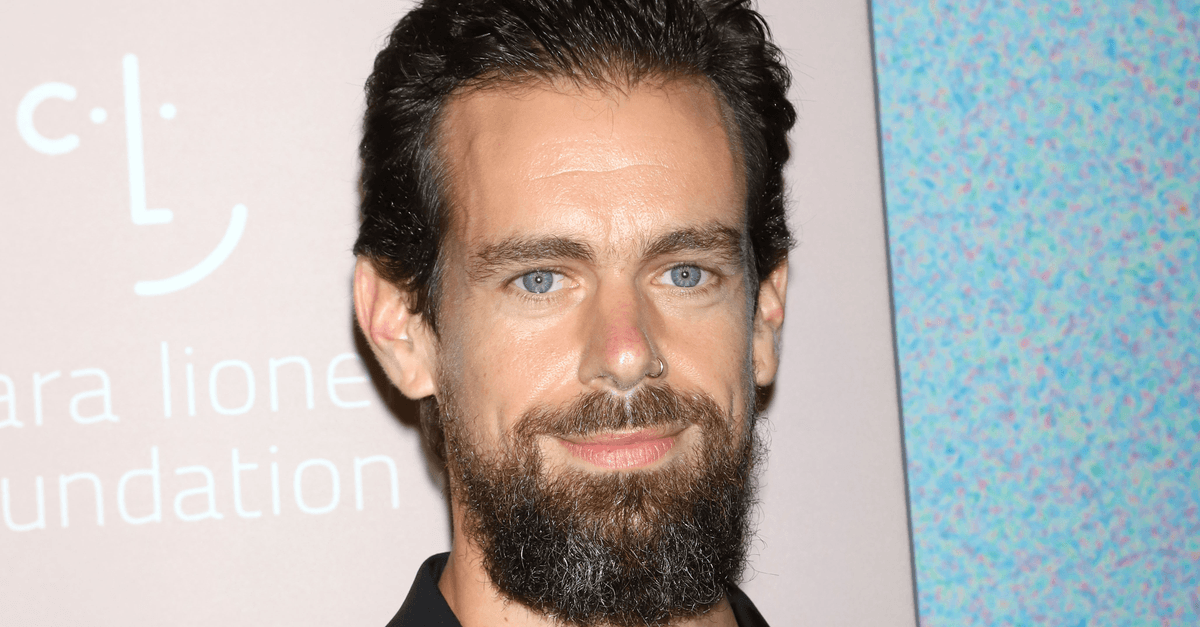
Police have arrested an alleged member of The Chuckling Squad: the hacking group behind the recent SIM-swap and hijacking of Twitter founder and CEO Jack Dorsey’s @Jack account.
Joseph Cox, writing for Motherboard, reported on Saturday that a Chuckling Squad leader – who goes by the handle Debug – told them that the individual was arrested about two weeks prior. Motherboard withheld their name, because they’re a minor.
Debug told Motherboard that the minor – whom they identified as a “he” – was a SIM-swapping aficionado whom the group kicked out in October:
He was a member of Chuckling Squad but not anymore. He was an active member for us by providing celebs/public figure [phone] numbers and helped us hack them.
The arrest was confirmed by the Santa Clara County District Attorney’s Office in California, which manages the Regional Enforcement Allied Computer Team (REACT) and which emailed this statement to Motherboard:
We applaud the efforts of all the law enforcement agencies involved in this arrest. REACT continues to work with and assist our law enforcement partners in any way we can. We hope this arrest serves as a reminder to the public that people who engage in these crimes will be caught, arrested and prosecuted.
Dorsey’s high-profile, high-value account – he’s got more than 4 million followers – was taken over in late August 2019 by hackers who used their brief access to go on a joyride to Nasty Town, tweeting out a racist/anti-semitic/bomb-hoaxing exhaust cloud.
A week later, Twitter temporarily yanked the ability to tweet via SMS – one of the possible ways that Dorsey’s account got taken over.
In a successful SIM-swap attack, hackers persuade a mobile phone provider to transfer a victim’s phone number to the hacker’s SIM card, giving the hacker access to the victim’s calls and messages.
At the time, Twitter said that it was suspending the ability to tweet via text due to vulnerabilities that mobile carriers need to address, and due to its reliance on having a linked phone number for two-factor authentication (2FA) – something it said it’s working to improve.
It’s not too surprising to hear that the arrested, alleged Chuckling Squad member who allegedly helped take over @Jack was a minor, given that celebrity account takeovers – unless they involved a ransom demand – aren’t necessarily worth big bucks.
Rather, they’re about lulz and/or bragging rights. Here’s Debug again, speaking about the former Chuckling Squadder who got arrested:
He would be weird. Swatting celebrities for a follow back.
But SIM-swap attacks are also big business, with hacking groups going after high rollers in the cryptocurrency scene, taking over their accounts so they can clean out their victims’ wallets.
Debug told Motherboard that the arrested kid was also allegedly behind other attacks, including one on Santa Clara County Deputy District Attorney Erin West. The hacker sent over a screenshot of a text message they said the individual sent to West, which included the hashtag “#FreeJoelOrtiz” – a reference to a SIM-swapper that West convicted.
