iPhone aficionados at iDeviceHelp and EverythingApplePro have discovered yet another way for someone who has physical access to your phone to access your messages, photos, and contacts, even if the phone is locked with both a passcode and properly configured TouchID.
EverythingApplePro and iDeviceHelp published full proof-of-concept videos of this bypass on YouTube, in case you’d like to follow along at home.
The demonstration shows the bypass on an iPhone 7 using the iOS 10.2 beta 3, as well as an iPhone 4 using iOS 8 and even on an iPad, showing that this flaw affects any iDevice that can receive Facetime or phone calls.
This is not the first time (by a long shot) that clever iPhone users have found lock screen bypasses to access information that should be locked down, including photos, messages, and contacts. In fact, we’ve been covering flaws like this since at least 2013.
Anyone attempting this bypass needs physical access to your phone – they can’t grab your stuff remotely but if your phone has been stolen or left unattended then this bypass is fairly straightforward.
The hack uses Siri to activate the VoiceOver feature on the target phone while the phone is still locked. Once the target phone receives a call (via Facetime or phone) and the target phone declines the call with a message, the VoiceOver feature can be hijacked to cause unintended behavior in the messaging screen which then allows access to the phone’s contacts, photos, and messages.
Thankfully, as with pretty much all of the iOS lockscreen bypasses we’ve covered, there is an easy way to prevent this from happening: disable Siri access on the lockscreen.
If you can’t use Siri to enable VoiceOver from the lockscreen, this hack (and many others) will not work.
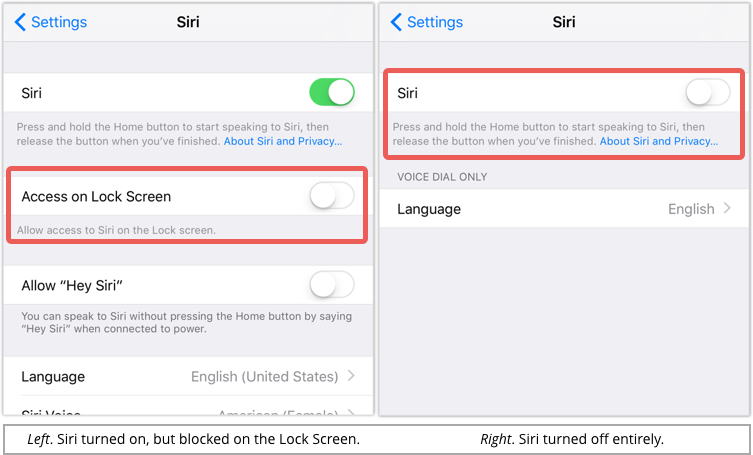
To disable Siri access on the lockscreen, go to the Settings | Siri page.
If Siri is turned on, you will see a slider to turn off Access on Lock Screen.
Alternatively, you can turn off Siri altogether with the Siri slider at the top, in which case the other configuration options will disappear from sight:
Are you concerned about iPhone hacks like this, or are they overblown?
Will you be disabling Siri from your lockscreen, or have you done so already?

Anonymous
Does anyone who reads this blog still have Siri enabled? It is the primary component in many lock screen bypass attacks. I know I have it completely disabled.
Mahhn
It would be appropriate if we could disable Both Siri and Voice Control, preventing this, a prior voice activated hack, and future similar exploits.
It’s very creepy of Apple to not let us disable the microphone from always listening.
(You cannot disable both Voice Control and Siri, only one or the other)
Colin
I almost didn’t check, because I know I’ve disabled Siri, on the lock screen, before. Apparently, some update had turned it on again.
BTW: With iOS 10.0.2, Siri is on the main Settings page, not within General.
Paul Ducklin
Yes, it is. I’ll update that…thanks.
Paul Ducklin
I put in screenshots, too, so you know what to look for.
Anonymous
I disabled Siri Like this some time ago. However, I do appreciate the reminder.
Peter Roe
Sorry Siri we’ve all just been shown
How to bypass security on the iPhone
It’s your last chance I’ve cut you off
So I can secure all my personal stuff
You have always been a joke of an App
And your answers are invariably crap
‘Hey Siri… search for Early Retirement’
Amy P Paxton
Is this how my one year child always manages to call people I haven’t spoken to in years from my locked iPhone 6? Seriously, I cannot figure out how he is doing this. The phone is most definitely locked, with a four digit passcode- and yet every time he manages to get hold of my phone he calls or face times people. It’s terrible! I just checked and I’ve had Siri disabled altogether this whole time.
Anyone on here have any ideas?
Anonymous
Terrible privacy hole.
Anonymous
One thing not mentioned. If you turn off Siri access from the lock screen. You can’t voice dial or ask Siri for directions when you have a bluetooth headset on without unlocking your device. This is especially bad when you are driving and want to call someone. I could not figure out why I had to fumble for my phone, open it and unlock when I was driving and wanted to ask for directions or call using SIri. So having it on is sometimes a good thing.