 Back in 2005, a youngster called Samy Kamkar wrote and unleashed a JavaScript virus on MySpace.
Back in 2005, a youngster called Samy Kamkar wrote and unleashed a JavaScript virus on MySpace.
You probably remember MySpace: back in 2005, it was the the place to be online, making it the place to try out social networking malware.
Assuming, that is, that you hadn’t learned the lesson of Robert Morris, whose Internet Worm of 1988 went sufficiently ballistic to end up in a courtroom conviction for its author.
And that’s what happened when Samy’s virus, dubbed JS/SpaceHero-A, evaded MySpace’s security filters and spread like crazy.
Samy figured out how to booby-trap a MySpace profile posting so that if you viewed it, the booby-trap would be added to your profile, and so on, and so on.
Every time the virus spread to a new profile, it “friended” young Samy Kamkar, who allegedly ended up with over 1,000,000 friends within 24 hours.
At this point MySpace, fixed the hole that allowed the payload to trigger.
In an interview shortly after the worm hit, Samy claims to have been surprised after reaching 200 friends, but worried after 2000 – after all, it wasn’t going to take a lot of detective work for the FBI to find out whodunnit.
A few hours later, at 200,000, he says he “went to Chipotle and ordered myself a burrito,” figuring that was one innocent way to “enjoy whatever freedom I had left.”
In the end, Samy owned up and pleaded guilty, making him a convicted virus writer, but helping him to avoid a custodial sentence.
He ended up paying restitution, getting 90 days of community service and agreeing to three years of control over how and when he used a computer.
He’s still a hacker, though.
A couple of years ago, he followed up on the efforts of some students in New Jersey, who built a Wi-Fi-hacking drone they called (who would have thought?) SkyNET, by building and open-sourcing a drone-hacking drone that he called (who would have thought?) SkyJack.
SkyJack was more targeted that just an airborne warbike, because it would, or so Samy claimed, seek out, hack into, and take over other drones of the same make in real time.
That would give a whole new sort of dual control: instead of a pilot and co-pilot having joint control of one aircraft, the SkyJack pilot got individual control of two drones at the same time.
→ As far as we know, SkyJack was never made viral, so a pwned drone wouldn’t then fly off and seek other drones to co-opt into a SkyJack zombie network. Perhaps Samy figured that piloting two drones at once was enough of a challenge without suddenly finding that you have 17 of the things careering above you in the local park in some kind of aerial lockstep, complete with 16 wailing kids and 16 angry dads bearing down on you, ready to show you what to do with your remote control unit.
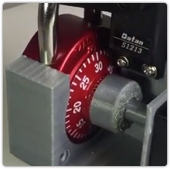
Anyway, Samy’s most recent publication is an open-source 3D-printed robot that can crack a combination lock in just 30 seconds by twiddling the dial all by itself.
We don’t normally feature products that don’t have obvious legitimate uses, but this one seems harmless enough, and it’s quite neatly done, if you’re looking for a cool project to try out at your local Hackerspace or similar.
It only cracks those ultra-budget school locker combination padlocks: the ones that the cool kids used to put on their lockers at school, even though everyone else knew they were much less secure than a keyed lock costing a third of the price.
A quick trawl with a search engine or two will reveal that the standard locker-room combo padlock has a 40-number dial and a hard-wired (unchangeable) three-number combination.
The same search engines will provide you with numerous ways to open such locks without the combination – it seems that the more worn the lock mechanism, the easier it is to “feel” the combination.
So Samy’s robot is more in the way of hacker fun than a criminal hazard.
→ If you were at a school where the other kids used combo locks, you probably already figured out how to heard excitable stories about how to open them. I certainly did. But, then, I also heard an earnestly-repeated warning that if you swallowed chewing gum, it would wrap around your heart and probably be fatal.
The locks we’re talking about here open like this: two spins right past the first number, until you reach it on your third lap; one spin to the left past the first number again, then stop at the second number; then simply turn right to the third number and the lock will open.
Note that the third number is a bit of a red herring.
On expensive combination locks, you have to stop at the the final number, and then reverse the dial one last time to activate the lock mechanism, so all the numbers play an critical part in the combination.
But on the cheap three-spin padlocks, the lock pops open as soon as you reach the last number.
So if you know the first two numbers, you don’t need to remember the third. You just pull down on the lock and spin the dial until the lock opens. (The dial will freeze at the actual number, so you can read it off if you like.)
In effect, the last partial turn to the right to pop open the lock, like the first two spins to the right to prime the mechanism, are just part of the “flagfall”, or operational overhead, of working the lock.
So, the keyspace of 64,000 (40x40x40, or approximately 216) apparent combinations offered by these locks is actually only 1600 (40×40, or less than 211).
That’s ideal for automation with a dedicated Arduino-powered robot like Samy’s, which can slog through the necessary repetitive motions in somewhere between one and two hours, assuming no components in the robot come loose, fall off or burn out.
Samy also figured out a simple way to work out, by feel, the likely first and second numbers, using some arithmetical relationships derived from the operation of the low-cost mechanism used in these budget locks.
His robot can’t do that initial “find by feel” stage, but if you can, it will do the rest, which reduces the cracking time to a mere 8 tries, which it can polish off in just 30 seconds.
Of course, you could just try those eight possible combos yourself, but that’s not why you join a Hackerspace!
