(Edited July 27, 2022 to add: Since we posted this, Microsoft has identified a private-sector offensive actor, called “Knotweed,” using CVE-2022-22047 in targeted attacks. Customers are encouraged to expedite deployment of the July 2022 Microsoft security updates to protect their systems against exploits using CVE-2022-22047.)
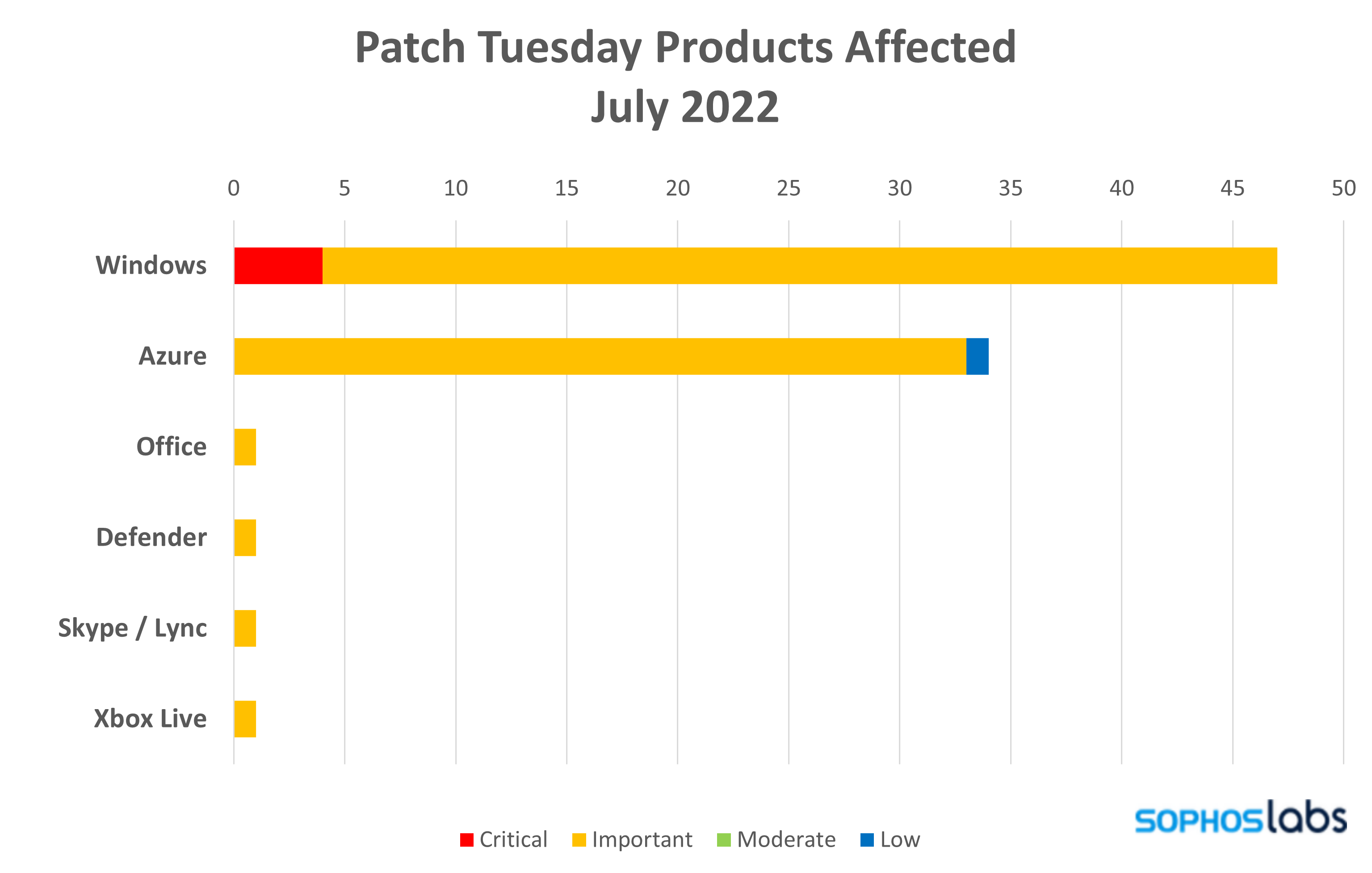
Microsoft on Tuesday released patches for 85 vulnerabilities in six Microsoft product families. All but six of those are rated Important in severity, and once again the majority (47) affect Windows. Azure makes up the lion’s share of the remainder with 34 patches in queue, with Edge, Office, Defender, and Xbox Live each receiving one update apiece. Three of the included Important-severity information-disclosure patches actually hail from third parties – two from AMD, one from HackerOne. One Important-class Elevation of Privilege issue, affecting Windows, is currently under active exploit in the wild. One advisory, with connections to Redmond’s long-awaited Windows Autopatch function, is also included in this month’s collection.
