By Andrew Brandt
It isn’t all that often that the stars align quite this well, but my two passions — information security and hacking my home — came together last week, when I stumbled upon a phishing attack very specifically targeting home improvement tradespeople in the county in which I live. Apparently, this phishing scam has been going on for a while, but I’ve only just come across it.
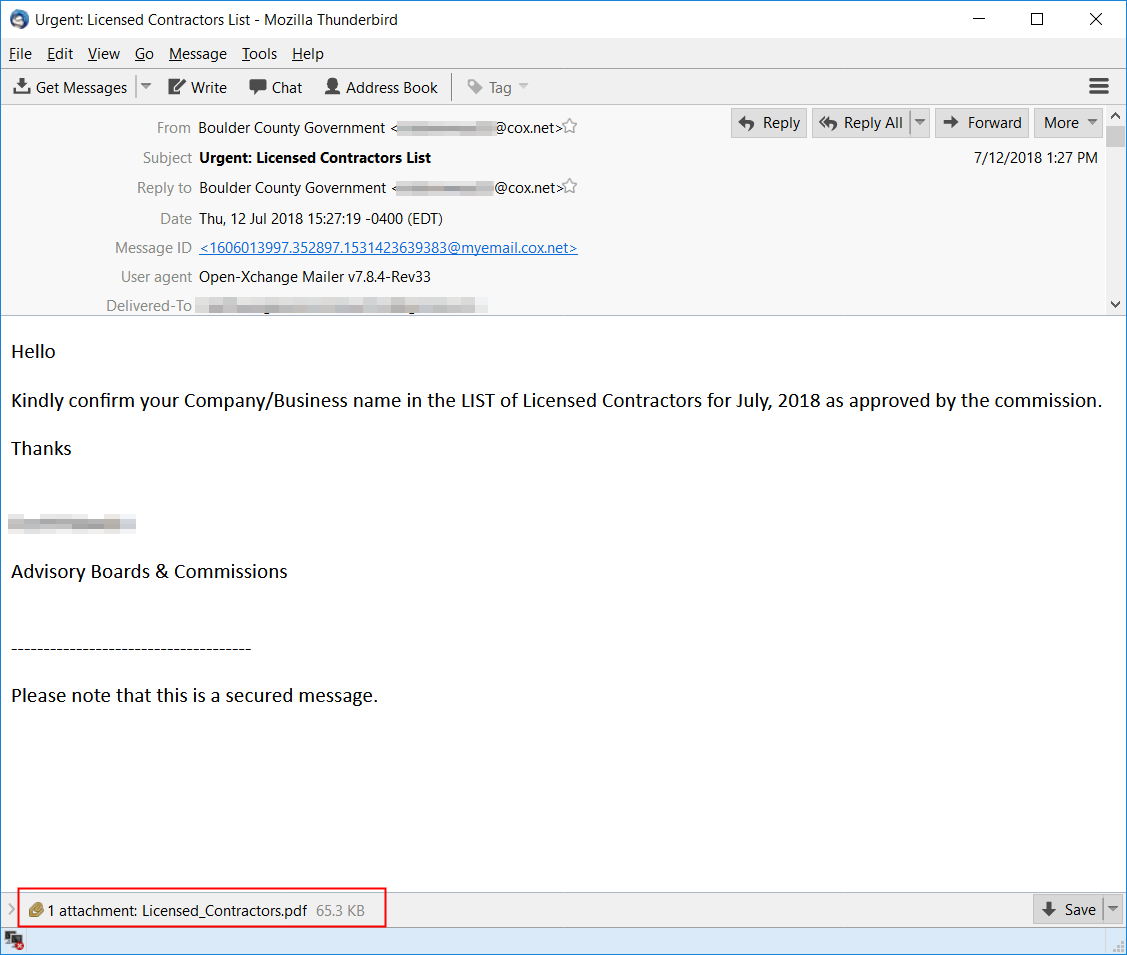
Someone I know who works for a general contractor (GC) sent me a copy of a suspicious email they received on July 12th. The message claims it comes from “Boulder County Government” but uses the personal email address that belongs to an oral surgeon from North Carolina.
