Last month, Sophos X-Ops reported several MDR cases where threat actors exploited a vulnerability in Veeam backup servers. We continue to track the activities of this threat cluster, which recently included deployment of a new ransomware. The vulnerability, CVE-2024-40711, was used as part of a threat activity cluster we named STAC 5881. Attacks leveraged compromised VPN appliances for access and used the VEEAM vulnerability to create a new local administrator account named “point”.
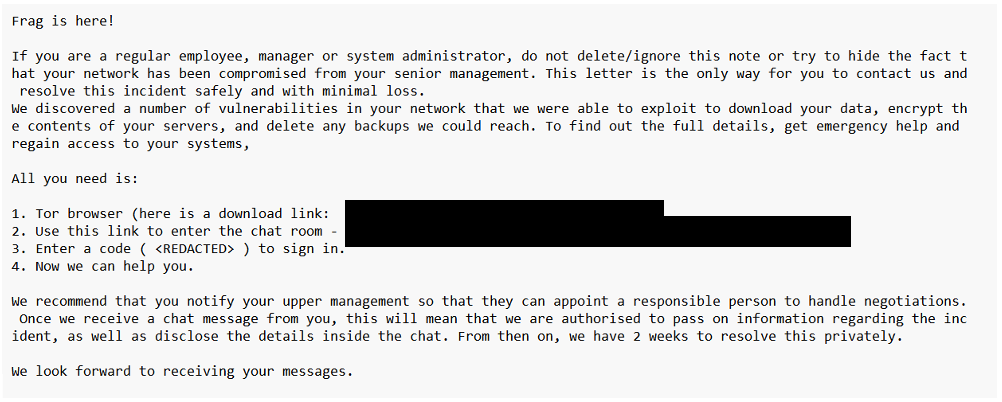
Some cases in this cluster led to the deployment of Akira or Fog ransomware. Akira was first seen in 2023; its leak site was offline briefly in October, but is back online and we continue to see Akira attacks. Fog emerged earlier this year, first seen in May. In a recent case MDR analysts once again observed the tactics associated with STAC 5881 – but this time observed the deployment of a previously-undocumented ransomware called “Frag”.

Similar to the previous events, the threat actor used a compromised VPN appliance for access, leveraged the VEEAM vulnerability, and created a new account named ‘point’.
However in this incident a ‘point2’ account was also created.
Frag is executed on the command line with a number of parameters, with one required: percentage of file encryption. The attacker can specify directories or individual files to encrypt.

When encrypted, files are given a .frag extension. In this case, the ransomware was blocked by Sophos endpoint protection’s CryptoGuard feature. A detection for the ransomware binary has since been added.

The similarity in the tactics, techniques and practices of the actor behind Frag to those used by Akira and Fog threat actors has also been observed by Agger Labs. Sophos X-Ops is closely monitoring this possible emergence of a new ransomware player with behaviors previously seen in Akira ransomware. We will continue to track this threat behavior. We will update this post with more technical details as they become available.