB Elevation of Privilege Vulnerability |
| CVE-2024-26248 | Windows Kerberos Elevation of Privilege Vulnerability |
| CVE-2024-26250 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-26252 | Windows rndismp6.sys Remote Code Execution Vulnerability |
| CVE-2024-26253 | Windows rndismp6.sys Remote Code Execution Vulnerability |
| CVE-2024-26254 | Microsoft Virtual Machine Bus (VMBus) Denial of Service Vulnerability |
| CVE-2024-26255 | Windows Remote Access Connection Manager Information Disclosure Vulnerability |
| CVE-2024-26256 | libarchive Remote Code Execution Vulnerability |
| CVE-2024-28896 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-28897 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-28898 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-28900 | Windows Remote Access Connection Manager Information Disclosure Vulnerability |
| CVE-2024-28901 | Windows Remote Access Connection Manager Information Disclosure Vulnerability |
| CVE-2024-28902 | Windows Remote Access Connection Manager Information Disclosure Vulnerability |
| CVE-2024-28903 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-28904 | Microsoft Brokering File System Elevation of Privilege Vulnerability |
| CVE-2024-28905 | Microsoft Brokering File System Elevation of Privilege Vulnerability |
| CVE-2024-28907 | Microsoft Brokering File System Elevation of Privilege Vulnerability |
| CVE-2024-28919 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-28920 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-28921 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-28922 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-28923 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-28924 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-28925 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-29050 | Windows Cryptographic Services Remote Code Execution Vulnerability |
| CVE-2024-29052 | Windows Storage Elevation of Privilege Vulnerability |
| CVE-2024-29056 | Windows Authentication Elevation of Privilege Vulnerability |
| CVE-2024-29061 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-29062 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2024-29064 | Windows Hyper-V Denial of Service Vulnerability |
| CVE-2024-29066 | Windows Distributed File System (DFS) Remote Code Execution Vulnerability |
| CVE-2024-29988 | Internet Shortcut Files Security Feature Bypass Vulnerability |
SQL Server (38 CVEs)
| Important severity | |
| CVE-2024-28906 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28908 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28909 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28910 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28911 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28912 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28913 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28914 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28915 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28926 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28927 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28929 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28930 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28931 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28932 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28933 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28934 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28935 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28936 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28937 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28938 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28939 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28940 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28941 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28942 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28943 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28944 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28945 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-29043 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-29044 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-29045 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-29046 | Microsoft WDAC OLE DB Provider for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-29047 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-29048 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-29982 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-29983 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-29984 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-29985 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability |
Visual Studio (11 CVEs)
| Important severity | |
| CVE-2024-21409 | .NET, .NET Framework, and Visual Studio Remote Code Execution Vulnerability |
| CVE-2024-28929 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28930 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28931 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28932 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28933 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28934 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28935 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28936 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28937 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-28938 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability |
Azure (9 CVEs)
| Important severity | |
| CVE-2024-21424 | Azure Compute Gallery Elevation of Privilege Vulnerability |
| CVE-2024-26193 | Azure Migrate Remote Code Execution Vulnerability |
| CVE-2024-28917 | Azure Arc-enabled Kubernetes Extension Cluster-Scope Elevation of Privilege Vulnerability |
| CVE-2024-29063 | Azure AI Search Information Disclosure Vulnerability |
| CVE-2024-29989 | Azure Monitor Agent Elevation of Privilege Vulnerability |
| CVE-2024-29990 | Microsoft Azure Kubernetes Service Confidential Container Elevation of Privilege Vulnerability |
| CVE-2024-29993 | Azure CycleCloud Elevation of Privilege Vulnerability |
| Moderate severity | |
| CVE-2024-20685 | Azure Private 5G Core Denial of Service Vulnerability |
| CVE-2024-29992 | Azure Identity Library for .NET Information Disclosure Vulnerability |
Defender (6 CVEs)
| Critical severity | |
| CVE-2024-21322 | Microsoft Defender for IoT Remote Code Execution Vulnerability |
| CVE-2024-21323 | Microsoft Defender for IoT Remote Code Execution Vulnerability |
| CVE-2024-29053 | Microsoft Defender for IoT Remote Code Execution Vulnerability |
| Important severity | |
| CVE-2024-21324 | Microsoft Defender for IoT Elevation of Privilege Vulnerability |
| CVE-2024-29054 | Microsoft Defender for IoT Elevation of Privilege Vulnerability |
| CVE-2024-29055 | Microsoft Defender for IoT Elevation of Privilege Vulnerability |
.NET (1 CVE)
| Important severity | |
| CVE-2024-21409 | .NET, .NET Framework, and Visual Studio Remote Code Execution Vulnerability |
365 (1 CVE)
| Important severity | |
| CVE-2024-26257 | Microsoft Excel Remote Code Execution Vulnerability |
Office (1 CVE)
| Important severity | |
| CVE-2024-26257 | Microsoft Excel Remote Code Execution Vulnerability |
Outlook (1 CVE)
| Important severity | |
| CVE-2024-20670 | Outlook for Windows Spoofing Vulnerability |
SharePoint (1 CVE)
| Important severity | |
| CVE-2024-26251 | Microsoft SharePoint Server Spoofing Vulnerability |
Appendix D: Advisories and Other Products
This is a list of advisories and information on other relevant CVEs in the April Microsoft release, sorted by product.
Relevant to Edge / Chromium (5 CVEs)
| CVE-2024-3156 | Chromium: CVE-2024-3156 Inappropriate implementation in V8 |
| CVE-2024-3158 | Chromium: CVE-2024-3158 Use after free in Bookmarks |
| CVE-2024-3159 | Chromium: CVE-2024-3159 Out of bounds memory access in V8 |
| CVE-2024-29049 | Microsoft Edge (Chromium-based) Webview2 Spoofing Vulnerability |
| CVE-2024-29981 | Microsoft Edge (Chromium-based) Spoofing Vulnerability |
Relevant to Windows (non-Microsoft release) (5 CVEs)
| CVE-2019-3816 | Red Hat: <unnamed CBL Mariner path transversal issue> |
| CVE-2019-3833 | Red Hat: <unnamed CBL Mariner infinite loop issue> |
| CVE-2024-2201 | Intel: CVE-2024-2201 Side Channel Execution |
| CVE-2024-23593 | Lenovo: CVE-2024-23593 Zero Out Boot Manager and drop to UEFI Shell |
| CVE-2024-23594 | Lenovo: CVE-2024-23594 Stack Buffer Overflow in LenovoBT.efi |
Other
| ADV990001 | Latest Servicing Stack Updates |