The message asks recipients to open an attached PDF document that it claims is a list of licensed building contractors. To lend the message some authenticity, it’s “signed” with the name of a real lawyer who used to serve on a local commission that oversees land use in the county — a person who might have some name recognition to a GC, and who knew nothing about this campaign until we contacted him.
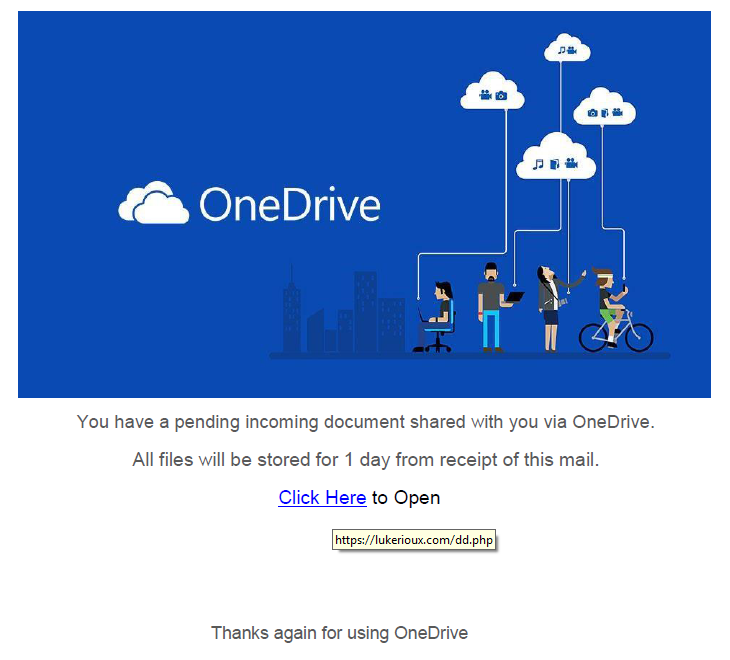
The embedded PDF attachment is a simple document with only a background image that makes it appear the file is stored in Microsoft’s OneDrive cloud storage service, and a link embedded in the page. To urge the recipient to quickly click the link, it claims “All files will be stored for 1 day from receipt of this mail.”
The link in the PDF file leads to a very clean-looking phishing page, hosted on a subdirectory of a (clearly, compromised) Web site that belongs to a criminal defense attorney based in Portland, Maine.
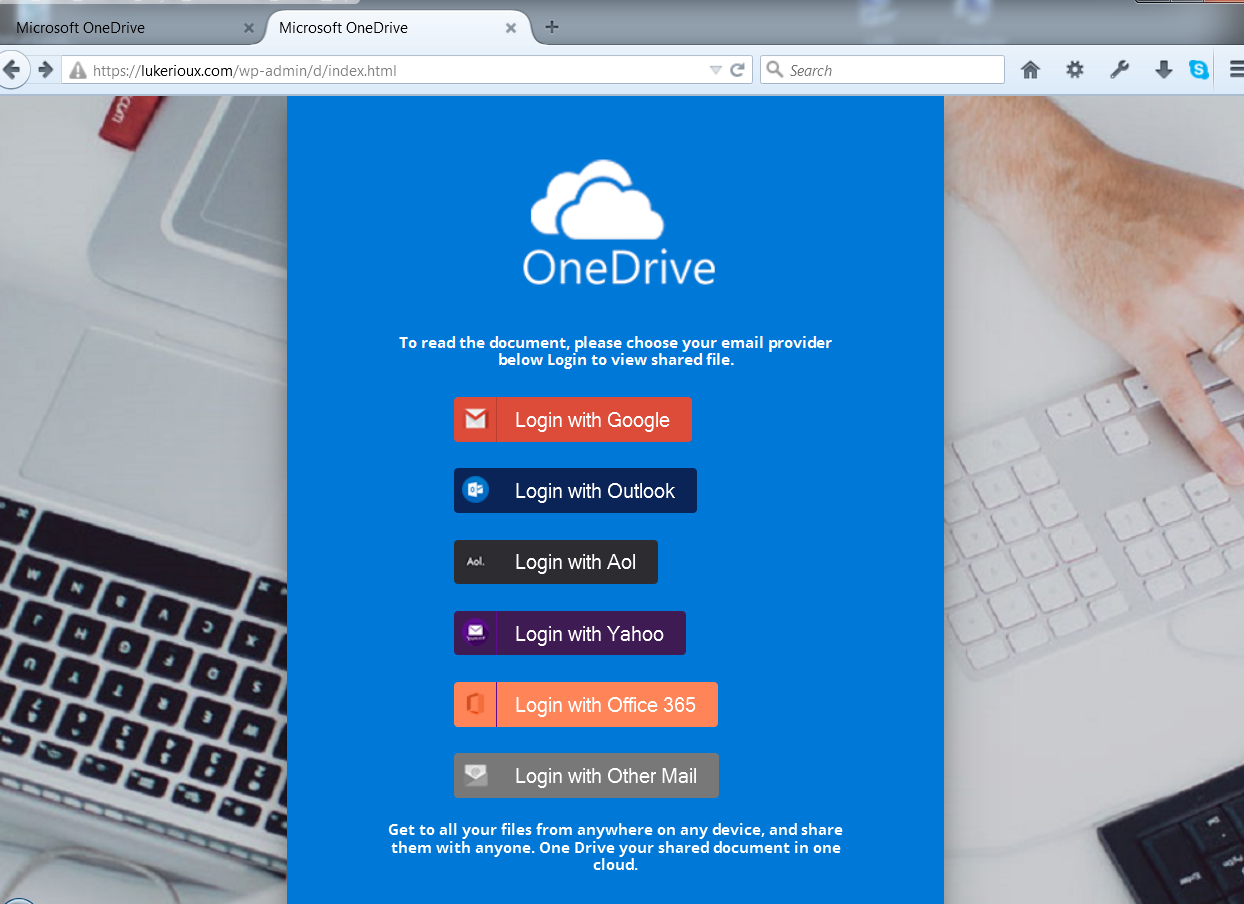
The phishing page prompts recipients to provide their email credentials. It uses a familiar-looking phishing kit that produces a customized login form decorated to look like various webmail providers, such as Google, Outlook, or Yahoo.
In doing a little background work on the email address used in the attack, I stumbled upon what looks like an identical attack that appears to have taken place in March, targeting people in Derbyshire, UK. The Derbyshire Open Arts Twitter account sent out a warning with a screenshot on March 22.

What isn’t clear is how the attackers managed to get a list of the email addresses belonging to GCs and tradespeople in this specific geographic region. One could speculate that the attackers may have breached some organization in possession of such a list of targets, but they could have just as easily Googled for emails. It’s not like builders, plumbers, electricians, or other contractors keep their business addresses a secret.
The Boulder phishing attack looks to have been just as carefully planned. The attacker, in this case, appears to be doing at least some homework about the geographic region they’re targeting, using the name of some local organization, or even the names of individuals from that organization, as part of the social engineering aspect of the attack. The site hosting the phishing page has not been taken down, so it’s possible that people could still become victims.
If you’re a Boulder- or Denver-area contractor or construction tradesperson who received this message, and you think that you might have clicked the link in the PDF, log in to your email account and change your password immediately.

(Actually, knowing the construction folks that I know, I’d recommend that they just change it anyway, right now, to something that meets strong password guidelines).
And if someone you don’t know emails you a PDF that purports to link directly to some sort of cloud storage service, just throw it out. Nothing good ever comes of this.
sheka
I noted that where I lived, stickers of different variety of similar instances were published internationally by attackers just to prove that such could be done. The irony is that nobody notices these anc take fior granted that they are ok.