There are only four Critical-class vulnerabilities this month, all for Windows, all listed as less likely to be exploited. The sole issue identified as actually under exploit, CVE-2022-22047, affects Client/Server Runtime Subsystem Service (CSRSS); it’s described as an Important-class Elevation of Privilege issue of potentially low attack complexity, requiring low privileges and no user interaction, and affecting both client and server installations. As such, administrators should consider this issue to be worth addressing sooner rather than later.
The two AMD-originated patches are both connected to the chip manufacturer’s own AMD-SB-1037 bulletin, also issued Tuesday. That bulletin addresses Retbleed, a speculative execution attack affecting certain AMD and Intel processors. Retbleed is in turn a variation on a Spectre microarchitectural timing side-channel attack. Retbleed exploits a security defense called retponline, which was developed to counter Spectre-type attacks, but which has been known to be potentially vulnerable to this sort of attack for years. (Intel, also vulnerable, is releasing advisory information this week as well. Microsoft’s patches today do not include that information.)
Aside from the sheer volume of Azure patches, a few issues addressed in July stand out just because Black Hat is on the horizon. Among various researchers regularly reporting issues to Microsoft, Devcore’s Cheng-Da “Orange” Tsai, who earlier this year disclosed the series of Exchange vulnerabilities that became ProxyLogon, is credited with three Important-severity IIS finds in this month’s patch collection. He’ll be speaking on destabilizing IIS’ hash table at next month’s conference.
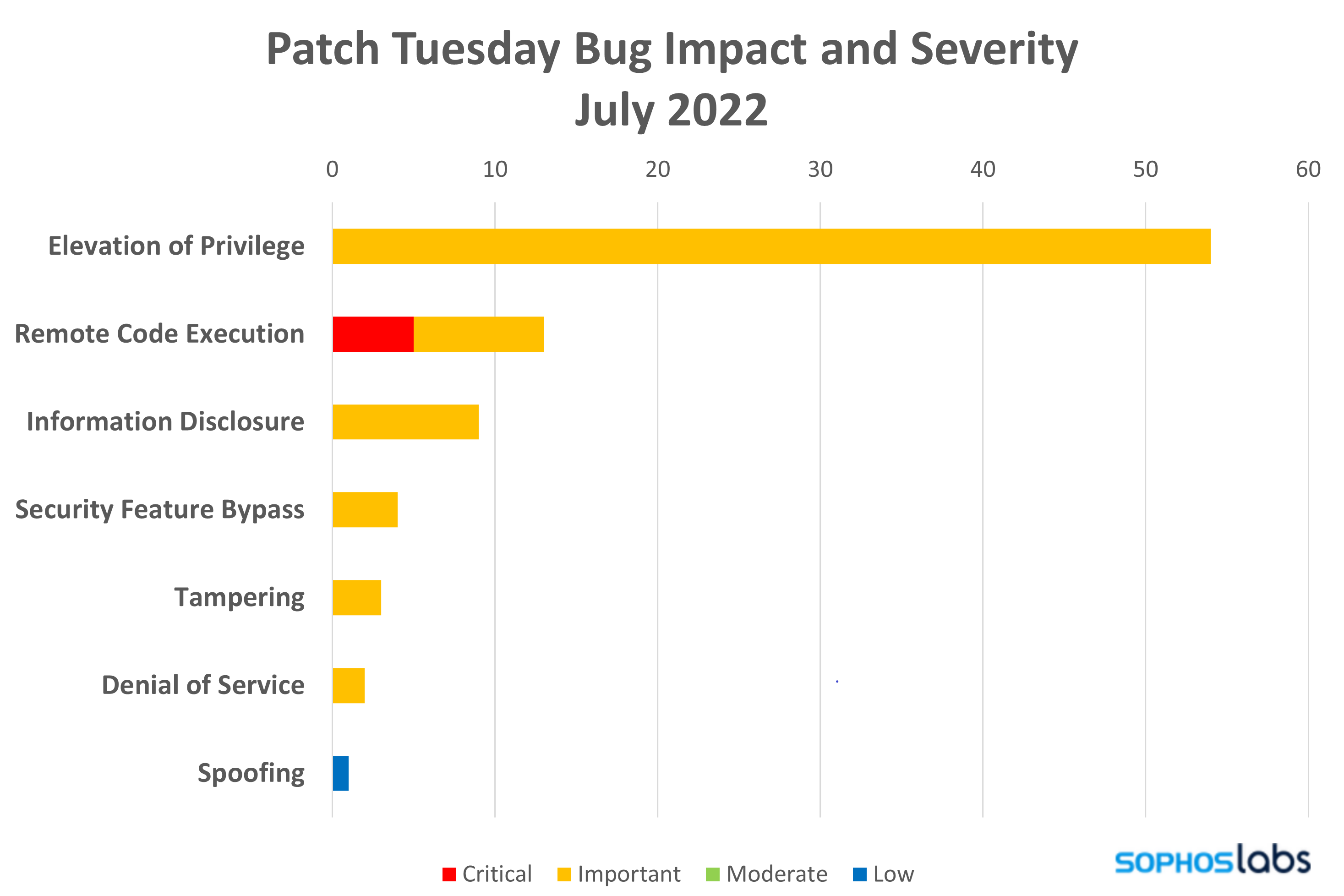
By the Numbers
- Total Microsoft CVEs: 82
- Total third-party CVEs also shipping in update: 3
- Publicly disclosed: 0
- Publicly exploited: 1
- Exploitation detected: 1 (both older and newer product versions)
- Exploitation more likely: 5 (both older and newer product versions)
- Severity
- Critical: 4
- Important: 80
- Low: 1
- Impact
- Elevation of Privilege: 54
- Remote Code Execution: 12
- Information Disclosure: 9
- Information Disclosure: 9
- Tampering: 3
- Denial of Service: 2
- Spoofing: 1
Figure 1: Important-severity Elevation of Privilege issues compose the vast majority of July’s patches
- Products
- Microsoft Windows: 47
- Azure: 34
- Microsoft Office: 1
- Defender: 1