Ortiz was one of two alleged SIM swappers busted last week for draining fat cryptocurrency wallets and hijacking high-value (“OG,” or “original gangster”) social media accounts. Accused of stealing more than $5 million in Bitcoin, Ortiz copped a plea and was sentenced to 10 years in prison.
How it’s done
As we’ve explained, SIM-swap fraud, also known as phone-porting fraud, works because phone numbers are actually tied to the phone’s SIM card – in fact, SIM is short for subscriber identity module, a special system-on-a-chip card that securely stores the cryptographic secret that identifies your phone number to the network.
Most mobile phone shops out there can issue and activate replacement SIM cards quickly, causing your old SIM to go dead and the new SIM card to take over your phone number… and your telephonic identity.
That comes in handy when you get a new phone or lose your phone: your phone carrier will be happy to sell you a new phone, with a new SIM, that has your old number.
But if a SIM-swap scammer can get enough information about you, they can just pretend they’re you and then social-engineer that swap of your phone number to a new SIM card that’s under their control.
By stealing your phone number, the crooks start receiving your text messages along with your phone calls, and if you’ve set up SMS-based two-factor authentication (2FA), the crooks now have access to your 2FA codes – at least, until you notice that your phone has gone dead, and manage to convince your account providers that somebody else has hijacked your account.
Of course, it takes time to discover that you’ve been SIM-swapped, and it takes time to notify your provider and explain it all. Crooks take advantage of that lag time to rifle through your accounts. Doing so gives them the ability to do many things, none of them good. We recently saw a victim who had his sex tapes whisked out from under him – after which the crook tried to sextort him, threatening to release the material if he didn’t pay up. We’ve seen bank account balances melt, and we’ve seen Bitcoin wallets drained.
What to do?
Here’s our advice on how to avoid a SIM swap:
- Set up a PIN or password on your cellular account. This could help protect your account from crooks trying to make unauthorized changes. Check your provider’s website for instructions on how to do it, or just call so they can walk you through it.
- Real companies don’t ask for passwords or verification codes. If somebody calls, says they’re one of your financial companies or your phone service provider, and asks for your password or verification code, get off that call: they’re a scammer. If you need to talk to your cellular provider or financial institution, look up the phone number, on the back of your card or on a legitimate website, and call them yourself.
- Watch out for phishing emails or fake websites that crooks use to acquire your usernames and passwords in the first place. Generally speaking, SIM-swap crooks need access to your text messages as a last step, meaning that they’ve already figured out your account number, username, password and so on.
- Avoid obvious answers to account security questions. Consider using a password manager to generate absurd and unguessable answers to the sort of questions that crooks might otherwise work out from your social media accounts. The crooks might guess that your first car was a Toyota, but they’re much less likely to figure out that it was a
87X4TNETENNBA. - Use an on-access (real-time) anti-virus and keep it up-to-date. One common way for crooks to figure out usernames and passwords is by means of keylogger malware, which lies low until you visit specific web pages such as your bank’s login page, then springs into action to record what you type while you’re logging on. A good real-time anti-virus will help you to block dangerous web links, infected email attachments and malicious downloads.
- Be suspicious if your phone drops back to “emergency calls only” unexpectedly. Check with friends or colleagues on the same network to see if they’re also having problems. If you need to, borrow a friend’s phone to contact your mobile provider to ask for help. Be prepared to attend a shop or service center in person if you can, and take ID and other evidence with you to back yourself up.
- Consider switching from SMS-based 2FA codes to codes generated by an authenticator app. This means the crooks have to steal your phone and figure out your lock code in order to access the app that generates your unique sequence of login codes.
Having said that, Naked Security’s Paul Ducklin advises that we shouldn’t think of switching from SMS to app-based authentication as a panacea:
Malware on your phone may be able to coerce the authenticator app into generating the next token without you realizing it – and canny scammers may even phone you up and try to trick you into reading out your next logon code, often pretending they’re doing some sort of “fraud check”.
If you’ve already been SIM-jacked…
- Contact your cellular service provider immediately to take back control of your phone number. Then, change your account passwords.
- Check your credit card, bank, and other financial statements for unauthorized charges or changes. If you see any, report them.
- If you think somebody’s already got your information, such as your taxpayer ID or the number of your payment card number or bank account, people in the US can go to IdentityTheft.gov for specific steps to take. If you’re in the UK, check out tips and resources from the Information Commissioner’s Office (ICO) and/or Action Fraud.
LEARN MORE ABOUT HOW SIM SWAPS WORK
Twitter hack section starts at 31’07, SIM swapping at 33’00”.
Click-and-drag on the soundwaves below to skip to any point in the podcast.
Audio player above not working? Download MP3, listen on Soundcloud or on Apple Podcasts, or access via Spotify.
cdoggyd
Convenient that Chuckling Squad no longer claims him as a member now that he’s been caught.
Anonymous
I know must cell phone companies in the United States will call customer service if you dial 611 on the cell phone. But what I find interesting about this, a very large cell phone company in the US has started to send text messages to customers when you dial the customer service line as a “verification” step, then ask you for the contents of that verification text. I guess they didn’t get the memo on the second recommendation!
Laurence Marks
No, this verification scheme does work. The code is sent BEFORE the sim-swap is allowed. It goes to the victim’s phone, not the perpetrator’s phone,