- Skype / Lync: 1
- Xbox Live: 1
Figure 2: Windows makes up the majority of July’s vulnerabilities, including all four of the Critical-class issues
Notable Vulnerabilities
Windows CSRSS Elevation of Privilege (CVE-2022-22047)
This is one of three elevation of privilege vulnerabilities affecting the Windows Client Server Run-Time Subsystem (CSRSS). All three are described as being of potentially low attack complexity, requiring low privileges and no user interaction and affect both client and server installations. Most importantly, it’s also the only vulnerability called out as being under active exploitation as of time of release. While we have not seen any proof of concept code as of the release and it is rated as “Important”, these factors make this a vulnerability that administrators should address sooner than later and best to address all three CSRSS vulnerabilities at once.
Microsoft Defender for Endpoint Tampering Vulnerability (CVE-2022-33637)
As a class of vulnerability, tampering is represented far more prominently than usual in July, with three issues – two affecting Windows, and one touching only Microsoft Defender for Endpoint for Linux. Successful exploitation of this vulnerability would require an attacker to authenticate to the management console appliance and to have a specific integration token.
BitLocker Security Bypass Feature Vulnerability (CVE-2022-22048)
It has a maximum severity of Important and requires that an attacker have physical attack to the target machine, but this vulnerability is capable of bypassing BitLocker encryption on the machine – even if it’s powered off. Both client and server Windows installations are affected.
Latest Servicing Stack Updates (Advisory ADV990001)
A servicing-stack update makes changes to the component that installs Windows updates as well as to the CBS (component-based servicing stack), another crucial underpinning of the operating system. Generally, such updates are issued in response to a newly discovered issue or vulnerability, though in this case the more likely scenario involves the release of Microsoft’s Windows Autopatch feature. Since the ability to install other security patches may be predicated on whether the servicing stack is up to date, we suggest that administrators make ADV990001 a priority. (Microsoft offers an overview of servicing stack updates for those unfamiliar with this infrequently updated component.)
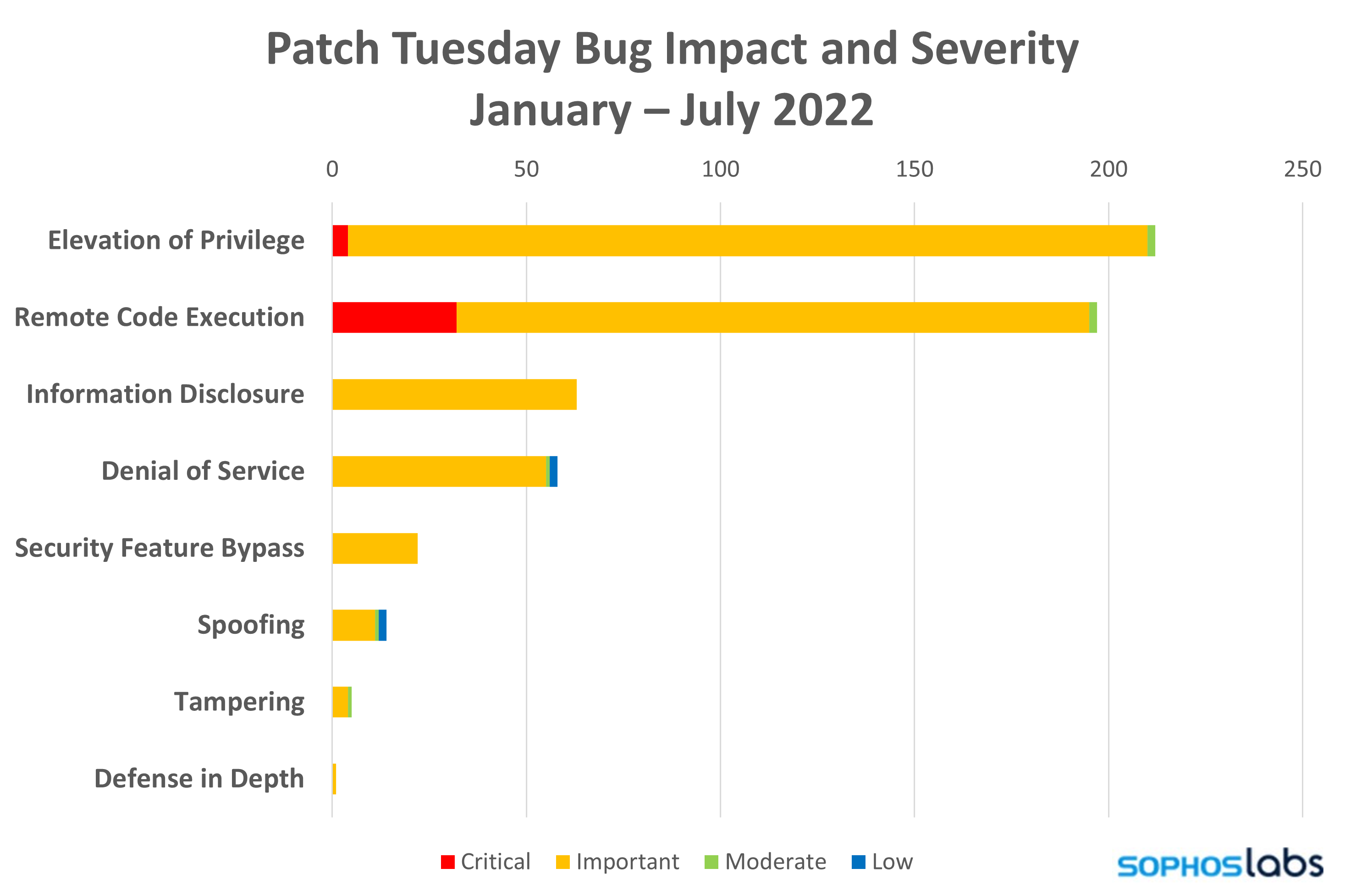
Figure 3: July’s preponderance of Elevation of Privilege issues bring 2022’s EoP count slightly ahead of the count for Remote Code Execution vulnerabilities
Sophos protection
|
CVE |
Sophos Intercept X / Endpoint IPS |
Sophos XGS Firewall |
|
CVE-2022-22047 |
Exp/2222047-A |
|
|
|
|
|
As you can every month, if you don’t want to wait for your system to pull down the updates itself, you can download them manually from the Windows Update Catalog website. Run the winver.exe tool to determine which build of Windows 10 or 11 you’re running, then download the Cumulative Update package for your particular system’s architecture and build number.

zc
I would like to mention that CVE-2022-30203 can also lead to bitlocker bypass; it’s just obscured in the advisory as “could allow an attacker to access the pre-boot environment” (which allows to dump and potentially derive bitlocker keys).